GoldenSpray
Scenario
Reconstruct a multi-stage intrusion timeline by analyzing Windows and Sysmon event logs within Elastic SIEM to identify key attack tactics, techniques, and procedures.
Methodology
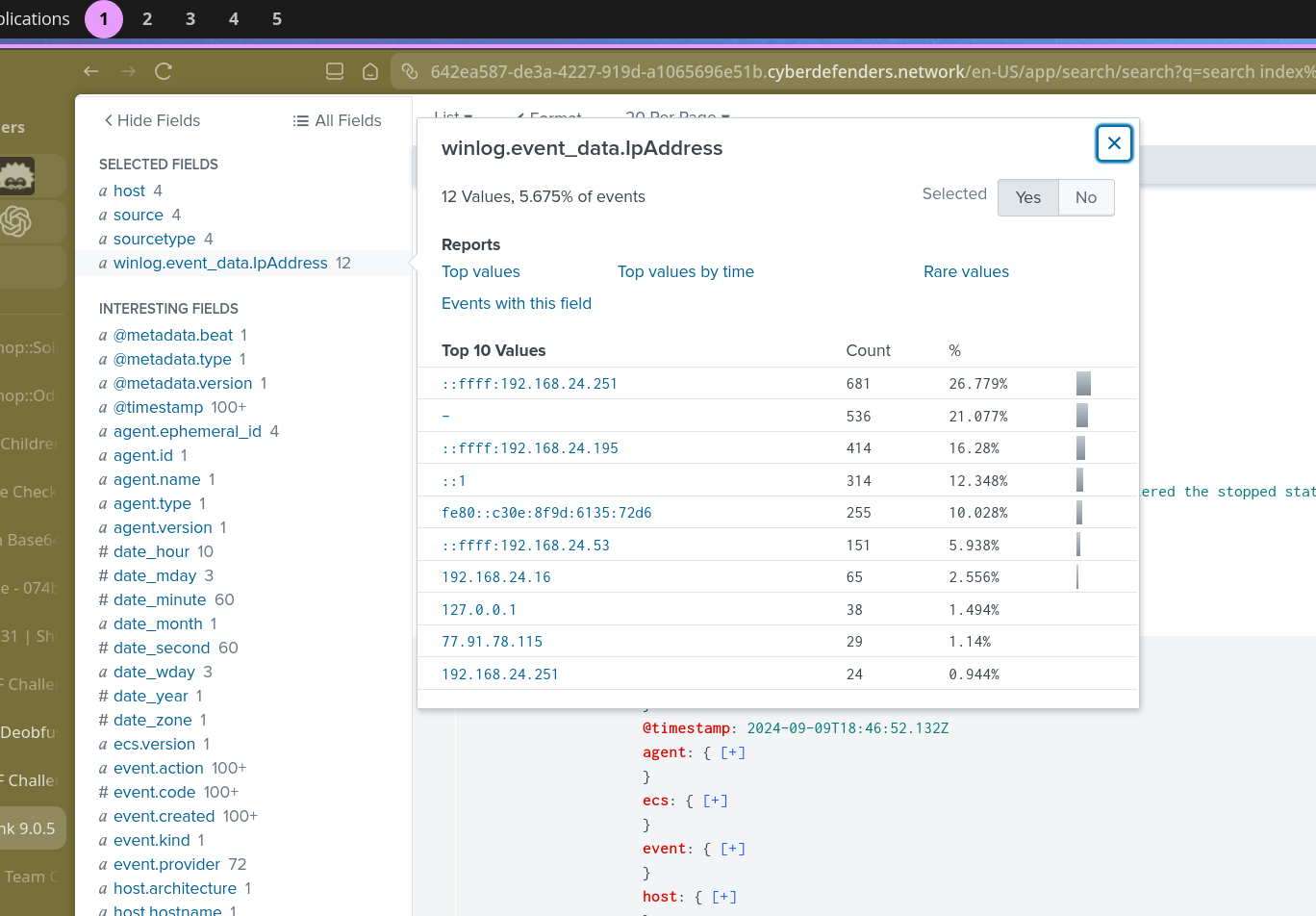
Initial Triage — Attacker IP
