blue team operations
& SOC analysis
Documented investigations across SIEM platforms, BTL1 labs, and real-world alert triage. Every lab completed, documented, and linked — proof of active daily grind toward SOC operations.
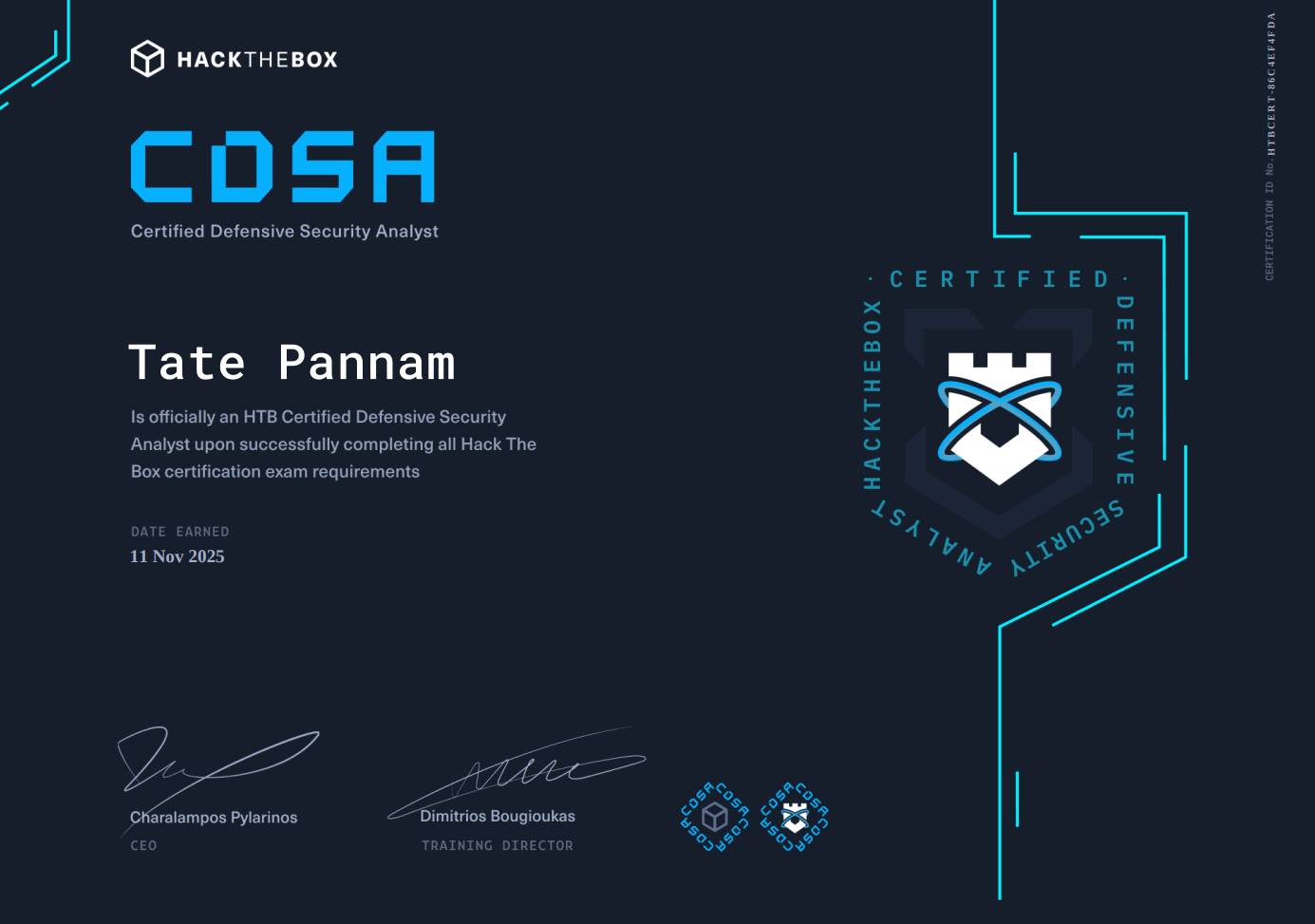
HTB proctored certification exam covering SOC fundamentals, alert triage workflows, SIEM analysis with Splunk & Elastic, threat intelligence & IOC correlation, digital forensics, incident response, phishing analysis, malware detection, and network traffic analysis.
- Phishing analysis & email header forensics
- SIEM threat detection & log correlation
- Network forensics & PCAP analysis
- Digital forensics & endpoint investigation
- Malware analysis & IOC identification
- Real-world SIEM alert triage
- Log analysis & correlation
- Malware investigation & IOC identification
- Incident documentation & reporting
- Threat intelligence integration
- SIEM alert triage & log correlation
- Network forensics & PCAP analysis
- Memory forensics & disk image analysis
- Threat intelligence & IOC attribution
- Incident response & malware investigation
- Memory forensics & volatile data analysis
- Disk image forensics & file recovery
- Malware triage & static analysis
- Threat actor attribution & TI correlation
- Advanced incident response workflows
- Alert triage & log analysis
- PCAP investigation & network forensics
- Defensive reasoning & escalation methodology
- Advent of Cyber 2025 — completed & certified
- Night Shift CTF — medium difficulty simulation
One real LetsDefend alert per day, triaged out loud on camera. Structured workflow, log correlation, containment decisions — real analyst thinking documented publicly.
Every alert triaged, documented, and mapped to MITRE ATT&CK. Updated daily as part of the Day N of Becoming a SOC Analyst series.
Every technique observed across labs and investigations mapped to MITRE ATT&CK Enterprise. Generated live from documented writeups — no manual curation.
Nine investigations selected across core blue team disciplines. Hard-rated labs, real artefacts, documented methodology.
All platforms, all labs. Filter by platform, difficulty, or category. Adding new labs weekly. BTL1: 1 of 9 completed.
Shorter CTF-style challenges. Same platforms, less depth.
- — investigations logged & counting
- — true positives · — false positives
- — unique MITRE ATT&CK techniques observed
- Latest: —
- 26 commands and growing
- Volatility · Splunk · Wireshark · Zeek
- Linked back to source lab for context
- Auto-extracted from investigation notes
- LetsDefend — 34 cases, 97% success
- TryHackMe — 46 cases, 100% detection
- GitHub — full writeup repository
- Real-time metrics & platform rankings