The first step is identifying where the attack originated. Adding winlog.event_data.IpAddress as a column and filtering for external IPs surfaces a single non-RFC1918 address:
77.91.78.115
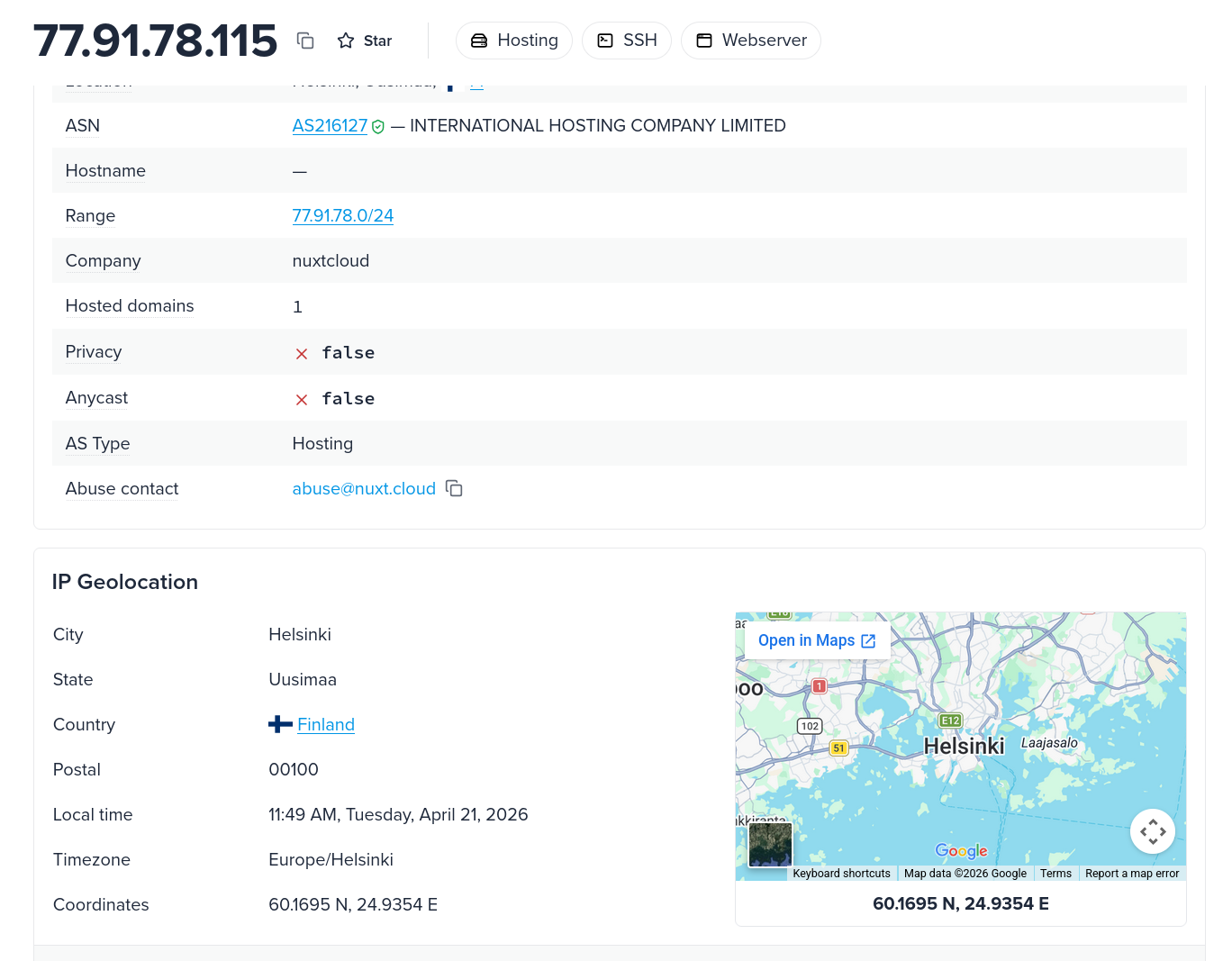
Geolocating the IP confirms the origin as Finland.
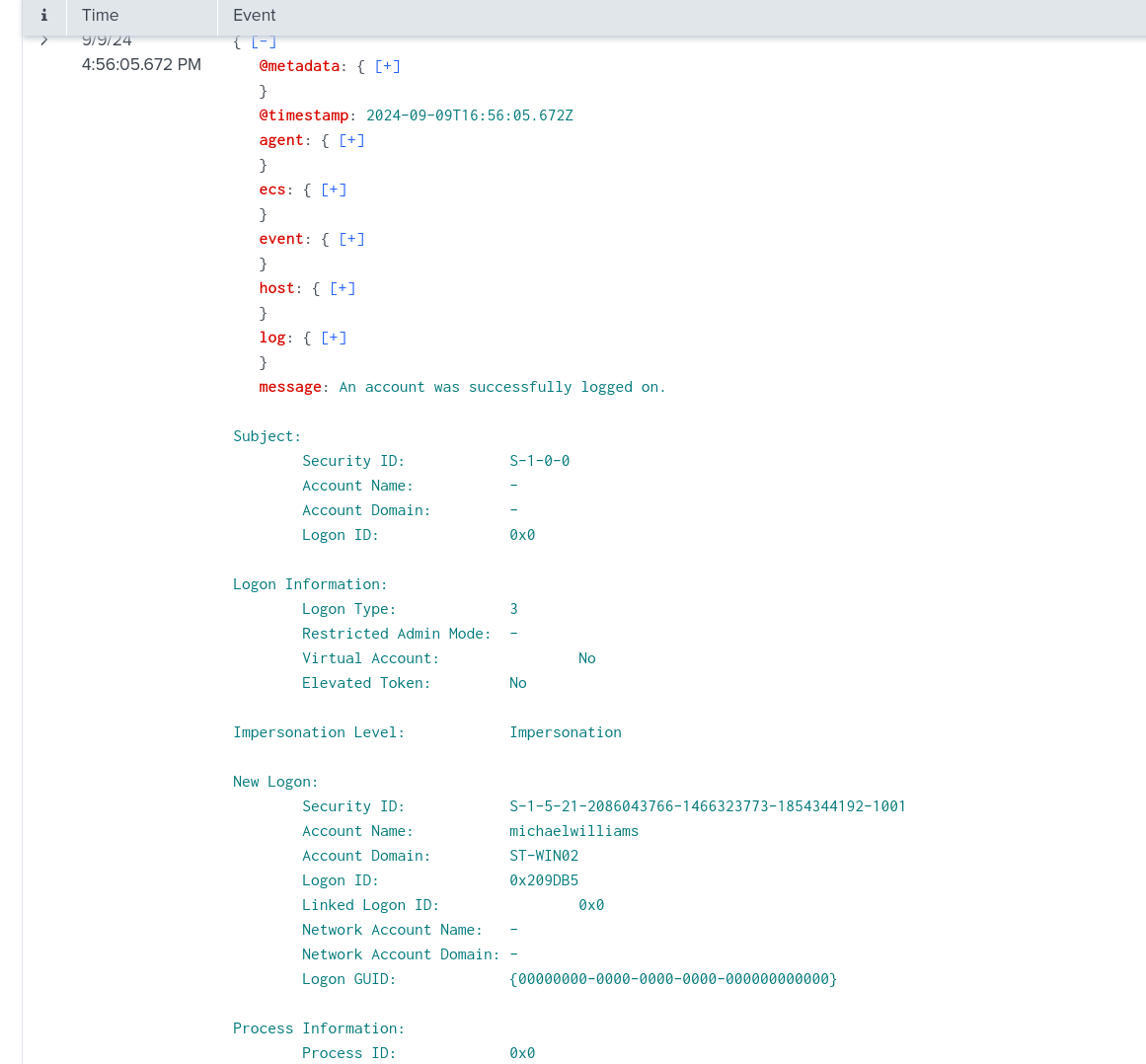
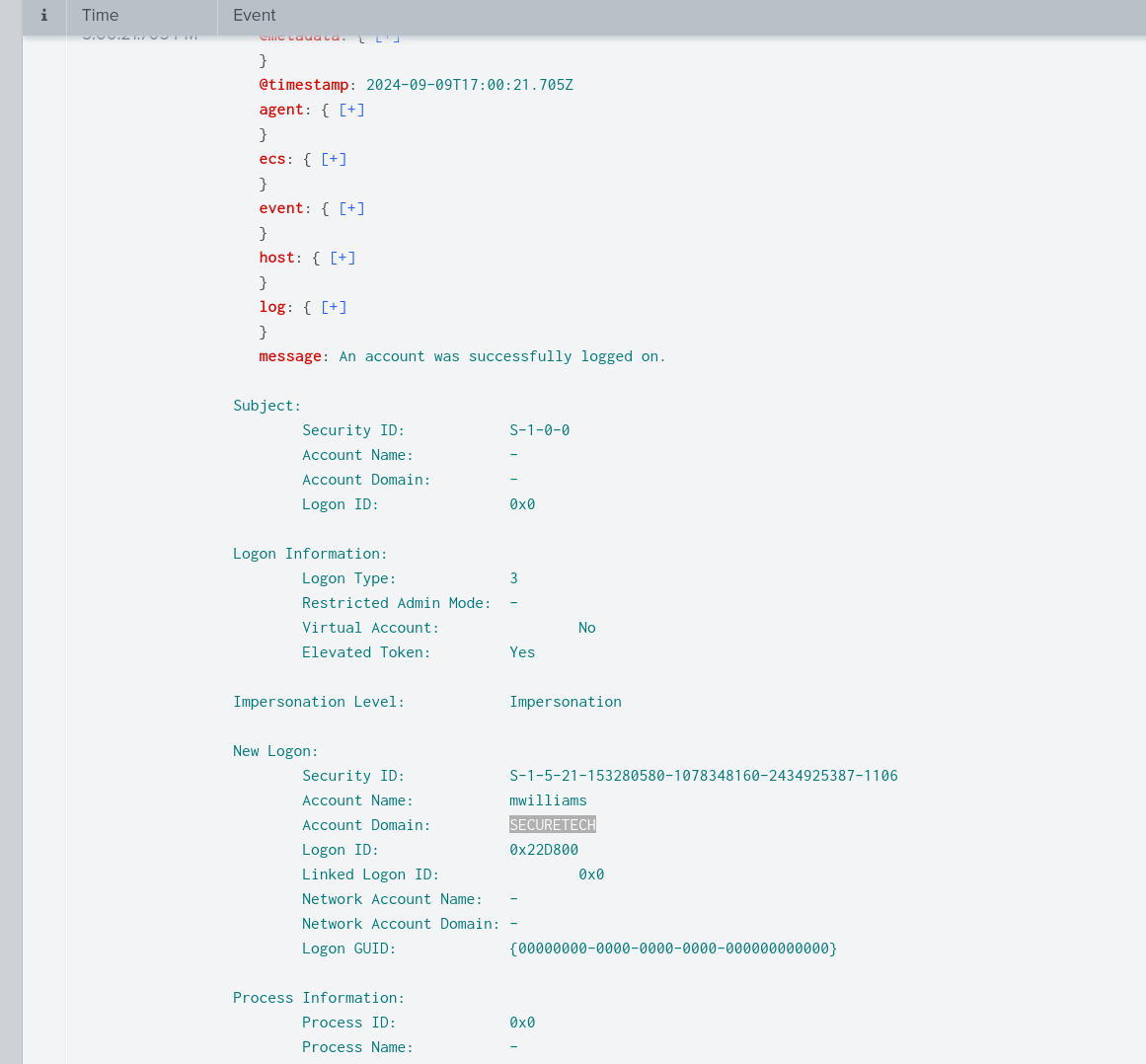
Initial Access — Password Spray
With the attacker IP identified, the investigation narrows to successful logon events originating from that address. Filtering on winlog.event_data.IpAddress: 77.91.78.115 with Event ID 4624 (successful logon) reveals the authentication timeline.
The first hit is a local account login — michaelwilliams — which appears to be a low-privilege local account. The more significant event follows shortly after: a domain account logon for SECURETECH\mwilliams, confirming the attacker successfully authenticated to the domain.
The RC4-HMAC encryption type (0x17) observed in Kerberos ticket requests at this stage is a known indicator of password spray and Pass-the-Hash activity — modern environments should be using AES encryption. Querying Event ID 4769 confirms the environment is using legacy RC4-HMAC across the board.
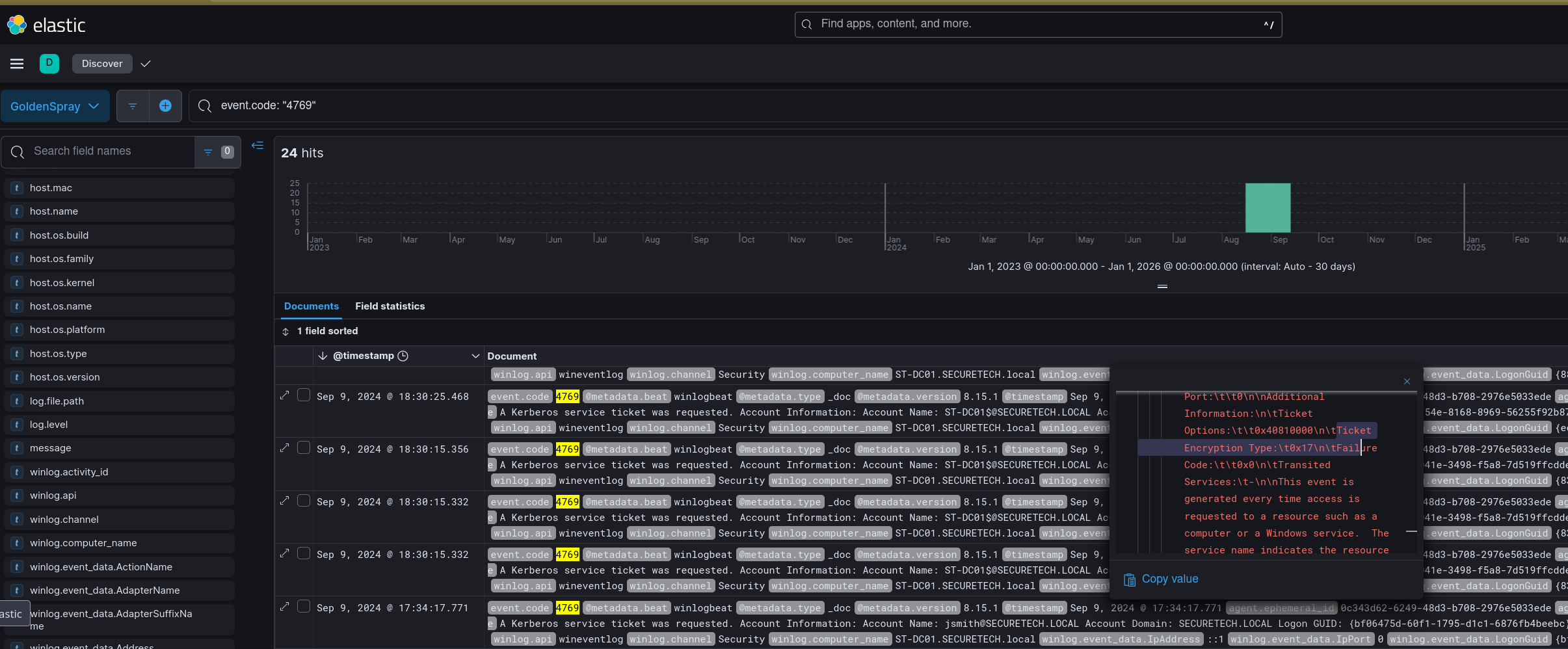
RC4-HMAC (0x17) maps to a legacy Kerberos encryption type that is exploitable for Kerberoasting and Pass-the-Hash — a significant environmental weakness that facilitated this attack.
Execution — Tooling Deployed
With a foothold established as mwilliams, the attacker transferred a red team toolkit to the host. Pivoting to Sysmon file creation events (Event ID 11) and filtering by TargetFilename reveals a zip archive was extracted to:
C:\Users\Public\Backup_Tools\
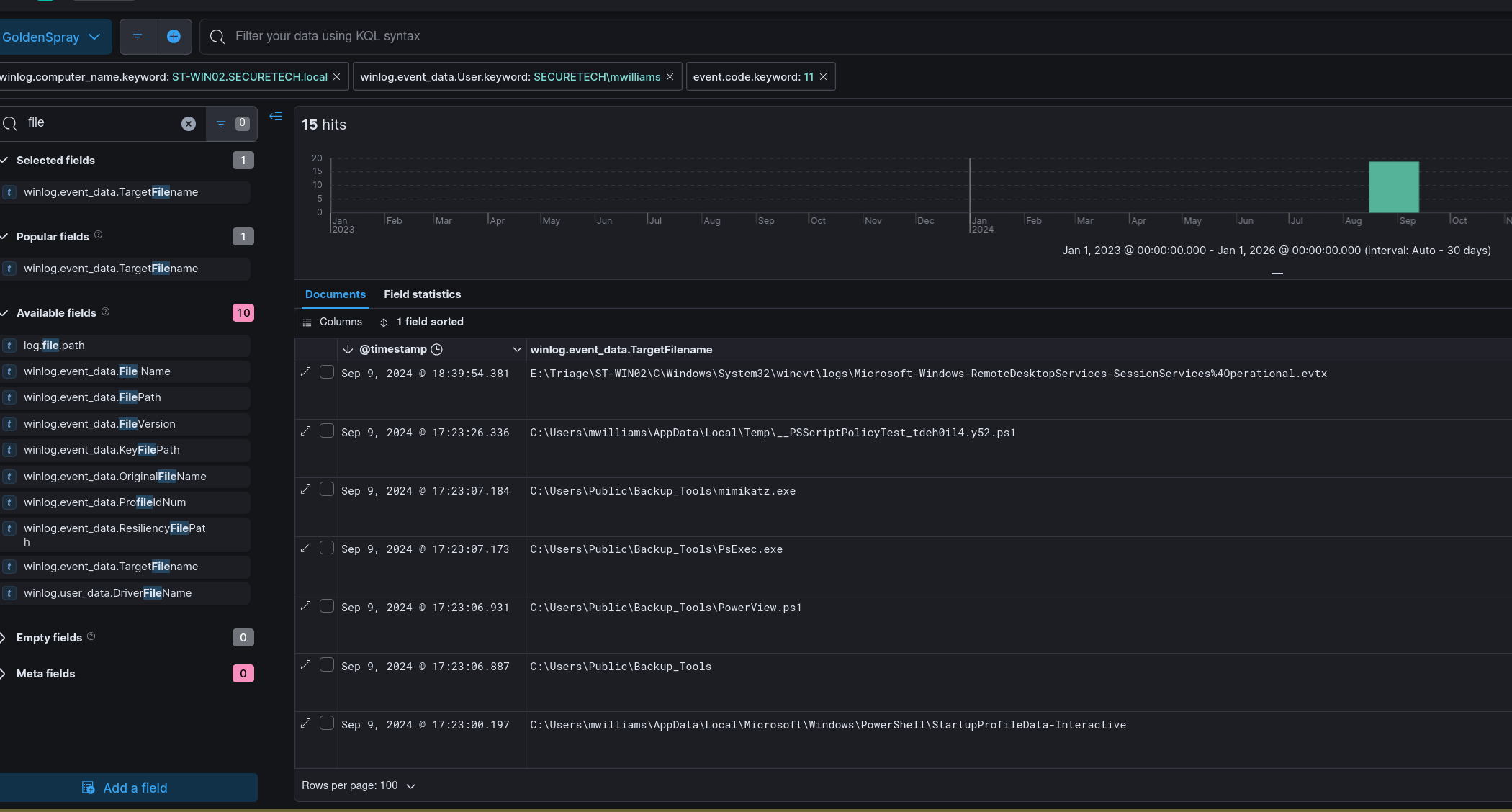
The directory contains PowerView.ps1, PsExec.exe, and mimikatz.exe — a standard post-exploitation toolkit covering recon, lateral movement, and credential access respectively. A separately named binary OfficeUpdater.exe is also present, masquerading as a legitimate update utility.
Persistence — ST-WIN02
OfficeUpdater.exe is the persistence mechanism on ST-WIN02. The masquerading name is deliberate — a process or scheduled task calling OfficeUpdater.exe from C:\Users\Public\Backup_Tools\ blends into process listings without immediate suspicion.
Credential Access — Mimikatz
With tools staged, the attacker executed mimikatz to dump credentials from LSASS. Filtering for Event ID 1 (Sysmon process creation) and searching for mimikatz returns the execution event with process ID 3708.
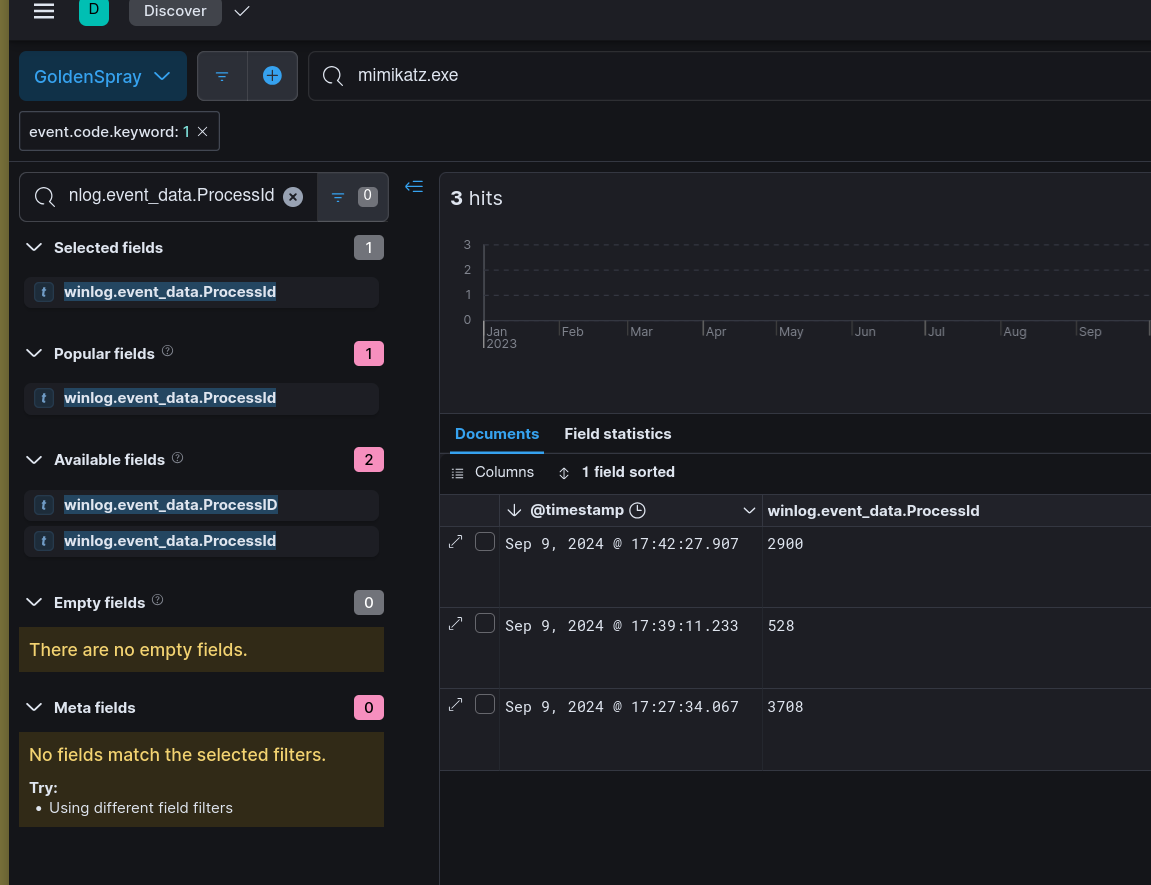
Dumping LSASS via mimikatz gives the attacker plaintext credentials and NTLM hashes for any accounts cached on the host — including domain accounts, which enables lateral movement without needing to crack anything.
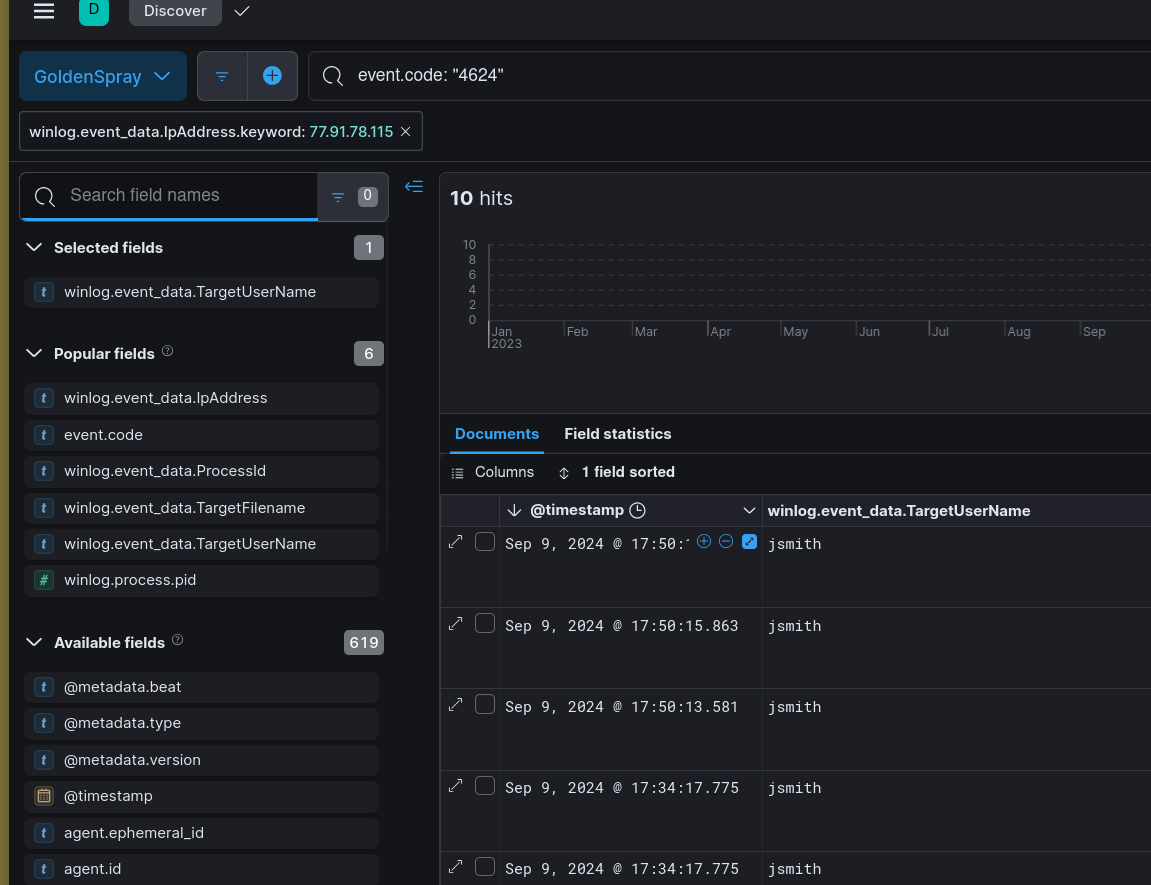
Lateral Movement — jsmith
With credentials from the LSASS dump in hand, the attacker moved laterally to a second host authenticating as SECURETECH\jsmith. Filtering on Event ID 4624 and correlating logon type and source IP confirms the jsmith account was used for the lateral move.
Persistence — Domain Controller
On the domain controller, the attacker created a scheduled task for persistent access. Event ID 106 (Task Scheduler — task registered) surfaces the task name:
filescheck
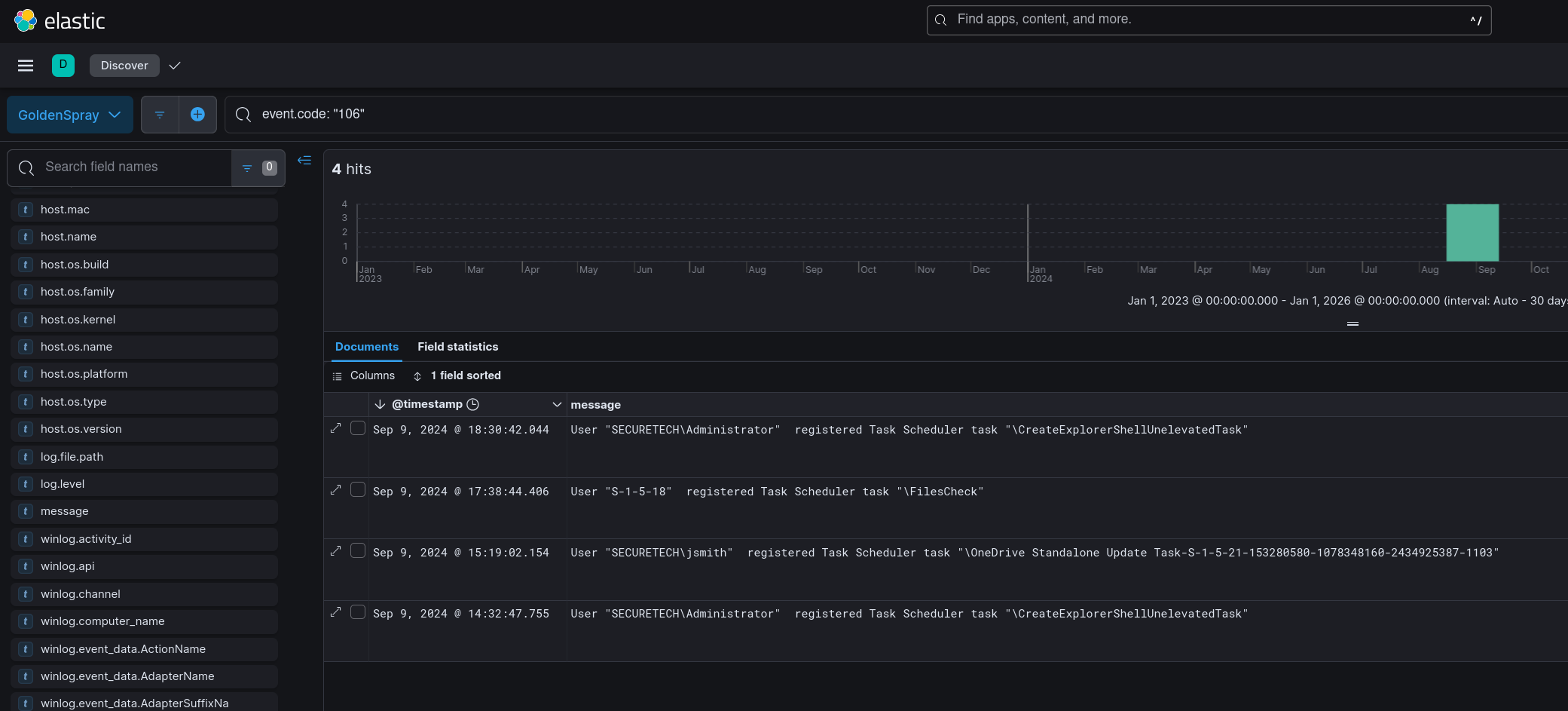
A scheduled task named filescheck on a DC is inconspicuous enough to survive a casual review — legitimate-sounding names are a standard attacker technique when creating persistence on high-value targets.
Exfiltration Preparation
Prior to exfil, the attacker staged collected data into a zip archive:
C:\Users\Public\Documents\Archive_8673812.zip
The randomised numeric suffix on the archive name is consistent with automated staging scripts that generate unique filenames to avoid collision and complicate forensic correlation.
Attack Summary
| Phase | Action |
|---|---|
| Reconnaissance | Password spray from 77.91.78.115 (Finland) targeting domain accounts |
| Initial Access | Successful authentication as SECURETECH\mwilliams via sprayed credentials |
| Execution | Red team toolkit unzipped to C:\Users\Public\Backup_Tools| |
| Persistence (Workstation) | OfficeUpdater.exe dropped on ST-WIN02 masquerading as update utility |
| Credential Access | mimikatz (PID 3708) dumped LSASS credentials on ST-WIN02 |
| Lateral Movement | Authenticated as SECURETECH\jsmith to domain controller |
| Persistence (DC) | Scheduled task filescheck registered on domain controller |
| Collection | Data staged to C:\Users\Public\Documents\Archive_8673812.zip |
IOCs
| Type | Value |
|---|---|
| IP (Attacker) | 77[.]91[.]78[.]115 |
| Country | Finland |
| Account (Initial) | SECURETECH\mwilliams |
| Account (Lateral) | SECURETECH\jsmith |
| Tool Path | C:\Users\Public\Backup_Tools| |
| File | OfficeUpdater.exe |
| File | mimikatz.exe |
| File | PsExec.exe |
| File | PowerView.ps1 |
| Scheduled Task | filescheck |
| Archive (Staged) | C:\Users\Public\Documents\Archive_8673812.zip |
| Kerberos Encryption | RC4-HMAC (0x17) |
MITRE ATT&CK
| Technique | ID | Description |
|---|---|---|
| Password Spraying | T1110.003 | Domain accounts targeted from single external IP |
| Valid Accounts | T1078 | mwilliams and jsmith credentials used for access and lateral movement |
| Ingress Tool Transfer | T1105 | Red team toolkit transferred to C:\Users\Public\Backup_Tools| |
| Masquerading | T1036.005 | OfficeUpdater.exe named to blend into process listings |
| OS Credential Dumping: LSASS Memory | T1003.001 | mimikatz (PID 3708) dumped LSASS on ST-WIN02 |
| SMB/Windows Admin Shares | T1021.002 | PsExec used for lateral movement to domain controller |
| Scheduled Task | T1053.005 | filescheck task registered on domain controller for persistence |
| Kerberoasting | T1558.003 | RC4-HMAC (0x17) encryption indicates legacy Kerberos exploitable for roasting |
| Archive Collected Data | T1560.001 | Data staged to Archive_8673812.zip prior to exfiltration |
Defender Takeaways
Disable RC4-HMAC for Kerberos — The presence of 0x17 encryption across the environment is a significant gap. Enforcing AES-256 Kerberos encryption domain-wide removes the precondition for Kerberoasting and reduces Pass-the-Hash viability. This is a group policy change that should be prioritised in any domain still running legacy encryption.
Alert on LSASS access by non-system processes — Sysmon Event ID 10 (process access) targeting lsass.exe from a process in C:\Users\Public\ is a near-certain malicious signal. A detection rule scoped to LSASS access from user-writable directories is high-fidelity and low noise.
C:\Users\Public\ as a staging indicator — Legitimate software does not install to C:\Users\Public\. Any process creation or file write event originating from this path warrants immediate investigation. A Sysmon rule alerting on new executables created under C:\Users\Public\ would have caught the toolkit deployment before any credentials were dumped.
Scheduled task monitoring on domain controllers — Event ID 106 on a DC should generate an alert by default. Tasks registered on domain controllers outside of a change window are high-priority events — filescheck is exactly the kind of low-suspicion name an attacker uses to avoid scrutiny in a scheduled task list.
Password spray detection — A single external IP authenticating against multiple domain accounts in a short window is a textbook spray pattern. An alert on more than 5 failed logons across different usernames from the same source IP within 60 seconds would have flagged 77.91.78.115 before mwilliams was successfully compromised.